Abstract
The communication between cell phones and sensor networks involves strong user authentication protocols to ensure the data and network security. Generally, in order to obtain the relevant information, cell phones interact with sensor networks via gateways. In 2009, according to Arjan Durresi and Vamsi Paruchuri scheme, this unique ability is used to provide better authentication and security protocols that can be used to establish secure communications among cell phones and sensor networks. In this paper, we show that their scheme is vulnerable to known attacks such as man-in-the-middle attack and reply attack, and it does not provide mutual authentication between gateway node and cell phone. In addition, it does not establish session key after the authentication phase. To fill this security gap, we proposed security patches and improvements, which overcome the weak features in the scheme of Arjan Durresi and Vamsi Paruchuri. Finally, we came out with results which show that our improved security patch establishes trust between the cell phone and gateway in the form of mutual authentication and provides the session key establishment after the authentication phase.
1. Introduction
With the recent advances in information and communication technology, the wireless sensor networks (WSNs) have attracted an increasing interest from researchers due to its ubiquitous nature. Wireless sensor networks (WSNs) are normally deployed in an unattended environment to collect the data which are transmitted to the base-station traversing some nodes via RF signals and routing schemes. In general, most of the queries in WSN applications are issued at the points of base stations or gateway (GW) nodes of the network. However, due to the wireless nature of sensor node it may be possible that a user can access sensor data directly without involving the gateway. Thus, user authentication is a primary concern in this resource-constrained environment before accessing data from the sensor/gateway nodes. WSNs are widely used in areas such as military, battlefield, homeland security, healthcare monitoring, agriculture and cropping, manufacturing, and measurement of seismic activity, and so forth. Every sensor node has some level of computing power, limited storage, and a small communication module to communicate with the outside world over an ad hoc wireless network [1]. Thus far authentication protocols schemes have been proposed on the link layer [2–5] and the network layer [6], and they provide sufficient security in the wireless sensor networks. Meanwhile, protocols based on user authentication on the application layer in [7–10] have been proposed where the secrets are stored into the gateway node or base station. In that case, when a user wants to access data through the gateway node or base station, he is authenticated those protocols. Through cellular network, user can access gateway of wireless sensor networks and get the data he wants to access. Cell phones are ubiquitous and have a low power transceiver that communicates with the base stations that are typically located on a distance of a few miles. There are many applications which would greatly benefit from using cell phones in the ad hoc mode. Collecting data from a gateway by a cell phone, needs an authentication protocols are needed to prevent a malicious cell phone user from misguiding other users [11].
In 2009, Durresi and Paruchuri [12] proposed architecture among the cellular network and wireless sensor networks with protocols to establish secure communication. According to their scheme, the gateways are connected to an authentication server (AS), and each sensor network has its own AS in charge of their security. A central server (CS) that interacts with all ASs and cell phones is required. The CSs communicate with cell phones through the existing cellular network only to exchange control and security information. The data communication between cell phones and sensor networks (gateways) is done through ad hoc channels. The control of the security across all the sensor networks is done by the CS, and it could be distributed. To utilize the advantages of both cell phones and sensor nodes, the use of gateways nodes was proposed. These nodes act as sinks for sensor networks to obtain and aggregate the relevant information sensed by the sensor network. Gateways act also as intermediates through which the cell phones get information from sensor networks. Cell phones can communicate with cellular network and sensor networks at the same time. They claimed that this unique ability is used to provide better authentication and security.
Unfortunately, this paper finds that Arjan et al.'s scheme is susceptible to information leakage attack, to man-in-the-middle attack, reply attack, and no mutual authentication between the cell phone and the gateway, and no session key is established between the cell phone and the gateway node at the end of the authentication phase.
The rest of the paper is structured as follows. Section 2 briefly reviews Arjan et al.'s schemes. Section 3 elaborates on the weaknesses and security pitfalls of his scheme. Section 4, presents our improved security patch over Arjan et al.'s scheme. Section 5 reveals the performance analysis of the presented scheme and Section 6 concludes this paper.
2. Review of Arjan et al.'s Scheme
In this section, we review Arjan et al.'s schemes. The first scheme uses asymmetric key cryptography, whereas the other scheme use symmetric key cryptography between cell phones and gateways.
2.1. Review on Using Secure Infrastructure and Asymmetric Cryptography Scheme
The first scheme of Arjan et al. is using the identity-based cryptography (IBC) to provide a secure connectivity. According to their architecture, each sensor node has a private key generator (PKG) which is part of the authentication server. The notations used throughout this paper are given in Table 1.
Notations and descriptions.

