Abstract
Security supports are a significant factor in the design of security system in ad hoc networks. It is particularly important to protect the identities of individual nodes to avoid personal privacy concerns. In this paper, we propose a security system for ID-based anonymous cluster-based MANETs to protect the privacy of nodes. Moreover, we propose a threshold signature scheme without pairing computations, which diminishes the computation load on each node. To the best of our knowledge, our proposed security system is the first in which the pseudonym is combined with cluster-based mobile ad hoc networks (MANETs) without a trusted entity. According to our protocol analysis, our proposal satisfies most properties for an anonymous security system and effectively copes with dynamic environments with greater efficiency by using secret sharing schemes. Therefore, it could be usefully applied to preserve privacy in dynamic MANETs without a trusted entity, such as military battlefields, emergency areas, mobile marketplaces, and vehicular ad hoc networks (VANETs).
1. Introduction
MANETs support communications in situations involving temporary self-organization and infrastructure-less situations, such as battlefields, disaster relief situations, and emergency rescue areas [1]. Recently, MANETs have been extended to intelligent transport systems, often called VANETs. However, MANETs are subject to various types of attacks because of the wireless and infrastructure-less environments in which they are used. Moreover, these network structures make it difficult to apply the certificate-based public key cryptosystem (CBC) to meet the requirements of the certificate authority (CA). As a powerful alternative to the CBC, the identity-based cryptosystem (IBC) proposed by Shamir [2] has been gaining momentum in recent years. It allows public keys to be derived from entities' known identity information, such as e-mail addresses, IP addresses, or codes, thus eliminating the need for public key distribution and certificates. In other words, a user's public key can be determined directly from his identifying information, rather than having to be extracted from a certificate issued by a CA.
However, a centralized public key generator (PKG) which generates a key pair for users in the IBC would obviously be easy to attack, and accessibility could not be guaranteed at all times for all participants in MANETs. To counter this, Boneh and Franklin [3] suggested spreading the PKG by means of distributed PKGs (D-PKGs), using threshold cryptography. Distribution of a signing key and CA functionality over multiple nodes using secret sharing and threshold cryptography is a possible solution to this problem. Most studies in cluster-based MANETs considering D-PKGs have been based on hierarchy topology structures, which classify the node into two types, namely, representative nodes, called clusterheads (CHs), and common nodes.
Furthermore, the threshold signature scheme in MANETs has attracted many researchers' attentions recently [4]. The threshold signature achieves the purpose for many individuals to cooperatively sign the same document. Some schemes with trusted party are proposed and applied to CBC-based networks [5], while these are unreasonable to MANETs where there are no infrastructure and control administration. Therefore, the threshold signature scheme is necessary for secure message transmission in MANETs. A recent research on cluster-based MANETs has sought to address the privacy problem [6] and threshold signature schemes [7], but research on anonymous threshold signature schemes in cluster-based MANETs has been insufficient.
This paper proposes a security system for ID-based anonymous cluster-based MANETs to protect the privacy of nodes. Moreover, we propose a threshold signature scheme without pairing computation, which diminishes the computation load on each node in comparison with existing schemes. The major contributions of this study are summarized as follows.
Security of a cluster key distribution scheme and key agreement scheme. We propose a secure cluster key distribution scheme and a key agreement scheme with anonymity for cluster-based MAENTs. Cluster key distribution scheme ensures that the compromise of an arbitrary number of nodes outside the target cluster does not jeopardize the secrecy of noncompromised nodes. Key agreement scheme also ensures secure communication between nodes in intra- and interclusters. Consideration of threshold signature without pairing computation. Our threshold signature supports threshold signature. Comparing to existing threshold signatures, we diminish the computation load on signing nodes and a verification node; instead, CHs aid signature verification process. Thus, our threshold signature is suitable for the distributed PKGs architecture or the cluster-based network architecture. Protection of personal privacy. Our schemes support entity anonymity. Only the entities especially of the matched session can know the identity of others with whom they are in communication. For instance, CHs could be dealers, and common nodes could be purchasers when considering temporary established mobile markets. It is no needed to hide the CHs' identity because every purchaser should recognize CHs as dealers and their information; therefore, identities of CHs are not quite important. Besides, the information of purchasers is much attractive to adversaries because the information could be abusable commercially and criminally.
The rest of the paper is organized as follows. In Section 2, we present preliminaries, and the system model is presented in Section 3. In Section 4, we describe ID-based anonymous cluster-based MANETs, and the threshold signature is discussed in Section 5. Finally, we analyze the proposed scheme in Section 6 and conclude our findings in Section 7.
2. Preliminaries
In this section and we present notations, then define the cryptographic system and primitives used as building blocks in our security system.
