Abstract
In cellular-based machine-to-machine (M2M) networks, supporting large number of machine-type communications (MTC) users (devices) has become a critical challenge in both the uplink and downlink channels. In this paper, we focus on the downlink beamforming using zero-forcing dirty paper coding (DPC). In order to characterize the system's ability of user admission, we consider the achievable user number, which is defined as the number of users whose signal-to-interference plus-noise ratios exceed a target threshold. Due to the complexity of the optimal scheme, we propose two algorithms with random user scheduling and greedy user scheduling in maximizing the achievable user number by dynamical power assignment. Using the joint distribution of effective channel gains, we derive the achievable user number of both the scheduling schemes. An upper bound on the achievable user number of the greedy scheme is then derived which is shown to be tight when there are a large number of users. From numerical results, we show that both of the schemes enjoy a linear increase in the achievable user number as the number of transmitter antennas increases. The performance of the greedy scheduling scheme is close to the optimal scheduling scheme.
1. Introduction
Wireless machine-to-machine (M2M) networks are emerging as new types of communication, where cellular systems are expected to play an important role in wireless M2M networks [1]. In cellular-based M2M networks, supporting large number of machine-type communications (MTC) users (devices) has become a critical challenge in both the uplink [2, 3] and downlink channels. The rate required by each MTC user may be low, however, their number may be large. Thus, the study on efficient user admission policies becomes one of the critical issues in M2M communications. In this paper, we focus on improving the number of active users in the cellular-based M2M communications networks.
In the cellular communications networks, beamforming techniques with multiple antennas at the base station (BS) are used for simultaneous transmission of multiple users. The multi-antenna techniques have received a lot of attention since the heuristic research work by Telatar [4] due to its diversity and multiplexing gain. When perfect channel state information is available at the BS, the optimal downlink beamforming scheme is dirty paper coding (DPC) [5] where the interference known at the transmitter is pre-subtracted at the BS. The optimal beamforming weight vectors and encoding order of DPC can be found using a duality between the downlink and the corresponding uplink channel. In [6, 7], numerical algorithms are proposed based on this duality. However, these algorithms exhibit an undesired iterative feature.
In order to reduce the complexity, a zero-forcing structure is imposed in DPC [5], that is, zero-forcing DPC. Only random user scheduling is considered in [5]. Subsequent works [8, 9] extend zero-forcing DPC in [5] by considering the user selection and propose a greedy user scheduling scheme.
In this paper, we focus on the performance evaluation and algorithms of multi-user systems with zero-forcing DPC. We are interested in the achievable user number, which is defined as the average number of users that are admissible in the system. We say that a user is admissible if the effective signal-to-interference-plus-noise ratio (SINR) achieves a given target SINR threshold. We propose algorithms to maximize the achievable user number. The difference of the zero-forcing DPC considered in this paper from the conventional zero-forcing DPC is that the proposed algorithms should maximize the achievable user number instead of the spectral efficiency (rate). Extensive literatures have been devoted to the spectral efficiency with few exceptions, for example, [10, 11]. The achievable user number is considered in [10] for characterizing the performance of a circuit scenario.
We consider the beamforming vector design and user scheduling of zero-forcing DPC for maximizing the achievable user number. The optimal beamforming vectors for maximizing the achievable user number can be calculated by the Gram-Schmidt process which is a method for orthogonalizing a set of vectors in a successive manner. When there are more users than the number of transmitter antennas, a user scheduling problem exists. The optimal scheduling scheme can be found by solving a combinatorial optimization problem which is not easy to solve. Thus, we propose two suboptimal scheduling algorithms for maximizing the achievable user number, that is, random scheduling and greedy scheduling.
We derive the achievable user number performance of both the random and greedy user scheduling, using the joint distribution of effective channel gains. An upper bound on the achievable user number of the greedy scheme is derived. Various numerical results are present to justify our theoretical analysis. The performance of the greedy scheduling scheme is shown to be close to the optimal scheduling scheme.
The rest of the paper is organized as follows. The system model is presented in Section 2. Some preliminaries of zero-forcing DPC are given in Section 3. The algorithms for maximizing the achievable user number are proposed in Section 4. The achievable user numbers of both random scheduling scheme and greedy scheduling scheme are derived in Section 5. A comprehensive evaluation of the achievable user number of zero-forcing DPC is given in Section 6 with numerical results. We conclude the paper with some remarks in Section 8.