The system model of Arjan et al.'s architecture is defined by different components as follows:
cell phones (CP) cellular base station (CBS) central server (CS) authentication server (AS) sensor networks gateways (G).
The proposed architecture by Arjan et al. is shown in Figure 1, and they claimed that it supports secure communication among cell phones and sensor networks.
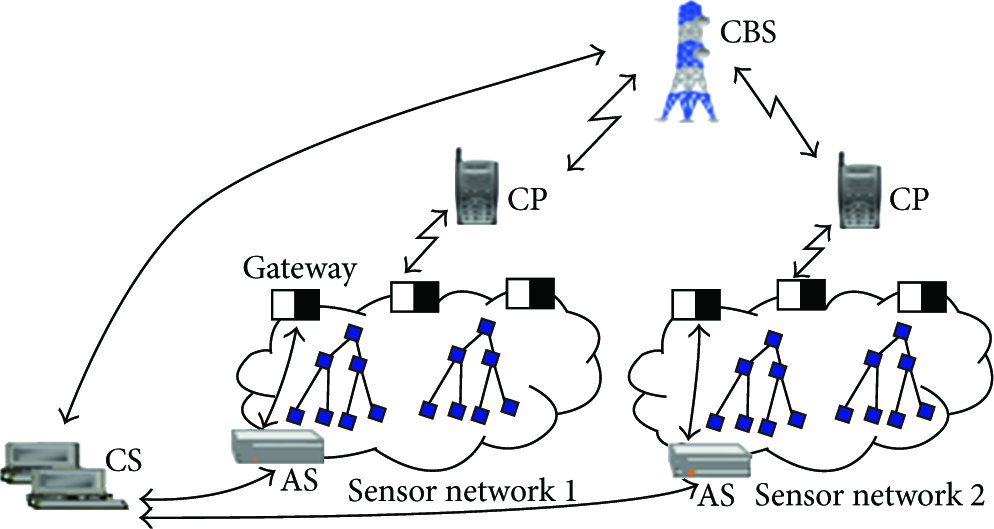
Arjan et al. network architecture.
In Figure 1, the CP does not communicate directly with the sensor network. It has first to be requested from the CS a PKPKG of that particular sensor network. The CS generates the
Initially the CP interacts with the CBS, and after the CP is authenticated by the BCS, a session key 


2.2. Review on Using Secure Infrastructure and Symmetric Cryptography Scheme
This scheme uses symmetric cryptography to provide secure links between CP and gateways. The CP shares keys with gateways. If the cell phone wants to communicate with a sensor network, it sends the
The CS interacts with AS of that sensor network to obtain a set of secrets key for the CP. The AS also distributes each key of the set to some gateways. The CP broadcasts its 