2.1. Notations
Table 1 lists some important notations whose concrete meanings will be further explained where they appear for the first time.
Notations.

2.2. ID-Based Cryptography
Let Bilinear: for all Consequently, for all Nondegenerate: if P is a generator of Computable: there is an efficient algorithm to compute
Note that
Definition 1 (bilinear Diffie-Hellman (BDH) problem).
The BDH problem for a bilinear pairing
Definition 2 (decisional Bilinear Diffie-Hellman (DBDH) problem).
The DBDH problem for a bilinear pairing
2.3. Threshold Schemes Based on Secret Sharing
2.3.1. Shamir's
-SS
In Shamir's Share generation algorithm: dealer D does the following: dealer D first picks a polynomial D computes all shares: Then, D outputs a subset Secret reconstruction algorithm: based on a Lagrange interpolation, any subset

We note that the above scheme satisfies the basic security requirements of secret sharing schemes as follows: (1) with knowledge of a t or more than t shares, it can reconstruct the secret K easily; (2) with knowledge of fewer than
3. System Model
We describe the network architecture and the security requirements.
3.1. Network Architecture
We divide the networks into several clusters to enhance the efficiency and availability. The clustering is a method that enables nodes to be organized on the basis of their relative proximity to one another. We envision a cluster-based MANETs consisting of n CHs without any prior contact, trust, or authority relation. In each cluster, one distinguished node, the CH, is responsible for establishing and managing the cluster. The size of the network may change dynamically according to the efficiency and the security. Let us consider an ad hoc network with n CHs that are selected to enable secure and robust pseudonym generation. We assume that compromised CHs will eventually exhibit detectable misbehavior. Studies [10, 11] discussed ways to detect the misbehavior of nodes or intrusions in detail.
Our schemes work securely and properly on the assumption, which is similar to assumptions made in [12–14], that adversaries compromise no more than
Figure 1(a) illustrates the basic network architecture of our security system for cluster setup and pseudonym generation. CHs have secret sharing
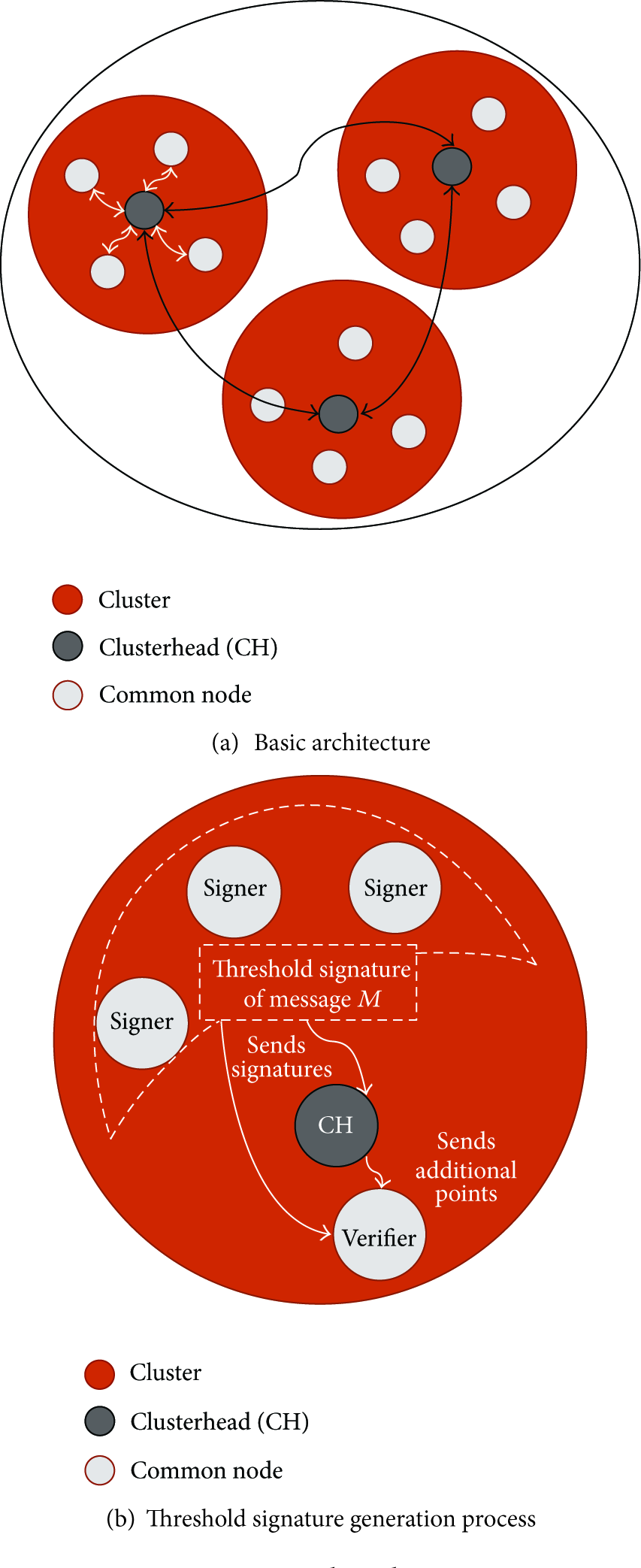
Network Architectures.