Notations. The superscripts T and H stand for the transpose and Hermitian transpose, respectively. Upper and lower boldfaced letters are used for matrices and column vectors, respectively. Denote by
2. System Model
Consider the downlink transmission of a single cell system with a base station (BS) and K users in M2M communications. The users may be the group heads of group-based MTC devices. Suppose that the BS is equipped with an antenna array of L elements, while each user is with single antenna. Multiuser downlink beamforming is used for simultaneous transmission for N (≤K) active users in the system. As the number of antennas at the BS is L, a typical value of N is L, that is,
The transmitted signal vector from the antenna array to N active users, denoted by
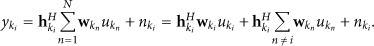
The signal received at the active user
Substituting (1) into (2) yields
The target SINR threshold for user k is denoted as
Throughout the paper, we assume that the channel vectors
3. Preliminaries of Zero-Forcing DPC
In this section, some preliminaries of downlink beamforming with zero-forcing DPC are given.
3.1. Dirty Paper Coding
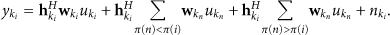
Assume a specific DPC encoding order [12] π, which means the encoding order of the user n is
For the index specific order, that is,
It has been proven that DPC is the capacity-achieving scheme for the multiple-input multiple-output (MIMO) broadcast channel (BC). The optimal beamforming weight vectors and encoding order can be found using a duality between the BC and the corresponding multiple access channel (MAC). Several numerical algorithms have been proposed, for example, [6, 7]. However it has been recognized that these algorithms exhibit an undesired iterative feature.
3.2. Zero-Forcing DPC
In order to reduce the complexity of the calculation, a zero-forcing structure is imposed to the beamforming weight vectors, resulting in a simplified scheme, zero-forcing DPC scheme. The term
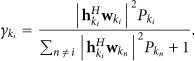
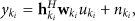
The resulting signal received by user
4. Algorithm for Maximizing User Number
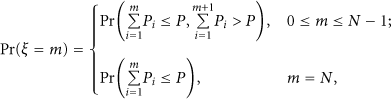
For a specific DPC encoding order π and N scheduled users
From
The
In a system where
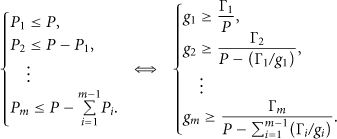
1: Initialize 2: 3: Choose a user 4: 5: 6: 7: 8: 9: 10: 11: 12: 13: break. 14: 16:
In Algorithm 1, the powers are assigned dynamically to each active user according to their channel conditions.
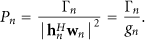
The step 4 of Algorithm 1 can be expressed equivalently as
The optimal user scheduling, step 3 of Algorithm 1, can be implemented by an exhaustive search of all possible active user set 𝒜 and encoding order π. The scope of search are
The optimal user scheduling is a combinatorial optimization problem which is obviously not easy to solve. Therefore, two suboptimal user scheduling methods are considered in this study. The first heuristic method is random scheduling, in which a user is randomly scheduled for downlink beamforming. In random scheduling, the step 3 of Algorithm 1 is
5. Achievable User Number Performance
In this section, we derive the achievable user number of zero-forcing DPC with both random and greedy scheduling for maximizing the achievable user number.
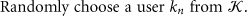
The achievable user number M is a discrete random variable with possible values
The probability
For the purpose of analysis, we make the following CSCG assumption as those in many literatures, for example, [15, 16].
Assumption 1.
The elements of each user's channel vector
Assumption 1 is reasonable in rich scattered environment. The path loss encountered by each user is assumed to be the same, and their channel directions are uniformly distributed. Assumption 1 simplifies the following performance analysis. It is noted that the algorithm in the Section 4 is not based on Assumption 1.
Besides, we assume that all the users have equal target SINR threshold, that is,
5.1. Achievable User Number with Random Scheduling
In the random scheduling scheme, we have the following lemma [5].
Lemma 1.
The channel gains
Thus, the probability density function (PDF) of each channel gain
Thus, the probability becomes
From (32), (30) and (23), we can calculate the average achievable user number of the random scheduling scheme.
