Abstract
The uses of wireless sensor networks have increased to be applicable in many different areas, such as military applications, ecology, and health applications. These applications often include the management of confidential information, making the issue of security one of the most important aspects to consider. In this aspect, a user authentication mechanism that allows only legitimate users to access the network data becomes critical for maintaining the confidentiality and integrity of the network information. In this paper, we describe and cryptoanalyze previous works in user authentication to illustrate their vulnerabilities and security flaws. We then propose a robust user authentication scheme that solves the identified limitations. Additionally, we describe how the proposed protocol is more suitable for a secure sensor network implementation by analysis in terms of security and performance.
1. Introduction
Wireless sensor networks (WSNs) are being applied in different fields such as habitat monitoring [1], indoor sensor networks [2], military applications [3], and health monitoring [4]. Many of these applications manage confidential information, making the issue of security one of the most important points to consider. One of the fields of research in wireless sensor network security is the user authentication scheme that allows only authentic users to access the data collected by the sensor nodes.
In 2006, Wong et al. [5] proposed a dynamic user authentication scheme and discussed the implementation issues with the recommendation of using the security features of the IEEE 802.15.4 MAC sublayer. Later, in 2009, Das [6] presented his research work where he identified vulnerabilities in Wong et al.'s protocol and proposed his own authentication scheme based on the two-factor user authentication concept. After publication of Das' proposal, several works have pointed out that such a protocol was vulnerable to other attacks. Nyang and Lee [7] identified that Das' protocol was vulnerable to offline password guessing and sensor node compromising attacks. Huang et al. [8] also identified some limitations of Das' scheme, such as vulnerability from an impersonation attack. Additionally, [9] pointed out the absence of a mutual authentication feature in Das' protocol, while Khan and Alghathbar [10] pointed out more security flaws of Das' proposal, noting that it was vulnerable to privileged-insider and gateway-node bypassing attacks. References [7–10] also proposed enhanced versions of Das' protocol to eliminate detected vulnerabilities. However, those proposals still include several vulnerabilities and limitations that an adversary could take advantage of.
In this paper, we provide two specific contributions to the WSN user authentication research area: (1) first, we cryptoanalyze the aforementioned works and show how reference [7] is still vulnerable to parallel session and privileged-insider attacks and how it does not offer a password change mechanism. We also illustrate how [8] is vulnerable to parallel session and privileged-insider attacks and how it does not provide mutual authentication and password change features. Additionally, we explain how [9] is defenseless against parallel session, privileged-insider, and gateway-node bypassing attacks, does not offer a password change mechanism, and has a serious vulnerability in its mutual authentication mechanism. Furthermore, we explain how [10] is vulnerable from parallel session attacks, only offers a partial protection against gateway-node bypassing attacks, and does not provide mutual authentication between the user and the gateway-node. (2) Later, after identifying the limitations of previously mentioned works, we propose a robust user authentication for wireless sensor networks which fixes the aforementioned weaknesses.