Figure 1(b) illustrates the threshold signature generation process in a cluster. Nodes that are member of the same cluster and try to send the same message generate a threshold signature and send the message with a threshold signature to a verifier and the CH. Then, the CH checks the validity of messages and signatures and generates and sends additional points to a verifier. Finally, a verifier checks the validity of signatures.
3.2. Security Requirements
We define security requirements for our anonymous security system.
Privacy: private information, such as the node's identity and location, should be protected against malicious adversaries. Formally, given two sets of legitimate identities, Traceability: compromised nodes are identified, and the corresponding identity and pseudonym should be revoked to protect networks against further threats. Nonmanipulation: no nodes or CHs can computationally manipulate a pseudonym from an identity. Verifiability: from the signature, the verifier can be convinced of the signer. Undeniability: once a signer creates a valid signature, he cannot repudiate the signature creation. Unforgeability: no nodes can forge a signature; it can only be replicated by the signer who creates it.
4. Anonymous Cluster-Based MANETs
4.1. System Setup
It is reasonable to assume that a trusted PKG could bootstrap the network, which itself is not a part of the resulting network. The basic operations consist of generating pairing parameters, private keys, and secret sharing.
Generation of the pairing parameters Generation of pairing parameters Generation of secret sharing for cluster key: to generate secret sharing for cluster key, the PKG does the following.
It submits identity information. A CH submits its identity information, It chooses cluster key. The PKG selects an arbitrary cluster keys It determines polynomials of degree It performs Parameters U, Generation of CH's ID-based private keys: to hand out CH's private key, the PKG does the following.
It submits identity information. A CH submits its identity information, It computes key pairs. The PKG computes a public/private key pairs: Parameters Generation of common nodes' ID-based private keys: to hand out node's private key, the PKG does the following.
It submits identity information. A common node submits its identity information, It computes key pairs. The PKG computes a public/private key pairs: Parameters
Due to the difficulty of solving the DLP in
4.2. Cluster Setup
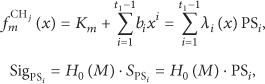
Cluster-based MANETs work without the help of PKG after completing the system setup. Instead of a PKG, CHs play this role using their secret sharing. In our security system, to provide security services to networks, each CH first generates respective polynomials, that cover within a cluster and a group secret key. Then, the CHs establish a secure channel with CHs or nodes to forward them. Secure channels are generated using their initial key pairs. Secure channels between CHs or between a CH and a node are established by the noninteractive key agreement scheme as follows:
Generate respective polynomials Pooling secret sharing. Every CH shares their secret sharing, Performing secret reconstruction algorithm. Each CH reconstructs the polynomial Generating respective polynomials of degree 

To avoid cryptanalysis and malfunction of CHs, frequent key updates are needed. Our key update schemes consist of two parts: one is an update of the cluster key, and the other is the respective polynomial. The cluster keys,
4.3. Generation of Pseudonyms
Pseudonym generation is an essential process to provide privacy of each node. Figure 1(a) shows a scenario of pseudonym generation process. Initial pseudonym generation starts when the registered nodes on the PKG try to get a pseudonym from an adjacent CH. The CH generates pseudonyms for common nodes within a cluster using its respective polynomial. Pseudonyms and secret sharing are generated as follows.
Generation of pseudonyms and key pair: to generate pseudonyms, CHs do the following. Performing Computing key pairs. Each CH computes a public/private key pairs: Recording pseudonyms. Each CH records the identities and the pseudonyms with the corresponding key pairs at the pseudonym lookup table (PLT). Forwarding pseudonyms, key pairs, and group secret key to corresponding nodes. CHs forward pseudonyms to nodes, respectively, using a secure channel.
