Abstract
We simulated a sensor network that detects and tracks the release of harmful airborne contaminants in an urban environment. The simulation determines sensor placement in that environment. The effort required integration of models from computational fluid dynamics (CFDs), combinatorial optimization, and population mobility dynamics. These CFD models, coupled with population mobility models, facilitate estimation of the effect of released contaminant on civilian populations. We studied the effects of a contaminant, chlorine gas, as a function of urban environment, prevailing winds, and likely attack locations. The models predictions optimized sensor node locations, providing mitigation of contaminant effects on human population. Results show that higher fidelity dispersal predictions increase sensor placement effectiveness. Incorporation of civilian evacuation models helps to minimize the overall impact of an attack when compared to a static population. Moreover, results show the benefits of using seasonal sensor configurations to maximize detection capabilities, taking into account prevailing seasonal wind conditions.
1. Introduction
Security concerns (e.g., [1–3]) focused attention on techniques that detect, localize, and respond to nuclear, biological, and chemical (NBC) agent attacks in dense urban population centers. One of the objectives of these techniques is to provide accurate predictions of agent dispersion at the onset of an attack so that rescue and evacuation efforts can be coordinated. Another objective is to determine sensor placement to provide optimal mitigation (e.g., minimize detection time and contaminant effect on human population). This research uses dispersion prediction techniques to optimize NBC sensor placement.
A powerful tool for dispersal prediction is computational fluid dynamics (CFDs) [4–9], which provide a family of models to conduct “what if” analysis. Detection of NBC threats benefits from the large number of sensing mechanisms and sensor systems that have been studied recently (i.e., [10–12]). Still, design and deployment of a reliable and accurate network of these sensors over a large area remains a challenge [13, 14]. Such a network would minimize the delay between the onset of a threat and its detection under specified tradeoff between the (high) probability of detection and the (low) probability of false alarm.
The design of an effective sensor network depends upon the sensor type, physical parameters of the environment (e.g., the speed and direction of the wind causing agent dispersal), and civilian response (e.g., crowd dynamics during evacuation). One of the practical considerations of our design is the use of “point sensors,” which require the agent to physically pass through the sensing mechanism. This sensor characteristic is reemphasized in Section 2.1. Ideally, the network will be able to provide reliable detection of the threat, allowing optimal mitigation and neutralization [13]. The challenge is to integrate all the pertinent factors (physical constraints, threat assessment, sensor capabilities, and human factors) into a system that provides a good compromise between the multiple performance indices that the system is expected to meet.
Since the focus of this paper is optimizing NBC sensor placement, we do not consider a specific networking technology that could be used to interconnect our sensors. However, given the proliferation of wireless devices and networks and assuming urban infrastructure, the NBC sensors could be networked through a variety of techniques including telephone lines, fiber optic networks, mobile broadband networks, urban Wi-Fi, power lines, or a combination of any of the aforementioned systems. For example, in [15] the authors describe an NBC sensor communication network that would be suitable for deploying our sensor network. The authors also claim that the network can be ported from one city to another if implemented correctly, thus reducing the amount of network redesign to deploy in a variety of urban environments.
The following conceptual example (see Figure 1) illustrates how the technologies developed in this paper apply in the event of an NBC attack. Consider the release of a harmful agent in a highly populated region within a dense urban area. A network of sensor nodes, distributed throughout the environment, on rooftops, sides of buildings, and other fixtures, detects the release of the agent. The placements of the sensor nodes were optimized prior to system deployment through techniques that take into account expected attacks, typical environmental conditions, and population distributions. Specifically, CFD modeling of the airflow through the environment was performed, given the prevailing winds; an inventory of potential targets was collected to determine which ones are likely to be chosen by an adversary. The sensor nodes perform distributed signal processing and data fusion calculations to monitor contaminant propagation in the environment. Results are communicated to the municipal command center and to rescue and first-responder organizations. Based on population density data and road conditions, plans for evacuation and contaminant countermeasures are recommended. This paper describes simulation and optimization techniques to design the sensor network needed for such scenarios (i.e., select sensor locations). The sensor framework is based on work done by Berry et al. [16]. We used the Fire Dynamics Simulator (FDS) [17] for NBC fallout dispersion simulations. The civilian evacuation model we employed is based on the cellular automata model developed by Burstedde et al. [18].

3D Illustration of an example NBC sensor network.
In Section 2, we discuss sensor network design and provide background material on our simulation efforts. In Section 3, we develop the system models for selecting the placement of sensors from a set of candidate locations and civilian evacuation. Section 4 presents the CFD dispersion modeling and civilian evacuation simulations. In Section 5, we discuss fallout dispersion, the effect of additional sensors in the network, civilian evacuation, and sensor placement optimization based on static and variable population. Finally, in Section 6, we present our conclusions.
