Abstract
It is very important to protect the copyright of digital images in wireless transmission, because people often use a smart phone in their daily life. Traditional security schemes are computationally expensive, and they introduce overhead, which shortens the life of the image sensors. In this paper, we present an Improved Matrix Encoding (IME) scheme for hiding data into a two-color binary image. Our proposed scheme improved the CPT scheme. In the CPT scheme, each block F of
1. Introduction
The fundamental requirements of Wireless Sensor Network (WSN) in sensitive areas are a secure [1–9] image transmission. Unlike the wired networks, it is highly possible for attackers to access sensor data via wireless networks. Authentication preservation with sensors and related applications is an important research field in recent years [10–13]. Data hiding can be used for copyright, annotation, and communication and can be achieved by altering some nonessential pixels in the cover image. For example, in a given color image (including grayscale images), the least-significant bit (LSB) of each pixel can be changed to embed the hidden data. However, two-color images (including binary and halftone images) are very sensitive, as they can easily be detected by the human visual system. For stego images, one of the most challenging problems is hiding the secret data into binary images with a high ratio of secret data and low image distortion. Lower distortions of pixels in an image make it possible to resist steganalysis by the human visual system (HVS) [14].
Until now, there has been much research about data hiding based on binary cover images. Such research can be divided into four categories. The first category is pixel-wise: in this method, pixels can be chosen randomly [15]; therefore, the quality of the stego image is not good. In order to improve this problem, Kim [16] and Mei et al. [17] proposed improving the method based on some visual impact measures. The second category is pairwise: Tsai et al. [18] proposed this method based on pairwise logical computation (PWLC). The third category is block-wise: cover images are divided into blocks and modified by some characteristics of each block, including key and weight blocks. Some papers suggest changing the parity (or the quantization) of the number of black pixels in each block (Wu and Liu) [19], while others suggest flipping one specific pixel in the block [20, 21]. Finally, the fourth category is histogram: this method can be used for recovering the original image from the stego image using a histogram of an image. The histogram-based method was researched based on grayscale cover images. Guorong et al. [22] were the first to try to hide data in a binary image based on histogram. Ho et al. [23] later proposed a novel method for reversible data hiding and solved the problem of PWLC (i.e., binary image noise).
The CPT (Chen, Pan, and Tseng) scheme [24] was the first scheme based on the block-wise technique. This scheme is a good method for high-rate embedding of good-quality images. CPT is based on the pixel block scheme (its embedding rate is
In general, the evaluation of data-hiding performance depends mainly on the visual quality of stego image and data-hiding capacity. In this paper, we propose a binary data-hiding method based on a block-wise scheme: the Improved Matrix Encoding (IME) scheme. The reason why we propose IME is to show the maximum embedding rate of a block-wise scheme.
The advantages of the proposed scheme include improving CPT's data-hiding capacity. The CPT scheme's embedding rate is
2. CPT Scheme
The CPT scheme is a pixel block-based method: given a binary image G, which is partitioned into disjoint blocks
In each such block F, by changing values of at most two entries, the number of bits to be embedded is r. The operation
Procedure {Watermark_Embedding} Begin S1. Partition F into blocks, each of size S2. For each block holds true. If so, go to step S3 to embed one data bit in otherwise, no data will be embedded in S3. Let the bit to be embedded in If (SUM Else if (SUM Randomly pick a bit Else if (SUM Randomly pick a bit Else Randomly pick a bit End if; End {Watermark Embedding}
Example 1.
Assume that the size of K and W is

Example: block F, key K, and weight matrix W.
3. Data-Hiding IME Scheme
In this chapter, we propose an IME scheme to improve the quality of binary images using a new matrix encoding scheme.
3.1. System Architecture
In this section, we describe the configuration for the CMOS Image Sensor system that achieves watermark embedding in spatial domain. The system consists of a CMOS imager and IME. Figure 2 shows the data flow in this system. The CMOS imager output is a sequence of digital values; the watermark is a binary sequence. In order to rebuild the watermark data, information of the key is required.

General system block.
3.2. Embedding Algorithm for IME
In this section, we propose an embedding algorithm that can improve that in Chang et al. [21] for IME. The basic idea is to use an abelian group under an XOR ⊕ operation.
The inputs and notation to our scheme are as follows:
K: a secret key shared by the sender and receiver. It is a randomly selected block of size W: a secret weight matrix shared by the sender and receiver. It is an integer matrix of size b: some critical information consisting of bits to be embedded in F; r: an embedded rate in each S: weighted sum of block
Algorithm 2 of the proposed scheme is described as follows.
Procedure {Data Hiding Embedding} Begin S0. If F is mono-value, keep F intact and exit. S1. Compute S2. Compute sum S3. If Otherwise, Set Compute if if if dist if if if dist End {Data Hiding Embedding}
We define a distance matrix dist
For example, with F is given by Figure 3.