Now, the CP has the 


The gateway with the shared pairwise key sends a random challenge with its ID encrypted with the key
3. Cryptanalysis and Weakness of Arjan et al.'s Schemes
Initially the cell phone interacts with the cellular base station. The cell phone is authenticated by the cellular base station and a session key
However, their scheme presents a gap of weakness security as follows.
Information leakage attack: as an alternative, the attacker can perform a man-in-the-middle attack [15] (enter between the cell phone and the cellular base station by using a malicious cell phone and fake cellular base station), such that all the messages pass through the attacker. During the authentication phase between the cell phone and the cellular base station, only the cell phone is authenticated to the cellular base station while there is no mechanism to authenticate the cellular base station to the cell phone. Then, any adversary can perform the man-in-the-middle attack. Replay attack: the attack occurs when an adversary intercepts the message (3) and (7) (i.e., if the attacker accesses the SIM card of the legitimate user) and replays it, he might impersonate the gateway to be a real cell phone using an authenticated session key unless the gateway remembers indefinitely all previous sessions keys used with the cell phone. Here, Arjan et al.'s scheme, does not provide any mechanism to prevent the re-use of olds sessions keys. The gateway responds to the adversary's query, and CP-adversary, who is an adversary and not a legitimate user of the sensor network system, finally, he enjoys the resources as an authorized user without being a member of the system. Session-key establishment: Arjan et al.'s scheme does not establish the session key between the cell phone and the gateway after authentication phase. After successful user authentication, the involved parties should establish a session key, so that subsequent messages could transmit securely. Thus, Arjan et al.'s scheme fails to establish the session key after user authentication phase.
4. Proposed Security Improvements
4.1. Protection against Man-in-the-Middle-Attack
To resist to the man-in-the-middle attack, we propose to use 3G instead of 2–2.5G networks. In GSM authentication only user authentication to the network is provided. To come out this weakness we propose to use 3G network where [16] both network and cell phone can authenticate each other. Thus the mutual authentication is well performed and can avoid against a man-in-the-middle attack.
4.2. Protection against Reply Attack with Mutual Authentication between Cell Phone and Gateway
It was identified in Section 3(ii) that there is a possibility of a replay attack in Arjan et al.'s scheme. The reason of the possibility of the replay attack is due to the absence of mechanism to prevent the re-use of olds sessions keys. In the case of an adversary can capture the messages (3) and (7), can replay them and access to the resources of the sensor networks. To overcome to this security flaw, we propose to use nonce and timestamp for mutual authentication between cell phone and gateway. Arjan et al.'s scheme can be amended by Table 2.
Notations and descriptions.

Before detailed discussion of the proposed scheme, some assumptions are made and are not supposed to be violated while executing the scheme. The assumptions are mentioned below.
The CP is registered to the AS via CBS using 3G technology. The AS assigns the Using a secure communication channel, the AS assigns
The authentication phase (AP) is invoked when the cell phone wants to login the WSN and access data from the gateway with the followings steps.
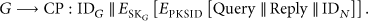
4.2.1. Using Secure Infrastructure and Asymmetric Cryptography Scheme
AP-1. The cell phone generates a secret number
AP-2. Upon receiving message (3) from the cell phone, the gateway decrypts it and performs the followings actions.
The gateway G validates the time The gateway verify if The gateway generates a secret number
AP-3. After receiving the reply message (4) from the G, the CP performs the following actions.
checks if The CP decrypts the message with its private key and check if The CP obtains Now, the CP sends the last message
AP-4. While receiving the message It computes the session key and decrypts the sub message, obtains Furthermore, the cell phone and the gateway node share the session key
4.2.2. Using Secure Infrastructure and Symmetric Cryptography Scheme
To enhance to security in Arjan et al.'s scheme using symmetric cryptography, the same assumptions are taken in considerations. The authentication phase (AP) is invoked when the cell phone wants to login the WSN and access data from the gateway with the followings steps.
AP-1. CP generates a secret number 
AP-2. The gateway which shares the pairwise key will interact with the cell phone with the actions below.
The gateway G checks if The gateway generates a secret number
AP-3. While receiving the message (11), the CP decrypts the message and performs the followings.
The CP validates the time The CP verifies if Then, the cell phone calculates the session key to respond to the challenge