2. Background
2.1. Sensor Network Design
Design of sensor networks for homeland security was the focus of studies by several U.S. government agencies, most notably the Defense Threat Reduction Agency of the U.S. Army Nuclear and Chemical Agency [19]. These efforts resulted in the development of several tools including SAFE (Sensor Analysis and Fusion Environment) and REASON (Response and Effects Analysis System for Operational Needs) [19].
A considerable amount of work was done on grid-based methods [20–24]. These methods often assume that each sensor has a known detection radius (area sensors) and seek to provide complete coverage in the sense that each point in regions under surveillance is covered by at least one sensor. Some of the issues that were studied are the effects of sensor positioning accuracy, imprecise sensing, terrain, and cost. In [24], Zou and chakrabarty focus sensor placement on a cluster-based distributed sensor network and use a virtual force algorithm to place sensors after an initial random deployment. This method attempts to localize detection using a given number of sensors within the distributed network. Another topic of interest is preferential coverage, taking into account tactical considerations and security [21]. This method also relies on area sensors. Most detectors available for NBC agent detection are, however, “point sensors,” that can only detect a threat at a single point in space [12]. Point sensors provide more reliable detection when compared to area sensors, which have higher false alarm rates due to environmental conditions. A typical NBC sensor requires an agent to attach physically or chemically to the surface area of the sensor, employing chemical processes or infrared spectroscopy for accurate detection [10, 11]. The design described in this paper employs the use of point sensors.
Characteristics of a sensor network can drive the sensor placement formulation as well. For example, in [25–30], a wireless sensor network model drives node placement with respect to communication constraints such as power consumption, uncertainty, and failure analysis. While these parameters are important, our work does not focus on a specific type of network communication and excludes those constraints (i.e., wired versus wireless). Other placement strategies base arrangement on optimization techniques such as genetic algorithms [31, 32] or simulated annealing [22, 33] with objectives ranging from emergency networks [34] to habitat monitoring [25] to surveillance detection [35]. Genetic algorithms and simulated annealing techniques can be prohibitive for complex problems while requiring significant time to compute solutions.
A previous study of great relevance to our objectives was published by Berry et al. [16] in 2004. They developed an efficient integer programming-based technique for detecting attacks on urban water distribution networks and minimizing contaminant delivery to consumers. The goal was to place a number of “perfect” sensors in pipes or junctions of a water network, and the technique decoupled the contaminant transportation problem from sensor placement decisions. While the underlying application and contamination propagation mechanisms in [16] are different from those needed for sensor placement in urban NBC attack scenarios, the mathematical framework can still be used. In our study we apply the framework of [16] to urban airborne contaminant networks that take into consideration the effects of wind, topography, population density, and civilian evacuation dynamics.
The inputs of the sensor placement algorithm we develop here are threat simulation results, population evacuation simulation results, a set of candidate sensor locations (including a detection threshold), and a total cost constraint (i.e., maximum number of sensors to be placed). The states of the sensor placement algorithm are binary variables which represent whether a sensor is placed (1) or not (0). The output of the sensor placement algorithm is the optimal configuration of sensors which minimizes the network's total threat consumption which is defined in Section 3.1.
2.2. Computational Fluid Dynamics
In order to make good decisions on sensor placement in a given three-dimensional environment, a database of fallout dispersion for various attack scenarios in that environment is needed. Here, we use simulation techniques based on computational fluid dynamics (CFDs) and meteorological forecasting models to develop this database for urban environments.
CFD techniques are now widely used in the prediction of complex flow processes in reactive systems [4, 5, 36], fire prediction [5, 6, 37], plasma processing [7, 8], and high-speed flow systems. The application of CFD models in chemical/biological transport problems for an urban setting is new [9, 38] and requires considerably more computer resources than traditional models [39].
The Department of Defense has funded the development of the FAST3D [40], FEFLO [41], and FEM3C [42]. These models are 3-dimensional CFD solvers explicitly developed for urban plume dispersion and transport modeling in complex geometries. The Department of Homeland Security's Urban Dispersal Program [3, 43] aims to improve and validate computer models that simulate the atmospheric movement of contaminants within cities and around, into, and within building interiors [3, 9, 43].