The rest of the paper is organized as follows. Section 2 briefly reviews the existing works and details the weaknesses and security pitfalls of such schemes. Section 3 then presents the proposed protocol which solves the vulnerabilities and limitations mentioned in Section 2. Next, Section 4 analyzes the proposed protocol in terms of security and performance. Finally, Section 5 concludes this paper.
2. Previous Works and Their Cryptanalysis
In this section, we explain briefly the proposal of Das [6]. We then describe further works [7–10] focused to solve the limitations of Das' scheme and how those enhanced proposals are still not secure and have several security vulnerabilities.
2.1. Review of the Das Scheme
The scheme proposed by Das [6] is composed of registration and authentication phases.
Registration Phase
A user
Authentication Phase
This phase is executed when
(1) Login Phase.
(2) Verification Phase. Upon receiving the login request at time
2.2. Chen-Shih's Scheme
In [9], the authors indicate that Das' scheme fails in mutual authentication and it is vulnerable to parallel session attack, and propose “A robust mutual authentication protocol for wireless sensor networks” which still has vulnerabilities and limitations.
2.2.1. Review of Chen-Shih's Scheme
The protocol proposed in [9] is composed of registration, login, verification, and mutual authentication phases.
Registration Phase
The user
Login Phase
When
Verification Phase
Once the
Mutual Authentication Phase
After receiving the message
2.2.2. Cryptoanalysis of Chen-Shih's Scheme
Here, we show how the proposal of Chen and Shih still has some critical security pitfalls and limitations.
Parallel Session Attack
In Chen-Shih's scheme, the authors include the random nonce
Gateway Node Bypassing Attack
The Chen-Shih scheme uses the
Privileged-Insider Attack
The system administrator or privileged-insider of
Vulnerable Mutual Authentication between
and
Chen-Shih's scheme proposes a mutual authentication phase. However, it has vulnerability which allows an adversary to execute the
Lack of Mutual Authentication between
and the Sensor Node
The Chen-Shih scheme does not provide a mutual authentication mechanism between
Lack of a Password Change Phase
The Chen-Shih scheme does not provide a password change phase for
2.3. Khan-Alghathbar's Scheme
In [10], the authors indicate that Das' scheme is vulnerable to gateway node bypassing and privileged-insider attacks. They also point out that Das' scheme does not provide mutual authentication or a password change mechanism. As a response to such limitations, they propose improvements of Das' scheme which still has vulnerabilities and limitations.
2.3.1. Review of Khan-Alghathbar's Scheme
The protocol proposed in [10] is composed of registration and authentication phases.
Registration Phase
A user
Authentication Phase
This phase is executed when
(1) Login Phase.
(2) Verification Phase. Upon receiving the login request at time
Password Change Phase
When a user
2.3.2. Cryptoanalysis of Khan-Alghathbar Scheme
The proposal of Khan and Alghathbar still has some critical security pitfalls and limitations as shown below.
Parallel Session Attack
Assume that a legal user Tom eavesdrops on the message
Gateway Node Bypassing Attack
The secret value
Lack of Mutual Authentication between
and
First of all, the aforementioned work proposes a mutual authentication between
2.4. Nyang-Lee's Scheme