5.2. Achievable User Number with Greedy Scheduling
In the greedy scheduling scheme, it can be shown that
Therefore, the integration domain with ordered effective channel gains, denoted by
Following the derivation in [9], we can have the lemma.
Lemma 2.
The channel gains
Proof.
The derivation follows from that of Proposition 1 in [9] with a notable exception that we proof the important Claim 1 in [9]. We give an equivalent of Claim 1 in [9] in Lemma 3.
Lemma 3.
Let
Proof.
See Appendix A.
From (37), (36) and (23), we can calculate the average achievable user number of the greedy scheduling scheme.
Inspired by the distribution in Lemma 1, an upper bound of the achievable user number can be found using the following lemma.
Lemma 4.
The best performance of the greedy user scheduling can be achieved when the channel gains
Thus, using order statistics, the CDF of each channel gain
From (43), (42) and (23), we can calculate the upper bound on the average achievable user number of the greedy scheduling scheme.
6. Simulations
In this section, various numerical results are presented. In Section 6.1, the theoretic results derived from Section 5 are shown. In Section 6.2, we compare the performance of the proposed schemes with other beamforming schemes. In Section 6.3, the performances of the random and greedy scheduling schemes are compared with the optimal scheme. In Section 6.4, the improvements of the scheme with dynamic power assignment over that with equal power assignment are presented. The performance characterizations of the algorithms with dynamic power assignment are given in Section 6.5.