In this paper, we use the Fire Dynamics Simulator (FDS) [17], a CFD program developed by the National Institute of Standards and Technology (NIST). FDS is a multispecies, multivariable, boundary condition CFD program for the three-dimensional simulation of fires and smoke transport based on the Large Eddy Simulation (LES) technique [44–46]. For more information regarding CFD modeling and parameter tuning, see [9, 39, 47–49], and for information pertaining to FDS validation and applicability, see [6, 37, 46, 47, 50–55].
The inputs to the CFD simulations are the terrain where the dispersion will be modeled (i.e., the city model), physical parameters of the NBC agent (i.e., the molecular weight of chlorine), the prevailing wind condition, mesh size, simulation time, location of agent release, and data collection points (i.e., candidate sensor locations). The basic assumptions made by the simulator are (1) prior to agent release—the environment is uncontaminated; (2) during the agent release—the environment becomes contaminated; (3) after the release ends—the agent disperses throughout the environment until it is no longer detectable. The outputs of the simulations are the simulated concentration data at each candidate sensor location versus time and an animation file that illustrates the simulation.
2.3. Assumed Threat
In this study the contaminant gas is chlorine (Cl2). The widespread availability of chlorine and usage in both commercial applications (i.e., water treatment and sanitation of sewage) and in chemical warfare motivates its use in this paper. Exposure to high concentrations of chlorine gas can be fatal to humans. If there was a chlorine gas leak or accident in an urban environment, many people could be at risk of high exposure and consequently severe injury or death. (Chlorine gas can cause pulmonary edema. When inhaled, Cl2 reacts with lung water to produce hydrochloric acid (HCL) [56]. Chlorine gas can be fatal after a few breaths at 1000 parts per million (ppm) [57]. As little as 2.5 mg per liter (approximately 0.085 percent by volume) in the atmosphere can cause death in minutes [57].)
The density of air is 0.00128 g/mL, and chlorine gas is 2.5 times heavier than air (e.g., 0.0032 g/mL) [58, 59]. When chlorine gas is compared to carbon dioxide, chlorine is about 1.6 times heavier than carbon dioxide (smoke). Since chlorine gas is heavier than smoke, we assume that chlorine gas stays closer to ground level and propagates at a slower rate than smoke.
We use the following chlorine gas parameters as inputs to FDS: a molecular weight of 70.9 atomic mass units and a mass fraction of 0.4 (40% chlorine and 60% air). For the purposes of detecting chlorine-based attacks, we assume that available sensor technology allows the detection of chlorine concentrations at 1 ppm which approximates to a concentration threshold of 10−6 Kg/Kg.
2.4. Pedestrian Evacuation
In the event of an attack on an urban area, the distribution of humans in the attack area is of central importance in modeling the overall effect of a released contaminant. Assuming that the attack is apparent (i.e., accompanied by a loud explosion), it is natural to assume that pedestrians would quickly flee from the area of perceived danger. The dynamics of this crowd movement will help estimate the number of individuals exposed to the threat. Applying this model of pedestrian movement over the entire population in an area under attack allows for the calculation of the population density of different areas of a map as a function of time.
For simulating civilian flow, three main models emerge: the fluid approach, flow modeling, and discrete distributed modeling. The fluid flow regards the group of civilians as a single, consistent mass. However, taking into account human behaviors, the forces acting on a fluid would not match that of a crowd of civilians. The flow modeling approach, which is the newest method and still in development, is a derivative of the fluid approach but takes into account the different forces and behaviors that guide crowds. The discrete modeling approach [60, 61] is the most established method of modeling crowds. In this approach, crowd modeling consists of a group of individuals, each with his/her own movement behavior rather than a single mass. Helbing and Molnár present the social force model [60], which shapes particle movement by social rules where the environment and individual behaviors influence crowd dynamics. Reynolds' results [61] show that individuals move in crowd like behaviors with simple rules in place. A majority of discrete distributed modeling [62–64] are based on the work of Helbing and Reynolds.
We considered a number of existing models of population evacuation [60, 61, 64–70]. Most were confined to evacuations of a single building and depended on movement restrictions and behavioral assumptions that may not fit our scenario. We elected to use a discrete distributed model based upon the principles of Cellular Automata (CA), which have been extensively researched in crowd modeling [70–72] and vehicular traffic modeling [73]. There have been several attempts to model the movement of pedestrians based on CA, notably those described in [18, 66, 67, 70–73]. CA modeling is simple and computationally efficient and can reproduce several behaviors exhibited in pedestrian dynamics [18, 72, 73].