Other CHs cannot know pseudonyms from public keys of nodes even though they have knowledge of cluster key 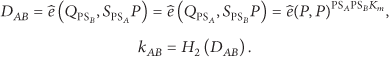
5. Threshold Signature in Anonymous Cluster-Based MANETs
We propose an anonymous threshold signature. The proposed scheme involves five roles: a clusterhead (CH), a set of members Generate threshold signature: to generate a threshold signature regarding message M, a number of Requesting threshold generation. The initiator, one of signers, sends a threshold generation request to the CH with a list of signers as Sending tokens. The CH chooses an arbitrary tokens Generating signature. Then, each signer generates a signature: Sending the signature and a pseudonym public key. Each node sends the message tuple to the verifier V and the Generate a verifying polynomial: to check the validity of signatures, the Check the validity of a set of messages. The Checking the validity of signatures. The Generating a verifying polynomial. If all messages and signatures are valid, the generating a verifying-polynomial. The generating points. The Generate verification: to check the validity of a signature, the verifier does the following. Performing secret reconstruction algorithm. The verifier performs a secret reconstruction algorithm using points Checking the validity of HMAC. The verifier checks the validity of HMAC using received




6. Analysis
In this section, we provide analysis of our system with respect to correctness, performance, and security.
6.1. Correctness
Note that
Therefore, a CH can verify the validity of each signature as follows:
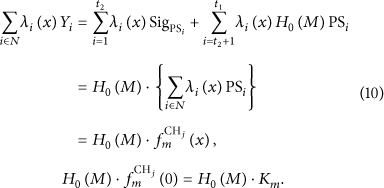
The verifier also can check the validity of threshold signature as above, similarly, because
6.2. Performance
This section presents our efficiency analysis. Table 2 compares our proposed schemes with other schemes. For simplicity, we omit private key distribution and secret sharing distribution process in comparison to computation load.
Comparisons among other ID-based threshold signature schemes.

∘ denotes the scheme, and considers the property; × denotes the scheme and does not consider the property;
Most schemes use pairing algorithm to generate and verify the signature except the proposed scheme. The pairing algorithm and the exponentiation generally consume heavy computation loads rather than scalar multiplications. Cao et al. [15] showed a pairing that consumes about double computation load with those of an exponentiation and three times computation load with those of scalar multiplication in
6.3. Security
6.3.1. Privacy
Our security system supports the anonymity of nodes using pseudonyms. In our proposed security system, every node does not reveal real identities after the pseudonym generation. An adversary cannot correctly match an identity with a pseudonym even though the identity and the pseudonym are released to them because of the hardness of DLP [17]. The pseudonym is in the form of
6.3.2. Traceability
Each CH records the relation of the identity and the pseudonym of common nodes in its cluster at the PLT. Pseudonyms of compromised and revoked nodes are rejected from the PLT, and these nodes cannot be updated any more. Therefore, our system enables the tracing of violators when unlawful actions are notified to the CH, and they are eventually isolated from the network.
6.3.3. Nonmanipulation
Our proposed security system ensures nonmanipulation in case of at most (
6.3.4. Verifiability, Undeniability, and Unforgeability
The CH works as a subverifier in our threshold signature scheme by generating a verifying polynomial. From message tuples from signers, the CH can check the validity of signers. First, only valid and registered nodes could generate correct HMAC with its pseudonym. Second, the CH could verify signatures by reconstructing a polynomial
6.3.5. Forward/Backward Secrecy
Our security system supports the forward/backward secrecy using key update scheme in case of at most (
7. Conclusions
Concerns for personal privacy and security in wireless environments are increasing rapidly as mobile devices are becoming more popular. Cluster-based MANETs are being seriously considered to pioneer new markets; however, there are urgent unresolved security problems. Fundamental aspects of security, such as authentication and signature, are challenging for secure security systems for cluster-based MANETs. In addition, the protection of personal privacy has become increasingly important as the wireless networks have become personal and popular; therefore, secure security system designs with anonymity are required for cluster-based MANETs.
In this paper, we presented a secure security system with anonymity for cluster-based MANETs and a threshold signature under practical assumptions. To the best of our knowledge, our proposed security system is the first in which the pseudonym is combined with cluster-based MANETs without a trusted entity. According to our protocol analysis, our proposed system satisfies most properties for an anonymous security system and successfully copes with dynamic environments with greater efficiency by using secret sharing schemes. We believe that the proposed system improves upon the security of previously proposed security systems, and that it is suitable for a wider variety of applications. It could be usefully applied to preserve privacy in dynamic MANETs without a trusted entity, such as military battlefields, emergency areas, mobile marketplaces, and privacy-preserving VANETs.
Footnotes
Acknowledgments
This paper was supported by the Basic Science Research Program through the National Research Foundation of Korea (NRF) funded by the Ministry of Education, Science and Technology (2012R1A1A4A01002603) and was supported by the Kyungpook National University Research Fund, 2012.