In the following simulations, samples of each user's channel vector
6.1. Theoretic Results
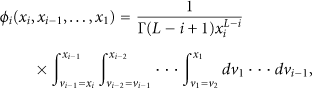
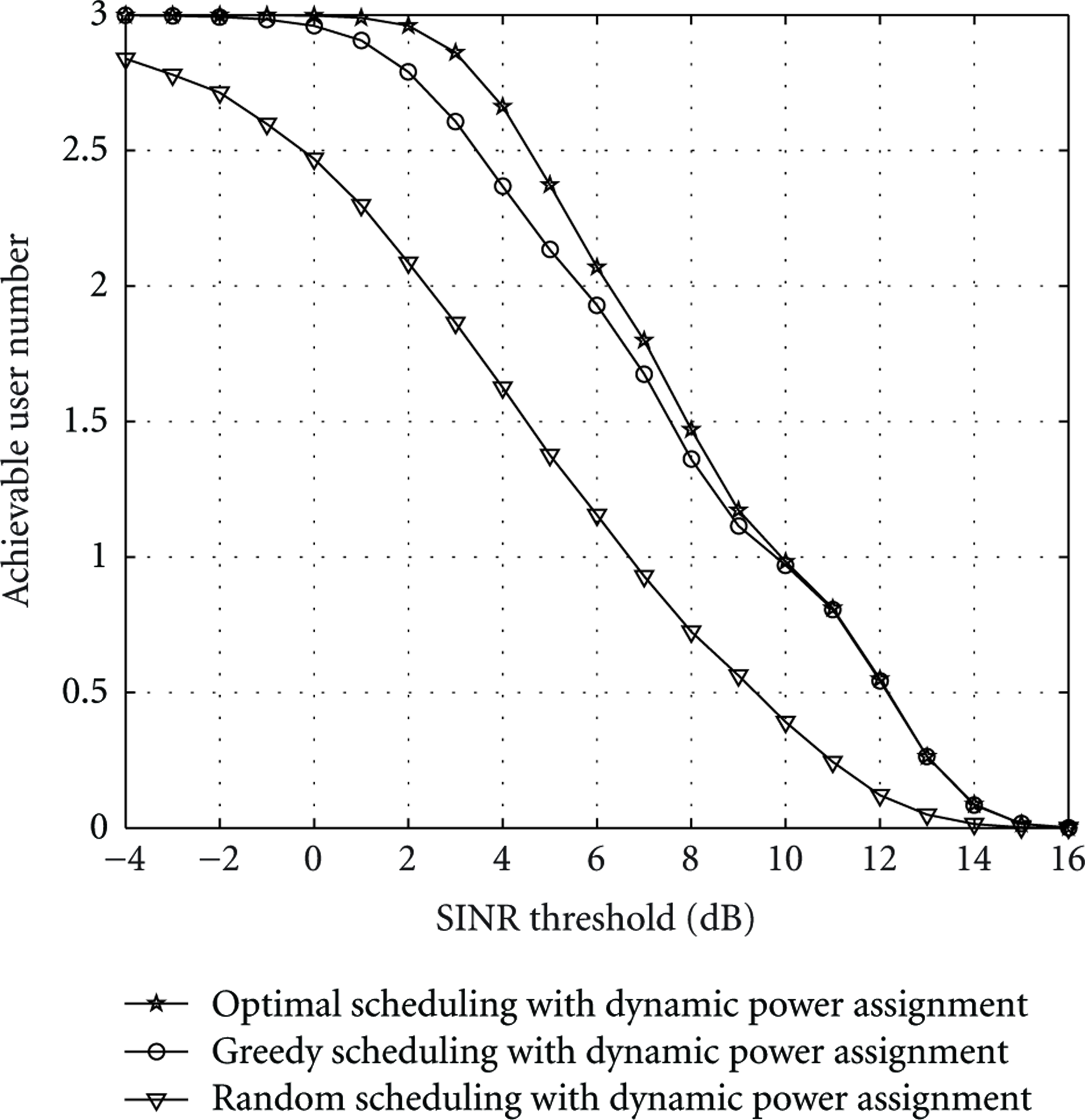
In Figure 1 the achievable user number performance of the schemes with dynamic power assignment is plotted for different SINR thresholds

Achievable user number versus SINR threshold, with
The upper bound of the greedy scheduling scheme with dynamic power assignment is shown in Figure 2, with
Achievable user number versus SINR threshold, with
These results justify our analysis in Section 5.
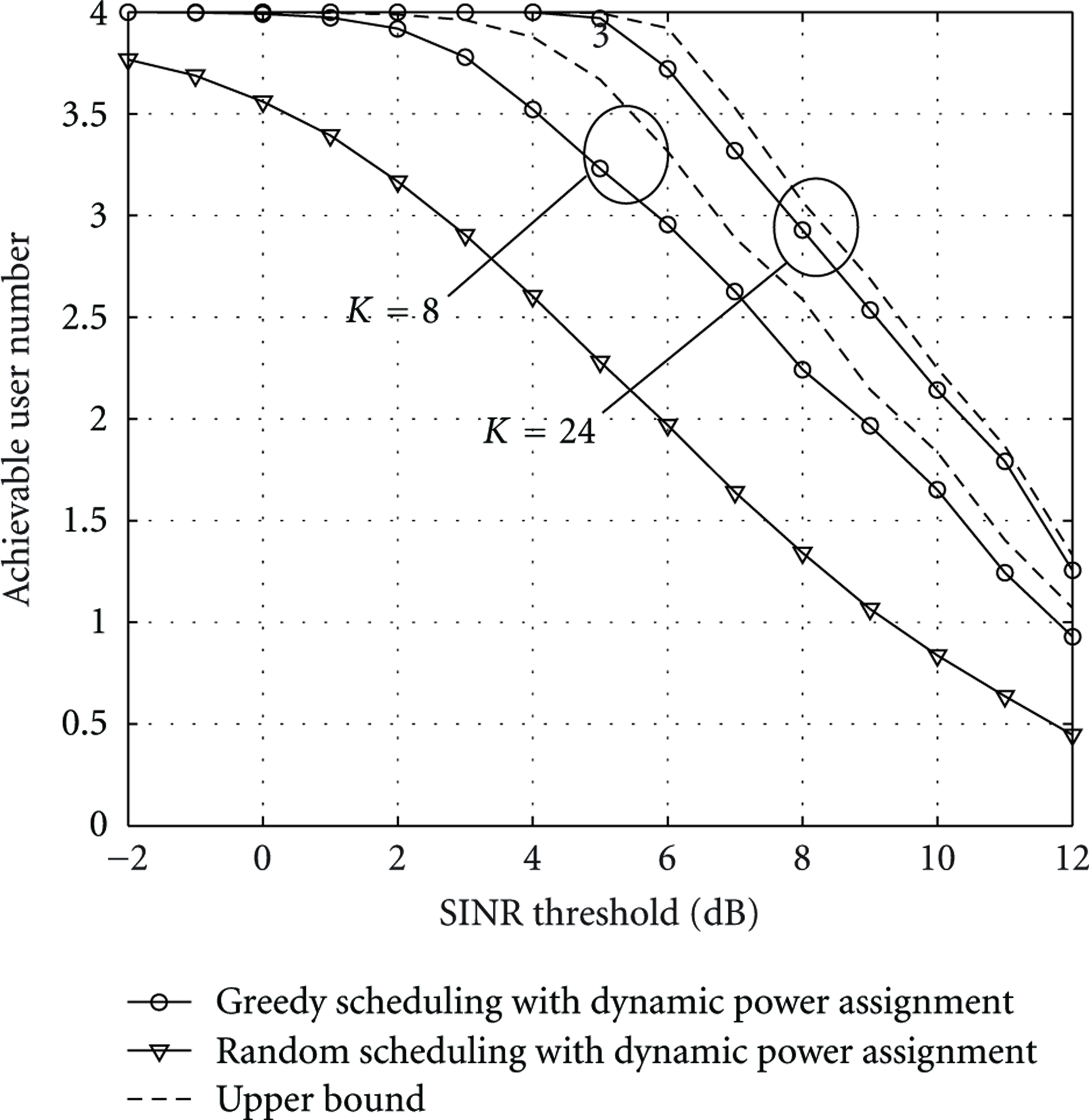
6.2. Comparison with Other Beamforming Schems
In Figure 3, the achievable user numbers of different beamforming schemes are shown. Four active users are considered with
Achievable user number of different beamforming schemes, with
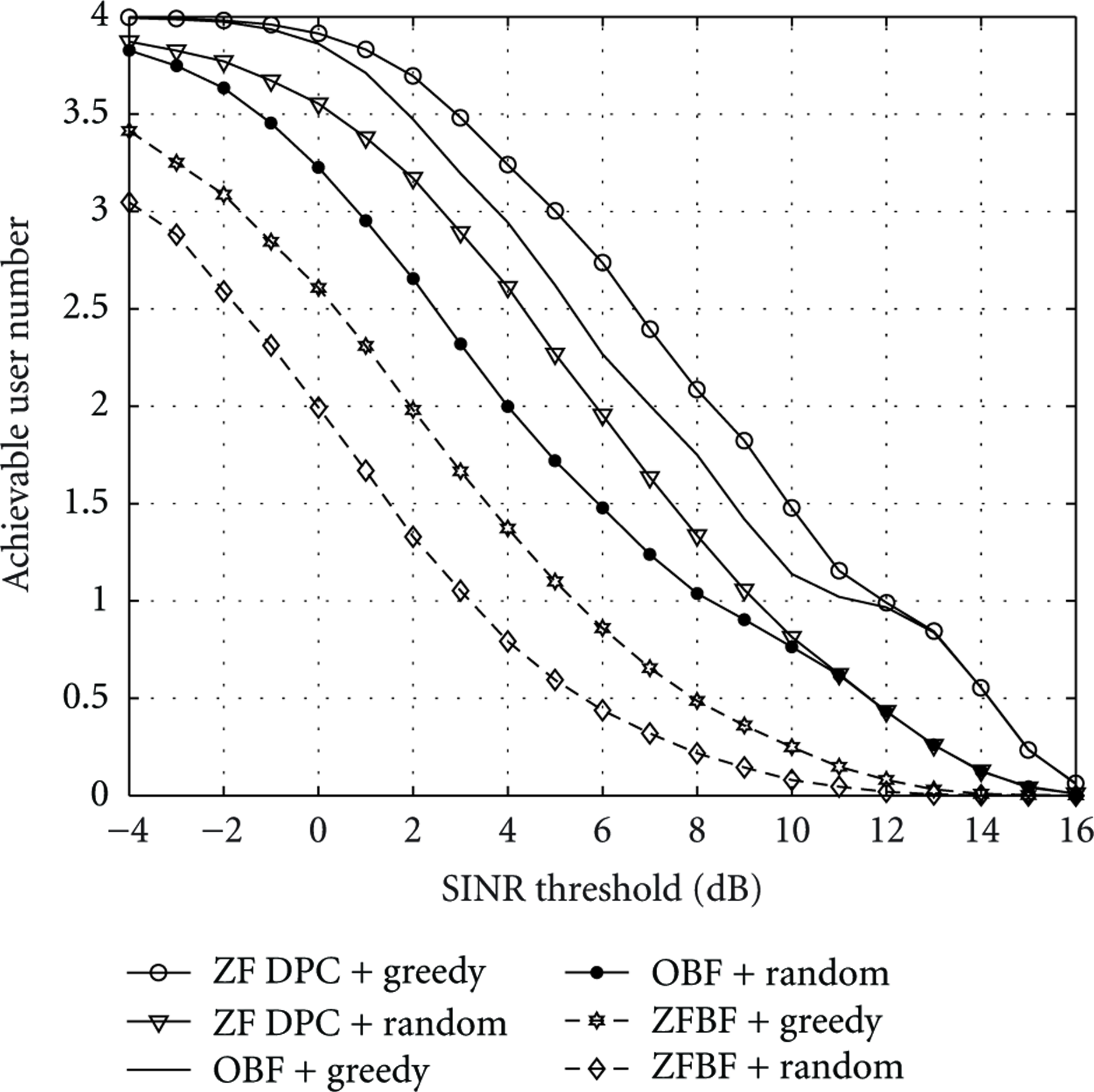
6.3. Comparison with the Optimal Scheduling
The achievable user numbers of both random and greedy scheduling schemes are presented in Figures 4 and 5 compared with the optimal scheduling scheme. The active user set and DPC encoding order of the optimal scheduling scheme are found by an exhaustive search.
Achievable user number versus SINR threshold, with

Achievable user number versus SINR threshold, with
In Figure 4 three active users are considered with
6.4. Improvement over Equal Power Assignment Schemes
In the equal power assignment schemes,
In Figure 6 the performance of the dynamic power assignment schemes is compared with that of the equal power assignment schemes for an increasing SINR threshold