CA models are discrete models based on the concept of cells, each one defined with a finite number of possible states. The CA model we employed divided the environment into cells, based on the two-dimensional automata schemes developed by Burstedde et al. [18]. Burstedde's model is arranged such that each cell has eight neighbors (see Figure 2). Each cell is either occupied by a pedestrian or vacant. The state of a cell at any moment in time is determined by the previous state of that cell, the previous states of neighboring cells, and the cell transition functions. The transition functions determine which neighboring cell has the highest probability of being occupied by a pedestrian at the next time step.

Illustration of neighboring cell locations.
The inputs to our civilian evacuation simulations are the initial density of human occupancy in the environment (person/meters2), the attack location, and the values for influence variables,
3. System Model
In the following section, we develop the two key components to our system model: sensor placement and civilian evacuation.
3.1. Sensor Placement Optimization
We build upon the mathematical framework provided by Berry et al. [16]. See Table 1 for a list of symbols and their definitions. Consider a set of “candidate” sensor locations in an urban sensor network,
Symbol table for sensor placement optimization.

The decision variable for our optimization problem is the sensor placement index
Given the above formulation, the objective function for sensor placement becomes




The objective function (2) minimizes network “consumption” of NBC contaminant averaged over a set of attacks. The constraint in (3) enforces that there is exactly one best sensor for each attack. The constraint in (4) enforces that a sensor cannot be the best sensor for an attack if it is not installed, and the constraint in (5) enforces that at most
3.2. Population Evacuation
We use a simplified version of the Burstedde cellular automata (CA) model [18] to quantify civilian population density throughout an urban environment during an NBC attack. Only bordering cells (see Figure 2) may cause a transition from vacant to occupied, and a pedestrian may only move in eight directions (N, S, E, W, NW, NE, SW, and SE).
The model works as follows. The map of the area to be studied is divided into a two-dimensional (x-location by y-location) grid of 40 cm × 40 cm cells. The cell size was chosen to correspond to the amount of space occupied by an average-sized adult. Only one pedestrian may occupy a cell at any given time t. The state of cell
