Abstract
We address the modeling and design of linear network coding (LNC) for reliable communication against multiple failures in wireless sensor networks (WSNs). To fulfill the objective, we design a deterministic LNC scheme RDLC based on the average number of path failures simultaneously happening in the network other than the maximum number of path failures. The scheme can significantly improve the network throughput comparing with the traditional approaches. In our study, we also investigate the potential of random linear code RRLC for providing reliable communication in WSNs and prove the low bound of the probability that the RRLC can provide the reliable communication. Finally, extensive simulation experiments have been conducted, and the results demonstrate the effectiveness of the proposed LNC schemes.
1. Introduction
In recent years, wireless sensor network (WSN) has attracted significant attention for future generations of wireless applications in industry, agriculture, and military [1–5]. Despite its salient potentials, there are still many challenges to be addressed. In this paper, we will investigate how to provide reliable data transmissions in WSNs, which is very challenging because not only the wireless medium is vulnerable to severe channel fading and interference but also the sensor node always faces to energy exhaustion and physical damage.
Clearly, how to provide reliable communication in WSNs can be studied from multiple layers, including the physical layer and the MAC layer [6–9]. In this work, we will focus on the network layer and transport layer. Particularly, we will study how to provide reliable communication in WSNs against loss of data packets.
To provide reliable communication against node or link failures, there are two kinds of traditional approaches [10]: the proactive recovery and the reactive recovery, which aim at recovering the data transmission when node or link failures happen. The proactive recovery approaches can recover data transmission immediately when a link or node failure occurs, because it reserves the bandwidth (in backup paths) between the source node and the destination node in advance and the data flow is simultaneously transmitted on both primary paths and backup paths. On the other hand, the proactive recovery approaches do not provide any immediate recovery in advance. When the failure occurs on the routing paths of the data flow, the affected flow will be retransmitted to the destination by using available bandwidth in the network. Therefore, although the proactive recovery approaches can recover data transmission immediately when the link or node failures happen, network resources (e.g., bandwidth on the backup paths) are wasted when no failure happens. For the proactive recovery approaches, although network resources are used efficiently (no network resource is reserved in advance), the procedure of transferring the data traffic from the failed paths to the new routing paths incurs a considerable delay to data communications.
Following its success in maximizing network throughput [11–15], linear network coding (LNC) has recently been shown to be a promising approach that can achieve reliable communication with much better efficiency, because it can be used to provide protection in a proactive manner with the bandwidth cost in a reactive manner [16–20]. LNC has been first introduced by Kamal [16, 19] to provide 100% protection against single link failures in optical network. Recently, the design of reliable communication based on LNC has attracted an increasing amount of attention in optical networks [16], wireless networks [18], and hybrid wireless-optical access networks [20], respectively. However, in these studies, the LNC scheme, which can generate large number of linear combinations of original data packets to provide reliable communication when link or node failures happen, is designed according to the maximum number of failures (
Therefore, our key idea is to increase the number of original data packets transmitted and recovered in the transmission rounds with large number of failures happening simultaneously, by utilizing the redundant coded data packets transmitted in the transmission rounds with fewer failures happening simultaneously in the network to improve the network throughput.
Figure 1 gives an example to compare the network throughput that can be achieved by LNC scheme based on the maximum number of failures