In [7], the authors point out that Das' scheme is vulnerable to password guessing attacks and gateway node impersonation attacks and has the limitation of a lack of protection relating to query-response. As a response to such security pitfalls, the authors propose a security-enhanced protocol.
2.4.1. Review of Nyang-Lee's Scheme
In [7], the authors propose a security-enhanced protocol composed of the registration and authentication phases.
Registration Phase
The registration phase is the same as that of Das' protocol except that
Authentication Phase
It starts with the submission of
2.4.2. Cryptoanalysis of Nyang-Lee's Scheme
The Nyang-Lee's proposal still has some critical security pitfalls and limitations as shown below.
Parallel Session Attack
The Nang-Lee scheme is vulnerable to a parallel session attack in the same way that happens in [9, 10]. A legal user Tom can obtain the message
Privileged-Insider Attack
The system administrator or privileged-insider of
Lack of Password Change Phase
This scheme does not provide a password change phase for
2.5. Huang et al.'s Scheme
In [8], the authors point out that the security features of Das' scheme is based on the
2.5.1. Review of Huang et al.'s Scheme
In this scheme,
Registration Phase
The user
Login Phase
Verification Phase
Once
Password Change Phase
When
2.5.2. Cryptoanalysis of Huang et al.'s Scheme
Parallel Session Attack
Huang et al.'s scheme is vulnerable to parallel session attacks in the same way that can happen in [7, 9, 10]. A legal user Tom can obtain the message
Privileged-Insider Attack
The system administrator or privileged-insider of
Lack of Mutual Authentication
Huang et al.'s scheme does not provide a mutual authentication mechanism. Therefore, it is vulnerable to
3. Proposed Protocol
This section describes a proposed enhanced protocol which fixes the weaknesses of previous works. The proposed protocol is composed of three phases: Registration, authentication and password change phases executed among three independent entities: users, gateway node, and sensor nodes.
3.1. Registration Phase
A user
Meanwhile, a unique secret key
3.2. Authentication Phase
This phase is performed when
Login Phase
Verification Phase
Upon receiving the login request at time
Session Key Establishment
A session key between
3.3. Password Change Phase
4. Analysis of the Protocol
In this section, we analyze the proposed protocol in terms of security and performance.
4.1. Security Analysis
In this part, we analyze the security of the proposed protocol in terms of formal verification and analysis of aforementioned attacks. The registration and password change phases of the proposed mechanism were excluded from this analysis because they are executed in a secure environment. In the analysis of the authentication phase, the widely used Dolev-Yao [16] threat model was applied, which assumes that two communicating parties communicate over an insecure channel.
4.1.1. Formal Proof Based on BAN Logic
In this subsection, we demonstrate the security of the proposed mechanism by a well-known formal model called BAN logic [17]. BAN logic has been widely used in different works such as [18–20] to reason about their security validation.
The logical notations of BAN logic used in this paper are as described as follows.
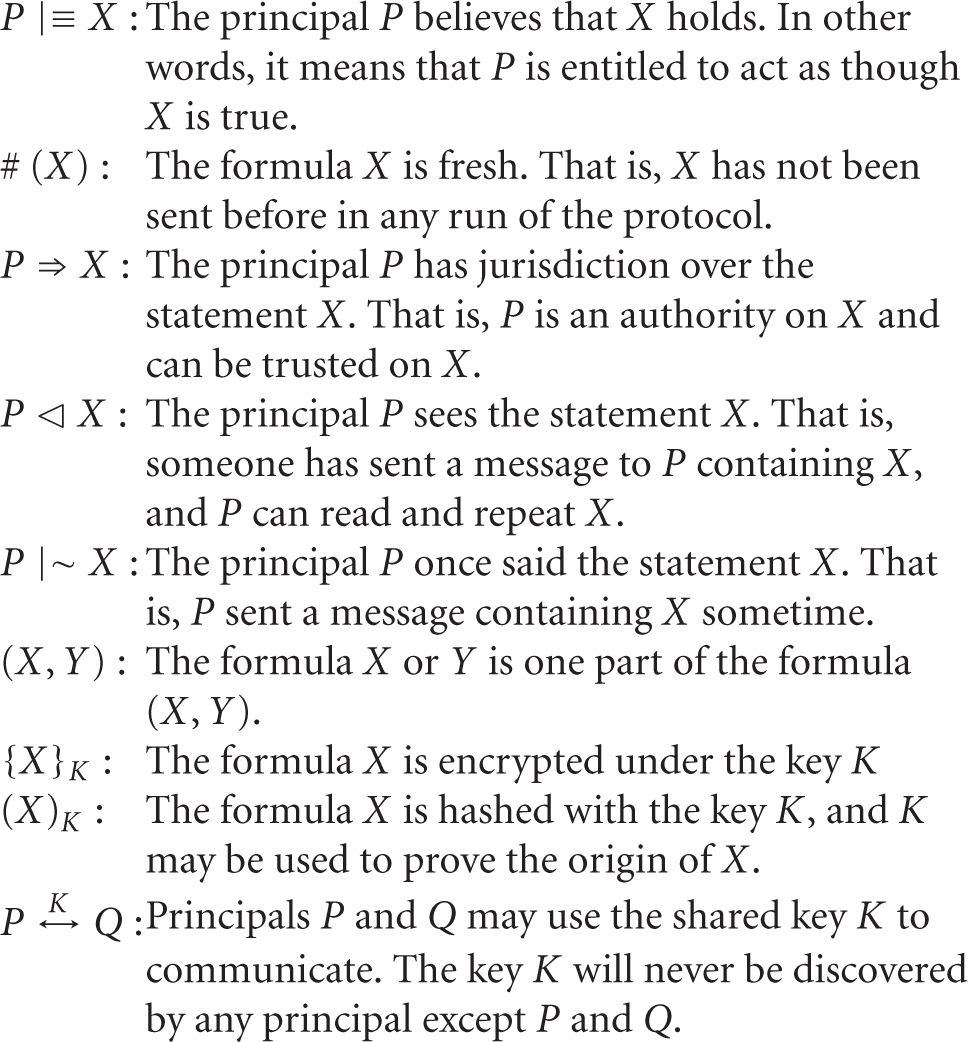
Moreover, we describe some main logical postulates to be used in proofs.
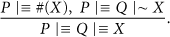
Message-Meaning Rule
If the principal P believes that the secret key is shared with the principal Q and P sees that the statement X is encrypted under K, then the principal P believes that the principal Q once said the statement X