Floor fields are variables associated with each cell that are used by pedestrians to assist in determining their next move. These variables mediate long-range interactions between cells and constrain pedestrian transitions to neighboring cells only. Two different types of floor fields, static (sField) and dynamic (dField), are used to model movement during an emergency. Simulation wide constants are used to determine the level of influence that the sField and dField values have on pedestrian movement.
sFields correspond to movement based on a pedestrian's knowledge of the topology of an area and, therefore, model “intelligent” movement behavior. If a pedestrian knows that a certain direction leads to an exit, the sField value,
dFields correspond to “herding” movement behavior. When a pedestrian is ignorant of the topology of an area, he/she is likely to base his/her movement on the movement of other pedestrians. The dField value of a cell,
A cell 
Once the weights are determined, the variable
In these calculations, i and j are relative to the cell in which the pedestrian currently resides (see Figure 2) and k and l are relative to the cell that the pedestrian might move into. 

4. Simulations
4.1. Fallout Dispersal Prediction
Fire Dynamics Simulator (FDS) was used to obtain simulated data for contaminant dispersal in a three-dimensional domain, which can be seen in Figure 1. Figure 3 shows the computational domain in two dimension: several city blocks in the downtown area of a generic urban environment.
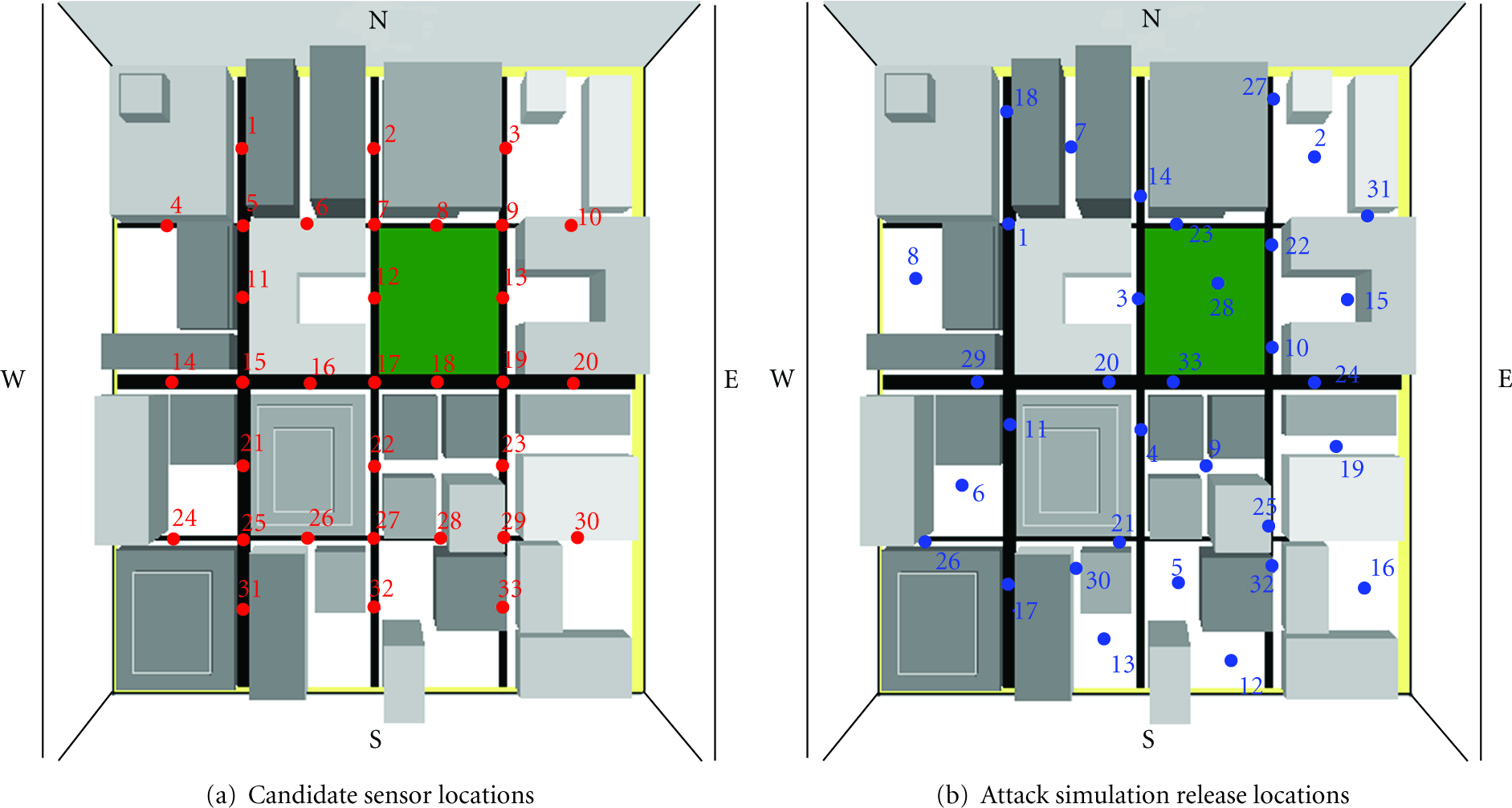
Generic urban environment used for fds simulations shown in 2D.
The urban environment included a city hall, an area of high concentration of humans, with political and symbolic significance. Second, a park (shown in green) was included to show the effect of an open area within an urban canyon on contaminant flow. Also, a central business district consisting of four skyscrapers in one block of the model near the city hall was created. The rest of the model was filled with generic buildings of varying dimensions. The streets, alleys, and other areas of open space between buildings add another realistic feature to the model. The combination of these features allows us to investigate dispersion characteristics of the urban environment, such as the trapping of contaminant in specific areas due to the geometric layout of the environment.
Figure 3(a) displays the thirty-three numbered candidate sensor locations (
Figure 3(b) displays the thirty-three numbered attack locations,
There are thirty-three simulated attacks per attack simulation set
4.2. Human Evacuation
In the evacuation simulator we assumed that the only barriers pedestrian movement were other pedestrians and buildings. We initialized the occupancy of cells in the CA civilian mobility simulation (
Our algorithm for determining the sField value of a cell works in two steps. First, we determine which cell was the origin of the attack and assign it the cell location 