Reliable communication using LNC: an example.
Since the
In this paper, we will design an efficient LNC scheme based on the average number of path failures, to provide reliable communication in WSNs. It must be noted that our study in this paper is different to our previous work in [21], where we have investigated the LNC design for providing
Firstly, different LNC designs are given to provide reliable communication in this paper. The deterministic LNC scheme proposed in Section 3 achieves the network throughput
Secondly, comparing with the work in [21], we not only give the theoretical design of deterministic LNC scheme and random LNC scheme but also conduct considerable simulations with four parameters to demonstrate the effectiveness of the proposed LNC schemes, from view of both network throughput and recovery delay. We also show the impact of the size of finite field on the performance of the proposed random LNC schemes, which is not investigated in [21].
The rest of the paper is organized as follows. Section 2 describes the system models and problem description. In Section 3, we design a deterministic LNC scheme to provide reliable communication in WSNs and give the theoretically analysis to show the achieved network throughput. The analysis of the usage of random LNC to realize reliable communication in WSNs is shown in Section 4. Simulation results are given in Section 5. Finally, we conclude the paper in Section 6.
2. Reliable Communication against Multiple Failures in WSNs Based on LNC
In this section, we will describe the problem studied in this paper. Specifically, we first introduce the network model. We then give the description of the reliable communication problem.
2.1. The Network Model
In this paper, we consider a multihop wireless sensor network as a directed acyclic graph
Although the wireless medium is vulnerable and the sensor node always faces energy exhaustion and physical damage, LNC can be designed to tolerate the link or node failures and provide reliable communications in WSNs. Specifically, L coded data packets are generated at the source node by linearly combining original data packets and transmitted through L edge-disjoint paths in each time slot. Since there will be different number of edge-disjoint paths failing simultaneously in different transmission rounds, we denote
Suppose that the data stream arrive rate is N data packets per time slot; the data packets arrived are firstly buffered at the source S, waiting for encoding and transmission towards the destination D. We will design an LNC scheme to protect the data stream with arrive rate N.
2.2. The LNC Scheme
In practical LNC schemes, the source node first divides the whole file into fix-size original packets. Then, the coded packets can be generated by encoding the original packets together. Moreover, each coded packet in the network corresponds to an encoding vector, which consists of the coding coefficients that it is produced with respect to the set of original packets. When the destination node received sufficient coded packets, it can decode and recover the original packets according to their encoding vectors.
Due to the limited computational capability of the sensor nodes in WSNs, we assume that the intermediate sensor nodes simply store and forward encoding packets. Such assumption is practical because coding operations require extra computation capability which imposes the processing overheads and may slow down the switching speed.
2.3. Problem Description
To improve the network throughput, we design the LNC schemes based on the expected number of path failures per time slot (
Therefore, in this paper, we aim to design an LNC scheme providing reliable communication in WSNs to achieve network throughput
2.4. Notations
To facilitate further discussions, we summarize main notations to be used throughout the rest of the paper in Table 1. We also denote the

3. Reliable Communication Using Deterministic Linear Network Coding
In this section, we provide a deterministic LNC scheme to provide reliable communication (RDLC) for multiple failures in WSNs.
We assume that a buffer exists in the source to buffer the newly arrived data packets and parts of original data packets arrived previously. We also assume that the destination has a buffer to buffer the coded data packets which have not been decoded. At the end of each time slot, the destination sends an acknowledgment to the source in order to report the number of coded data packets received in this time slot. Then, according to the number of coded data packets received by the destination in the previously time slots, the source first removes some original data packets arrived perviously in its buffer and then generates L new coded data packets by encoding the original data packets arrived previously and the newly arrived data packets together. After that, the source sends the L new coded data packets to the destination. At the end of time slot t, for all
We denote the N original packets arrived at time slot t as
N original data packets Generate L coded packets:
Receives Clear the buffer, set Remove the Generate L coded data packets: Send each coded packet
Received
Extend each received encoding vector Suppose that the matrix Decode and recover the tN original data packets as follows: Clear the its buffer and send a
Store the Send a
Suppose that 
Next, we will prove that the destination can decode and recover the
Lemma 1.
When
Proof.
When
Lemma 2.
When
Proof.
When 
We have

Since the block matrix
Therefore, we have
Theorem 3.
The destination can decode and recover the
Proof .
According to Lemmas 1 and 2, the theorem holds when 