AP-4. Upon receiving message (12) from the cell phone, the gateway computes the message and decrypts the sub message to retrieve the session key and check if
Finally, the cell phone and the gateway shares the session key
5. Performance Analysis of Proposed Scheme
In this section, we summarize security features and performance analysis of our proposed scheme and compare its security features and robustness with the scheme of Arjan et al. The performance analysis demonstrates that our scheme is more secure and robust than the scheme of [12], and achieves more security features, which were not considered in the aforementioned scheme. In addition a comparison with recent secure communication in WSN with our proposed protocol is done for the sufficient qualities.
5.1. Security Analysis
Mutual authentication between the CP and the CBS: our scheme proposes to use 3G instead of 2–2.5G networks. The GSM authentication mechanism is only one way; therefore, the user is not given the assurance that he has established a connection with an authentic serving network. With 3G technology, there is the assurance that authentication information and keys are not being re-used (key freshness). Mutual authentication between the CP and the G: in message (3) AP-2, the gateway verifies if the ID of the CP is the real one got from the AS, also the cell phone checks if Man-in-the middle attack: in message (3), if an attacker intercepts Reply attack: in this case, an attacker can steal the SIM card of the user of the cell phone and puts it in its cell phone. In this case, the attacker can use the Session key establishment: a session key,
As illustrated in Table 3, it is obvious that the proposed scheme is a secure user authentication protocol and provides more security services than Arjan et al.'s scheme.
Functionality comparison.

5.2. Performance Comparison among Existing Protocols
Recent researches have been conducted in WSN communication, and results show that they are efficiently secured in terms of computation cost and communication cost. Different existing schemes [17–23] have been analyzed in their communication protocols for the whole communication and confirmation of all entities (i.e., user, gateway, and sensor). In some cases all entities exchange messages or some of them only can exchange messages. In all cases, we carefully took in consideration the behavior of each protocol so that we can see how our protocol is efficient. Let us set
Performance comparison with related protocols.