In Figure 4(a), we illustrate contours of constant sField values as concentric circles about the origin of attack. These concentric rings create a movement gradient such that pedestrians will flee directly away from an attack, where the blue rings correspond to low values of
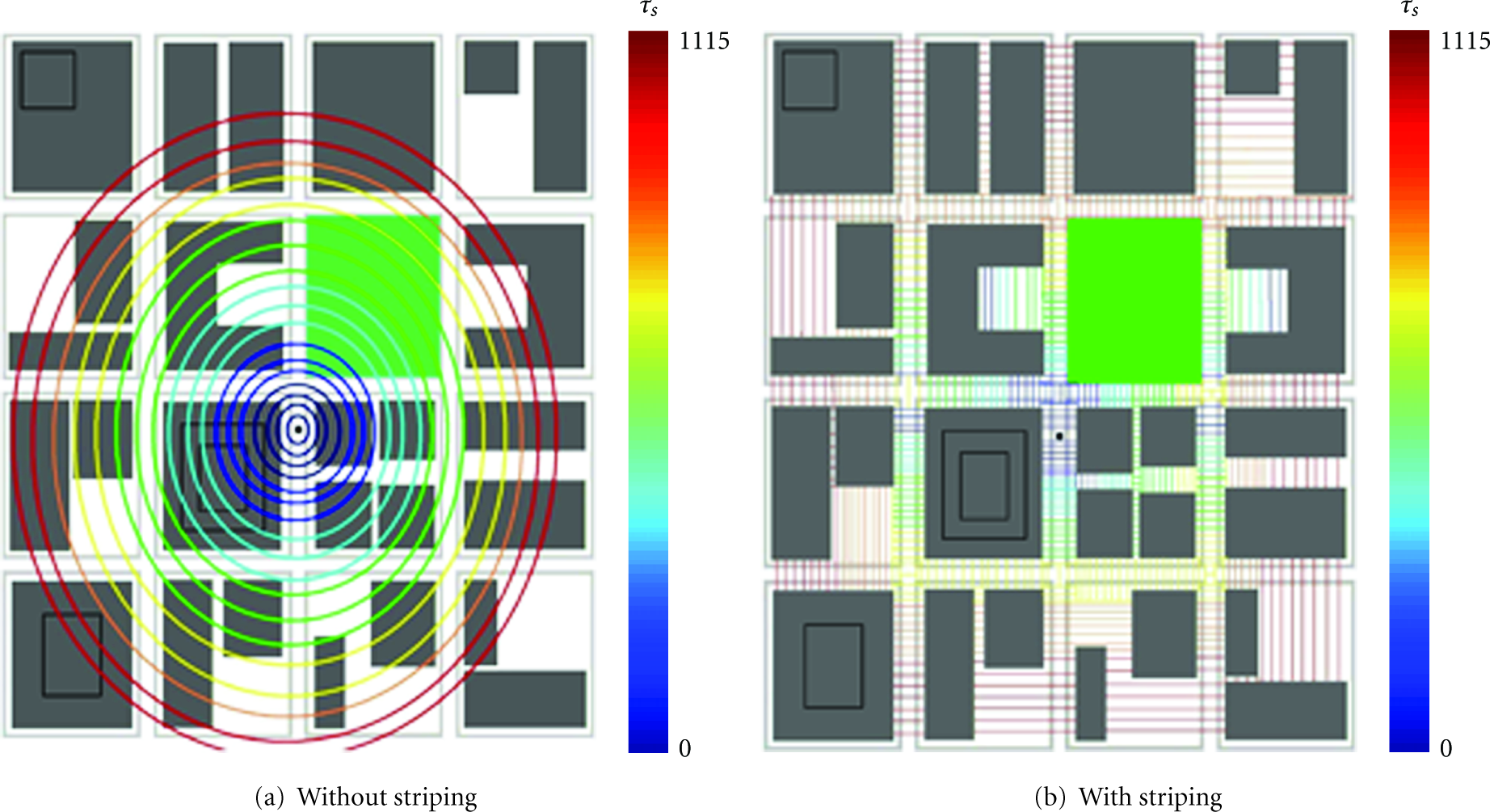
2D illustration of sField calculation for attack location using.
sField computation is modified to eliminate these undesired behaviors using a technique called striping. Allowed movement paths are divided crosswise into stripes. For each stripe, each 1 cell wide, we locate the cell with the largest sField value and assign all the cells within the stripe with that value. Striping warps the concentric rings formed by the first step of the algorithm as illustrated in Figure 4(b). This warping retains the general trend of moving pedestrians away from the center of an attack and enforces practical constraints on the avenues of evacuation.
5. Results
We present the results below in the following organization. First, the fallout dispersion results are presented. Next, we describe the effect of sensors on “Network Consumption.” Then we present the results of civilian evacuation. Finally, the sensor placement results are described, such that, first we discuss the sensor placement against static population and then against a variable population.
5.1. Fallout Dispersion Results
Figure 5, which is a two-dimensional snapshot of our three-dimensional urban terrain, illustrates the dispersal of the chlorine gas during

2D Illustration of chemical agent propagation in urban environment during attack

Chemical agent concentration data versus time with detection time and sensor detection threshold during attack 4, (
In Figure 6(a), the contaminant concentration fluctuates as a result of the urban terrain and the prevailing wind. The product of the concentration data shown in Figure 6 and the population density,
5.2. Effect of Sensors on Network Consumption
We performed mathematical optimization to solve the problem using the AMPL Modeling Language for Mathematical Programming [74] in concert with the linear solver, LP_SOLVE [74] (collectively referred to as AMPL), to solve the optimization problem formulated in (2)–(5). In doing so, we calculate the optimal placement of sensors for networks containing up to
Figure 7 shows the change (lower is better) in network chemical agent consumption versus

Total consumption of contaminants in the network (prior to attack detection) versus the total number of available sensors (
Detailed tables showing the various configurations and consumption values for the three scenarios and for configurations containing up to twenty sensors can be found at [75].