Freshness-Conjuncatenation Rule
Provided that the principal P believes freshness of the statement X, the principal P believes freshness of the 
Nonce-Verification Rule
Provided that the principal P believes that the statement X has never been utter before and the principal Q once said X, the principal P believes that Q believes X
Jurisdiction Rule
Provided that the principal P believes that the principal Q jurisdiction over the statement X, the principal P believes Q on the validity of X
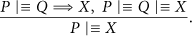
Belief Rules
A necessary property of the belief operator is that P believes a set of statements if and only if P believes each statement separately. This justifies the following rules:


First, we transform the messages of the proposed protocol to the idealized form as follows:

Second, we make the following assumptions about the initial state of the scheme to analyze the proposed scheme:

Finally, we perform the proof steps to the idealized form of the proposed scheme based on the BAN logic rules and the assumptions (see Table 1).

The proposed goals were reached by (S.17)–(S.24), (S.29), (S.34), and (S.35). In summary, we have demonstrated how the proposed scheme provides mutual authentication as well as establishes a fresh session keys among
4.1.2. Security Verification from Possible Attacks
This subsection analyzes the security of the proposed solution against possible attacks. We assume that common communication channels are insecure and that there exists an attacker who can intercept all messages communicated among
Parallel Session Attack
Even though another legal user of the system, say Tom, eavesdrops on
Privileged-Insider Attack
In the proposed solution,
Gateway Node Bypassing Attack
The reason for the possibility of a
In the proposed protocol,
Mutual Authentication
The proposed protocol provides both mutual authentication between
(1) Mutual authentication between
(2) Mutual authentication between
Masquerade Attack
An adversary who wants to impersonate a valid user
Replay Attack
Timestamps and random nonces are used to avoid replay attacks. At the beginning of each authentication request, a timestamp mechanism is used to guarantee the freshness of the authentication request. Later, a stronger mechanism: challenge-response of codified nonces is used to respond to the authentication requests. An adversary cannot replay a valid
Stolen-Verifier Attack
One of the features of the proposed protocol is the absence of a password/verifier table which prevents our solution from stolen-verifier attacks.
Guessing Attack
In the proposed scheme, secret values are never sent in plaintext, but encrypted inside a one-way hash function. Therefore, even if the adversary got
Many Logged-IN Users with the Same Login ID
By using two-factor based authentication, the proposed scheme offers higher protection than only-password-based schemes against this attack. Assuming that the
Brute-Force Attack
An attacker can try two kinds of brute-force attacks. (1) First, the attacker can attempt to authenticate by sending random or sequential messages (
Password Change Phase
Our proposal offers a light-weight password change phase that does not require communication with
Session Key Establishment
Our proposal offers a simple and practical method for session key establishment among
Table 2 shows the comparison of security features among different works. This demonstrates how our scheme is stronger in terms of security. Our approach provides protection against different kinds of attacks (privileged insider's attack, gateway node bypassing attack), also provides a secure password change phase, session key establishment, and achieves complete mutual authentication (mutual authentication between
List of enhanced security features of the proposed protocol.

4.2. Performance Analysis
Table 3 indicates the number of hash operations required in each phase for each entity. It shows that our protocol requires a few more operations in the verification phase than some previous works. However, the majority of additional operations are executed by
Performance analysis/number of operations (h: hash, se: symmetric encryption, sd: symmetric decryption).

According [22], the energy consumed by the MIPS R4000 and MC68328 “DragonBall” processors for performing the SHA-1 hashing function are 0.0000072 mJ/bit and 0.0000410 mJ/bit, respectively. Based on the previously mentioned data, we can calculate the energy consumed by sensor nodes executing the operations of the proposed scheme. Assuming that the size of
5. Conclusion
In this paper, we have analyzed previous user authentication mechanisms for wireless sensor networks and identified their vulnerabilities and limitations. We also have proposed a robust user authentication for wireless sensor networks that eliminates the identified security flaws. The proposed solution takes advantage of the two-factor authentication concept to provide a secure authentication system offering balanced features in terms of security and performance.