N/A: not applicable; ME: messages exchanges.
The results from Table 4 show that the proposed protocol in the authentication phase (with authentication verification and mutual authentication) requires
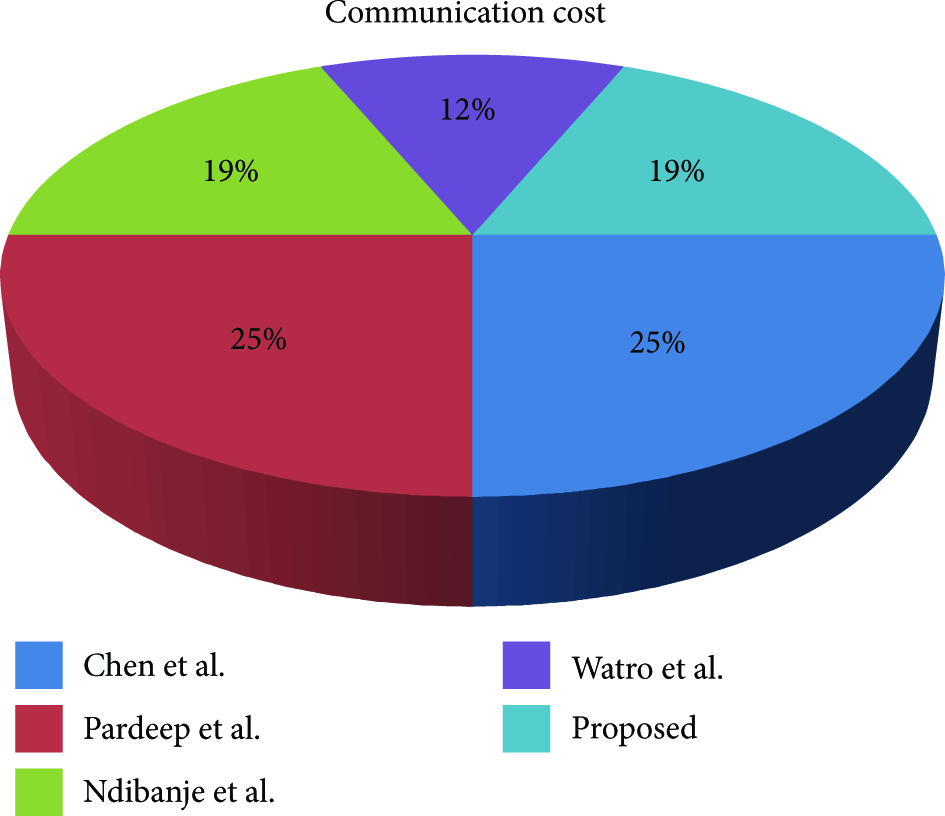
Figures 2 and 3 show the total time complexity of hash function and computation cost of cryptosystem respectively, while Figure 4 describes the total messages exchanges for the whole communication and confirmation of all entities used in the protocols aforementioned.
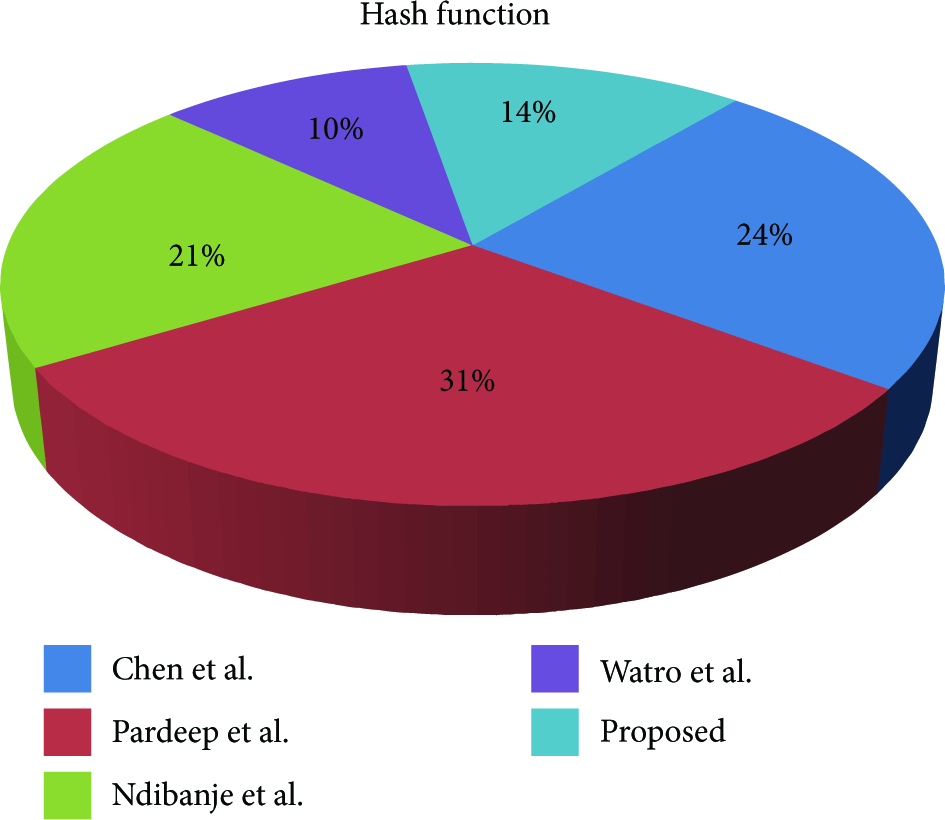
Total time complexity (hash function).

Total computation cost (symmetric cryptosystem).
Total messages exchanges for whole communication.
6. Conclusion
In real time, as a cell phone user can access data from gateway trough wireless sensor network; it is imperative to control data accessibility with strong user authentication protocols. In this regard, we have proposed enhancements to the scheme of Arjan et al. which suffers from Information leakage attack, does not provide mutual authentication between gateway node and cell phone, not able to establish session key after the authentication phase and it is susceptible to reply attack. To remedy the aforementioned flaws, we have proposed security patches and improvements, that overcome the weak features of Arjan et al.'s scheme and can be incorporated in their scheme for a more secure and robust authentication protocol in WSNs. Hence, through analysis, we came out with the conclusion that in our enhanced proposed improvement, the cell phone authenticates the gateway and both parties can trust on the authenticity of each other.
Footnotes
Acknowledgments
This work was supported by Dongseo University, “Dongseo Frontier Project” Research Fund of 2009. It was also supported by the National Research Foundation (NRF) 2012 Project (Grant no. 2012-0008447).