Achievable user number versus SINR threshold, with
In Figure 7 the performance is compared for different number of transmitter antennas, with

Achievable user number versus number of transmitter antennas, with
6.5. Performance Characterizations
The performances of the dynamic power assignment schemes with both greedy and random scheduling are investigated.
In Figure 8, the performance is shown for an increasing number of antennas L, with

Achievable user number versus number of transmitter antennas, with
The achievable user number is shown in Figure 9 versus number of scheduled users, with

Achievable user number versus number of scheduled users, with
The achievable user number is plotted in Figure 10 versus total number of users, with

Achievable user number versus total number of users, with
7. Discussion
In an M2M network, large number of MTC users challenge the admission capability of the communication system. However, the data rate required by each user may be small. Thus, small portion of the system's bandwidth will be allocated to each user, and different users can be allocated with different carriers. In a multi-carrier scenario, the algorithm proposed in this paper can be incorporated with the subcarrier allocation process to maximize the achievable user number. During the subcarrier allocation process, each user is assigned with one subcarrier. After that, the beamforming weight vectors can be calculated by the proposed algorithm in Section 4.
Denote the number of carriers as Q. After the subcarrier allocation process, subcarrier q is allocated with a candidate set of users
The optimal subcarrier allocation remains an open question. However some other suboptimal schemes can be considered. It is noted that the greedy method adopted in the user scheduling can also be used in the subcarrier allocation process. The achievable user number of each subcarrier can be calculated one after another.
8. Conclusion
In order to characterize a system's ability of user admission, we considered the achievable user number, that is, the number of users whose SINRs exceed a threshold. The downlink beamforming using zero-forcing DPC was considered. The algorithms for maximizing the achievable user number were proposed, and the achievable user number of both random and greedy scheduling schemes were derived using the joint distribution of effective channel gains. An upper bound on the achievable user number of the greedy user scheduling scheme was derived. Various numerical results were presented. It was shown that the upper bound becomes tighter when there are larger number of users. The performance of the greedy scheduling scheme is close to the optimal scheduling scheme. Achievable user number was shown to be one useful metric in understanding the performance of a system, especially in M2M communications, where large number of users challenge the user admission.
Footnotes
Appendices
Acknowledgment
This work has been supported by the National Basic Research Program of China (973 Program, No. 2009CB320403).