The block F and the distance map for F.
In applications, to avoid taking roots, we use
Condition 1 (odd condition). Each submatrix of size 2 × 2 in W has at least one odd element.
Condition 2 (skip condition). It should be
where
3.3. Extracting Algorithm for IME
In this section, we describe the extracting method with the binary stego image using the IME scheme.
Example 2 (Matrix Encoding: embedding).
For
If secret data are the digit
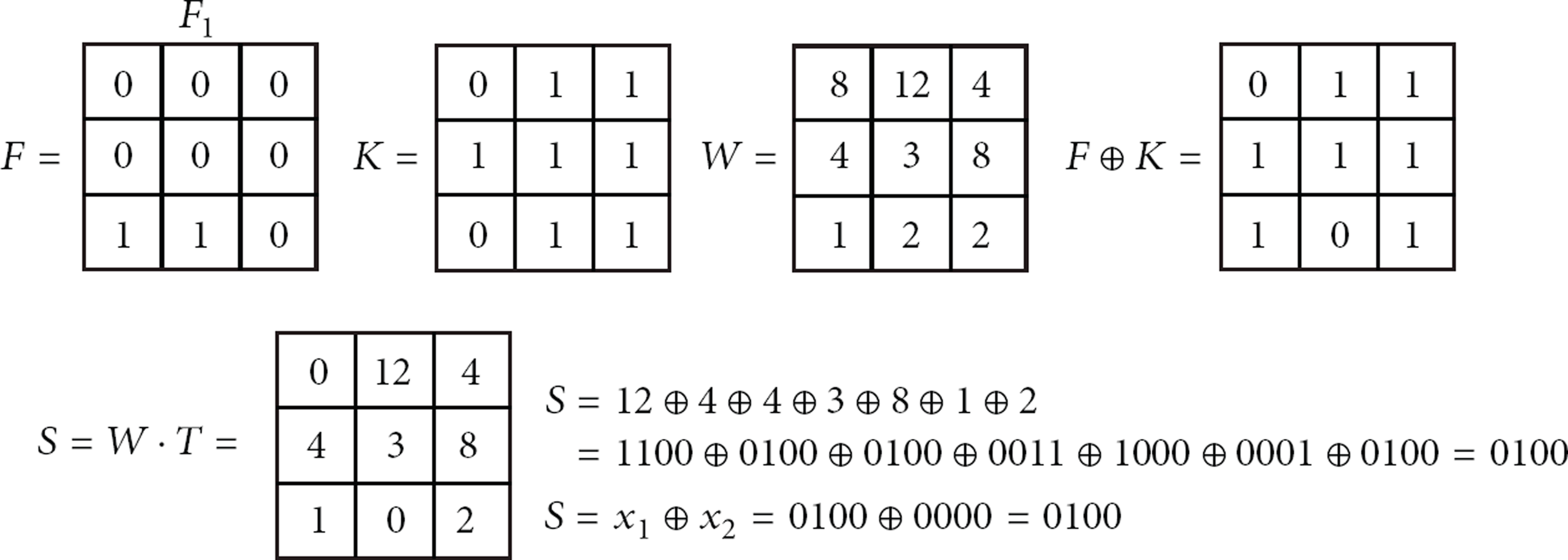
Example: block F, key K, and weight matrix W.
The correctness of Figure 4 is based on following theorem, which is easily checked.
Theorem 3.
Given a block F of binary image G, changing at most two pixels in F by Algorithm 2, one can hide
Procedure {Data Hiding Extracting} Begin S1. Compute S2. Compute (i) If u is odd: conclude F is fail and exit. (ii) If u is even: go to next step 3. S3. Return End {Data Hiding Extracting}
Proof.
By properties of XOR ⊕ operation and scalar multiplication ·, we have the evident fact:
flipping any entry consider now in Algorithm 2,
For example, we check the following case.
Example 4.
Let
4. Experimental Results
In this section, experimental outcomes are illustrated to show the feasibility of our proposed data-hiding mechanism. Various binary images, such as Mickey, Cycle, Landscape, Man, and Truck were chosen as the testing image (see Figure 5). The quality comparison was based on PSNR, which is represented in (4) and (5), for two

Original images, that is, Mickey, Cycle, Tree, Man, and Truck, were used for experiment.
Table 1 can be used to prove the claim. Our proposed schemes use the block-wise method; thus, Table 1 shows the comparison of block-wise methods, such as Maximal Secret Data Ratio (MSDR), CPT, MCPT, and IME.
Comparison of block-wise schemes, that is, MSDR, CPT, MCPT, and IME. (Compare a block,

Table 2 shows the experiment result. In this experiment, we used MCPT and IME schemes. The IME scheme's capacity is better than that of MCPT.
Comparison of capacity between MCPT and IME schemes.

Table 3 shows the comparison between MCPT and IME at the same hiding-capacity levels. In Figure 6, we compare stego experimental images, which are generated by MCPT and IME, because we compare visual quality by the HVS. By carefully observing the experimental results, we find that the visual quality generated by the IME data-hiding scheme is better than that generated by the MCPT data-hiding scheme.
PSNR comparisons between MCPT and IME at the same hiding-capacity levels.


Experimental results using the MCPT and IME schemes with Mickey, Cycle, Landscape, Man, and Truck.
The IME scheme has very good image quality and a reasonable capacity. Compared with the well-known MCPT method (see Table 3 and Figure 6), the experimental results of the method proposed in this paper show that our method can offer not only a higher maximum data-hiding capacity but also better visual quality.
5. Conclusion
Binary images are not easy for data hiding compared with grayscale or color images, because a binary image is very sensitive, so that the HVS can detect some flipping pixels. We researched to solve such a problem. In this paper, we proposed novel data hiding methods, namely, the IME scheme. The IME scheme has larger embedding rates than the CPT scheme and is approximate to that of MSDR. The results of our experiment showed that our schemes prove to be good schemes for binary data hiding.
Footnotes
Acknowledgment
This research was supported by the Basic Science Research Program through the National Research Foundation of Korea (NRF) by the Ministry of Education, Science and Technology (20120192).