5.3. Civilian Evacuation Effects
Figure 8 shows the graphical output of our population evacuation simulation for the attack pictured in Figure 5. Here, the red dot indicates the origin of the attack and black dots indicate individual pedestrians. Figure 8(a) shows the initial distribution of pedestrians, distributed randomly along roads and in the park, at the start of the attack. Figure 8(b) shows the evacuation of the population after 150 seconds with pedestrians scattering away from the source of the attack. The results of this simulation were used to calculate
Symbol table for population evacuation.

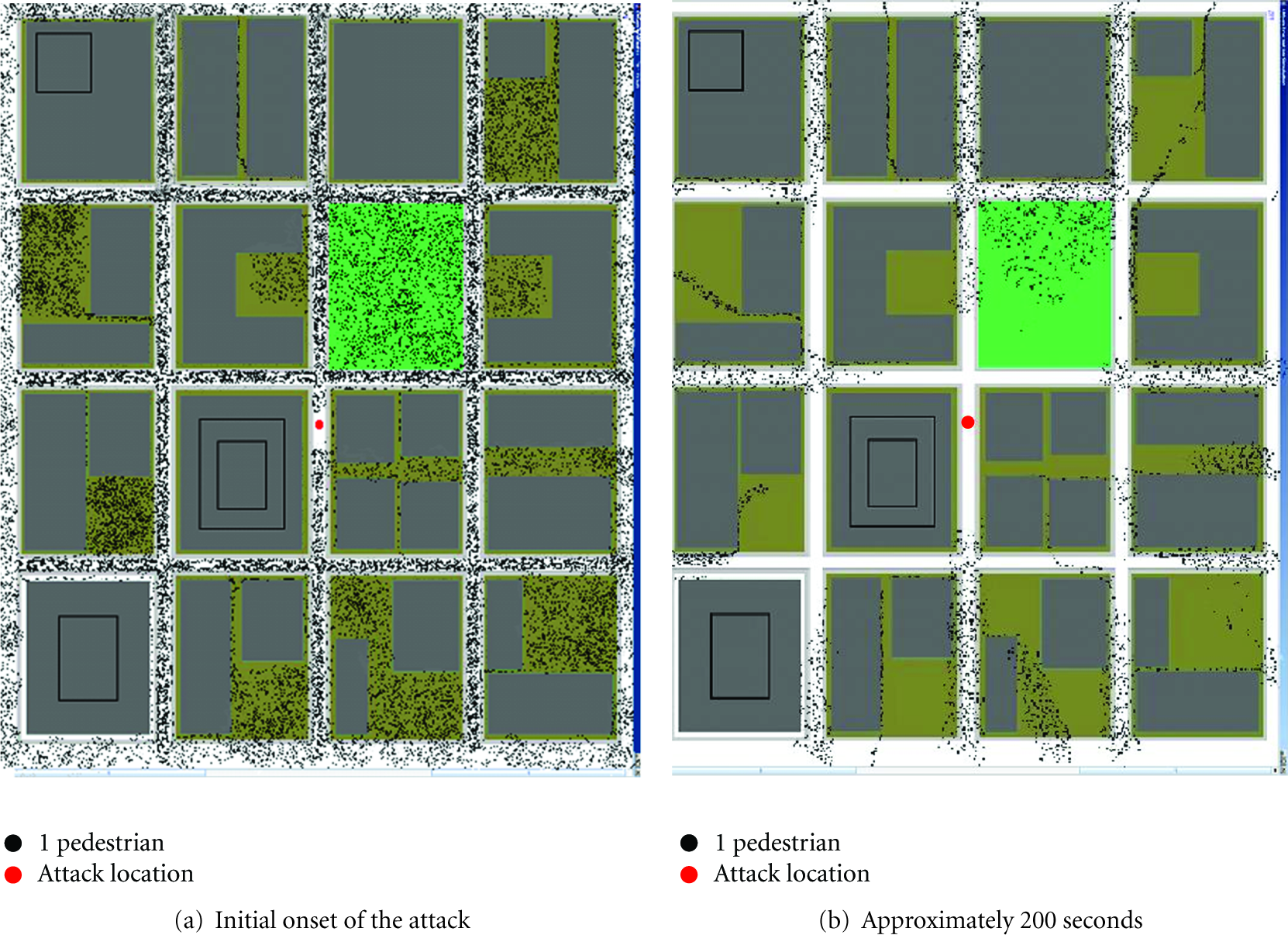
Simulation of population evacuation during the attack illustrated in Figure 5 at.