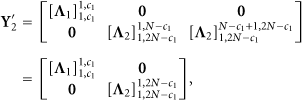
Similarly to the proof of Lemma 2, the block matrix
By step to step column transformation, the matrix 
When
Corollary 4.
If the average number of path failures is no more than
Proof.
When the average number of path failures is no more than
4. Reliable Communication Using Random Linear Network Coding
In the previous section, we have discussed how to construct linear network code at the source node in a deterministic manner to provide the reliable communication. In practice, random linear coding has been widely used in the literature [15, 22], because of the simplicity of the coding scheme. With random linear coding, random linear combinations of the packets can be forwarded by a node, which the node received previously, to outgoing edges. It has been proved in pervious work that such a simple approach can obtain valid linear codes for multicast with probability
In this section, we investigate the behavior of the random linear coding, when it is applied to the reliable communication problem we discuss in this paper. The usage of such linear code is similar to the one we discussed in Section 3. The coding operations are only done at the source node and destination node. The major difference is that, instead of computing the coding matrix
Specifically, the L coded data packets sent during time slot i can be represented by

Suppose that the number of coded packets received within time slot i by the destination node d is 


From above theoretical analysis, the destination D can decode and recover the set of
Next, we will give the lower bound of the probability that the destination D can decode and recover the original packets once it totally receives no less than
We set
Lemma 5.
If 
Proof.
Obviously, the matrix 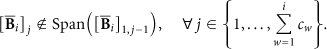
We first give the theoretical analysis on the first
Similarly, we then give the probability that the matrix
Suppose that the first
Let σ be the number of matrix 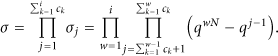
The total number of different matrix
Therefore, the probability that the matrix 
Theorem 6.
If the total number of coded packets received by destination d during the first i time slots is no less than 
Proof.
The destination node D can decode and recover the set of 
Since the probability that 
5. Performance Evaluation
In this section, we conduct simulations to compare the scheme that without considering reliable communication (denoted as Unreliable Communication Scheme) the linear coding schemes are designed for recovering from maximum number of edge failures and the proposed linear coding schemes.
In the transmission scheme without network protection, the source sent totally L original packets along the L paths between the source node and the destination node in each time slot, until the destination node receive all the L original packets. Since each path may fail in each time slot, the destination may wait for some time slots to receive all the L original packets.
In the linear coding schemes designed for recovering from maximum number of edge failures, the scheme codes
Therefore, in our coding scheme, we code the packets sent in the pervious time slots with the new packets together which can fully utilize the available paths in the network to achieve higher throughput. To achieve this goal, in the proposed linear coding scheme, the destination receives coded packets instead original packets in each time slot which may not be decoded immediately. Therefore, the destination may wait for some time slots to receive enough coded packets to decode and recover all the original packets sent by the source node in the past time slots. However, we will show in this section that we can decrease a bit of throughput to achieve a much low decoding delay.
The objectives of the simulation conducted in this work are as follows.
To compare the throughput achieved when using different schemes under different parameter settings. The throughput is referred to as the total number of original packets recovered (or reviewed) in the past time slots divided to the total number of time slots. To compare the recovery delay using different schemes under different parameter settings. The delay will cause by different schemes to receive (or decode and recover) all the original packets sent by the source node in the past time slots.
5.1. Simulation Setup
We have four parameters in our simulations.
The number of paths between the source node and the destination node, L, which varies from 10 to 20. The maximum number of paths between the source node and the destination node which can simultaneously fail, The number of original packets coded (or sent) in each time slots, N, which varies from 2 to The size of finite field,
In a network G, we suppose that there are L edge-disjoint paths between the source node S and the destination node D. In each time slot, there may be
For each combination of parameters L,
5.2. Simulation Results
We compare the network throughput and the recovery delay of the proposed RDLC and RRLC schemes with LLW scheme and the unreliable communication scheme.
Firstly, in Figure 2, we set