Graph of population density versus time for
5.4. Sensor Placement Results
5.4.1. Optimal Sensor Placement for Static Population Density
The consumption values, along with the configuration of placed sensors, are shown for each attack simulation set (
Configurations of sensors for a static population:

It is noted that there are relatively few sensors that are common to the optimal configuration of sensors for all three attack simulation sets (i.e.,
Sensors would have to be moved based on the predicted long-term wind patterns to achieve optimal performance. Seasonal movement of sensors is consistent with the military strategy known as “Sense-and-Respond” logistics [76, 77]. If the set of sensors in
As shown in Figure 7, it is desirable to have at least ten sensors placed in the network. By merging all three sets of attacks together and optimizing our network configuration, for a set of 10 sensors, a year-long configuration shown in Table 4 was found. The consumption for this yearlong configuration, 1.602, is significantly lower than the sum of consumptions for
Yearlong configuration of 10 sensors for a static population.

5.4.2. Optimal Sensor Placement for Variable Population Density
Up to this point, we assumed that the population density,
Next, rather than using the sensor configurations found in Section 5.4.1 we used AMPL to solve our constrained placement equations taking into account variable population results. Table 5 shows the sensor arrangements as given by AMPL for
Configurations of 10 sensors for a variable population.
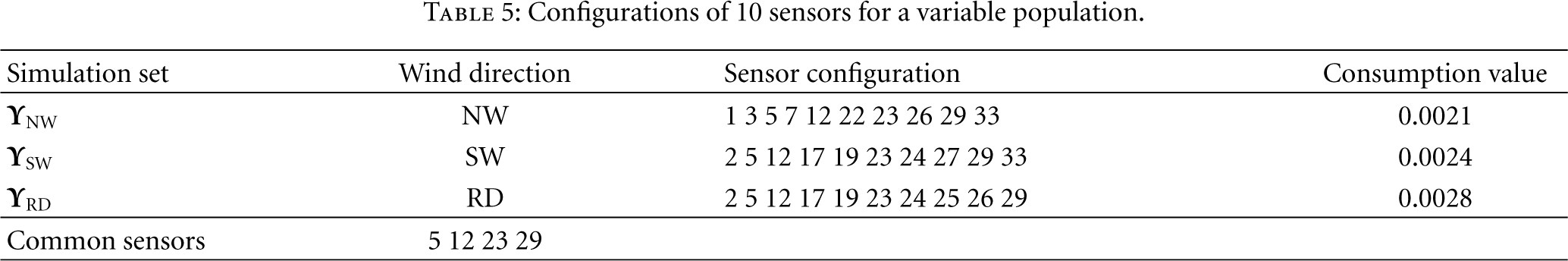
The sum of normalized consumptions for the configurations calculated using the variable population results was 0.0455. This value is less than one tenth of what we found by simply using a static population model.
This difference underscores the importance of taking into account pedestrian movement. The evacuation of pedestrians in our simulation resulted in a considerably lower consumption, and the methodology allows for comparison of different evacuation regimes and demonstrates the effect of a moving population when placing sensors. Table 6 shows sensor placements common between the two population models. While eight out of ten sensors are in common under the random wind scenario, only about half of the sensors coincide between the two sets of data in the other two scenarios.
Common sensor configurations between the static and variable population types.

6. Conclusions
We have quantified the benefit of additional sensors on the population and threat response time in an urban center and found that detailed modeling and monitoring of the prevailing winds in the urban area can greatly improve the effectiveness of the sensor placement algorithm. Our results indicate that sensors may have to be moved from location to location, based on seasonal wind patterns, in order to achieve optimal performance. Seasonal movement of sensors is consistent with the military strategy known as “Sense-and-Respond” logistics.
By incorporating pedestrian evacuation simulations based on CA into our problem formulation, a significant reduction in the value of consumption was achieved. More importantly, evacuation models changed the way we placed our sensors and improved overall performance (i.e., reduced contaminant consumption).
The most important observation made by this paper is that modeling of threats and population evacuation has a significant effect on the design of an effective sensor network. Urban NBC sensor network design is also sensitive to wind direction and details of the urban environment.
Footnotes
Acknowledgment
An earlier version of this work appeared in the Proceedings of the 2006 IEEE International Workshop on Measurement Systems for Homeland Security, Contraband Detection and Personal Safety.