In Figure 2(a), the throughput of all the four schemes increases with the increase of the number of edge-disjoint paths between the source node and the destination node. The reason is that the more the number of edge-disjoint paths exist between the source node and the destination node the more packets can be transmitted successfully to the destination. The throughput of the LLW scheme is higher than the unreliable communication scheme, because the LLW scheme exploits the LNC to ensure that all the original packets sent in one time slot can be recovered by the destination node which limit the number of original packets transmitted in each time slot. On the other hand, the unreliable communication scheme will transmit the same set of original packets many times to make sure the destination node can successfully receive all of them. The throughput of the proposed RDLC and RRLC schemes are much higher (more than
In Figure 2(b), the recovery delay of the unreliable communication scheme is higher than the other three schemes. The unreliable communication scheme will transmit the same set of original packets many times to make sure the destination node can successfully receive all of them. The recovery delay of the LLW scheme is always one time slot because a limited number of original packets are transmitted in each time slot to make sure the destination can decode and recover them in one time slot. The recovery delay of the proposed RDLC and RRLC schemes are between the unreliable communication scheme and the LLW scheme. Therefore, we can observe that the proposed RDLC and RRLC schemes can achieve highest throughput and moderate recovery delay. The figure also shows that the recovery delay of the RRLC scheme is higher than the recovery delay of the RDLC scheme. The reason is that according to the theoretical analysis a destination may not be decode and recover the original packets when using the RRLC scheme, even if it totally received more than
Secondly, in Figure 3, we set

In Figure 3(a), the throughput of all the four schemes decreases with the increase of α, because the number of edge-disjoint paths between the source node and the destination node is fixed but the number of failure paths increases. We can observe that the throughput of LLW scheme will be lower than the unreliable communication scheme when α grows sufficiently large. The reason is that when α grows sufficiently large, the throughput of of LLW scheme
In Figure 3(b), the recovery delay of the proposed RDLC, RRLC schemes, and the unreliable communication scheme increase with the increase of α. Moreover, The recovery delay of the unreliable communication scheme is higher than the other three schemes. The recovery delay of the LLW scheme is always one time slot because a number of original packets transmitted in each time slot decreases when the α increase to make sure the destination can decode and recover them in one time slot.
Thirdly, in Figure 4, we set

In Figure 4(a), the throughput of the proposed RDLC, RRLC schemes increases with the increase of N, because the throughput of the proposed RDLC, RRLC schemes can achieve N only if N is no more than the total number of paths minus the average number of path failures each time slot. In our simulation, the condition is that
Figure 4(b) shows that the values of N also do not have impact on the recovery delay of the unreliable communication scheme and the LCW scheme. On the other hand, the recovery delays of the proposed RDLC, RRLC schemes increase with the increase of achievable throughput. However, by selecting a suitable value of N, a transmission can achieve a higher throughput with a lower delay compared with the unreliable communication scheme and the LCW scheme.
Finally, in Figure 5, we set

In Figure 5(a), the throughput of the proposed RDLC, RRLC schemes, the unreliable communication scheme, and the LCW scheme do not change because the throughput of them does not related with the size of the finite field. However, as we showed in Section 4, the size of the finite field has impact on the decoding probability that the destination to recovery the original packets when using the RRLC scheme. Therefore, the increase of the size of the finite field will increase the decoding probability and reduce the recovery delay. The trends of the recovery delay of the RRLC scheme shown in Figure 5(a) are consistent with our theoretical analysis. The recovery delay of the other three schemes does not related with the size of the finite field.
6. Conclusion
In this paper, we have explored the power of LNC to provide reliable communication for multiple failures in WSNs. The key idea is to design the LNC scheme based on average number of path failures, in which part of original data packets sent previously is still encoded into the following time slots, in order to improve the network throughput by utilizing the redundant coded data packets transmitted in the transmission rounds with fewer failures happening simultaneously in the WSN. Specifically, we first give the design of deterministic LNC scheme based on the average number of path failures, by which the network throughput is significantly improved comparing with the traditional approaches designed based on the maximum number of path failures. We also have investigated the behavior of the random LNC, when it is applied to the reliable communication problem studied in this paper. We have given the performance evaluation, which demonstrates the effectiveness of the proposed LNC schemes.
Footnotes
Acknowledgments
This work is supported in part by the National Natural Science Foundation of China under Grants no. 61202378, 61070169, 61070170, and 61201212, the Fundamental Research Funds for the Central Universities under Grant no. 2012HGBZ0640, the Natural Science Foundation of Jiangsu Province under Grant no. BK2011376, the Specialized Research Foundation for the Doctoral Program of Higher Education of China no. 20103201110018, and the Application Foundation Research of Suzhou of China no. SYG201118, SYG201238, and SYG201239.

