Abstract
Petrochemical pipelines have taken center stage in public debates about the impacts of resource extraction dependencies and calls for greater participation in environmental governance. However, these concerns can run counter to the interests of the petrochemical industry and state security imaginaries that frame critics as threats. These imaginaries are evident in a suite of critical infrastructure (CI) trespass bills introduced by U.S. state legislatures implicating the activities of anti-pipeline protest movements. In a comparative analysis of 51 CI trespass bills, we find significant patterns in how criminal activities are defined across bills, as well as how individuals, aiding organizations, and the tactical practices of activists are positioned as threats. Additional findings show that CI trespass bills are more likely to emerge from states with heavy investments in pipeline infrastructure, states with contested pipelines, and states dominated by conservative political parties. Finally, we illustrate how major components of bills are authored by the American Legislative Exchange Council, a group that supports the interests of petrochemical companies. We argue that, by broadly designating those who resist pipelines as threats, trespass bills serve to strengthen petro-security state powers, thus transforming sites of resistance to petrochemical development into sites of acceptable risk for the externalities of free market industrialism under the pretense of protecting national security. We suggest that these developments may have multiple negative effects, including eroding the public's right to question pipelines and exacerbating patterns of social injustice, as well as unintended positive effects in strengthening organized resistance.
INTRODUCTION
Oil and gas pipelines have become acute battlegrounds in contemporary public discontent with resource extraction dependencies, the impacts of the petrochemical industry, and calls for more meaningful participation in environmental governance. However, these concerns frequently run counter to the interests of the petrochemical industry and its supporters, who view critics as working to undermine national security and economic stability.
One manifestation of these contestations can be found in a suite of trespass bills being introduced by U.S. states to criminalize activities deemed threatening to critical infrastructure (CI). These bills varyingly define CI to include such things as telecommunication systems, electrical grids, chemical plants, military bases, prisons, and agricultural facilities. Petrochemical pipelines are also consistently included in CI definitions, explicitly and implicitly, and are frequently the instigating reason for legislative actions.
This article investigates 51 CI trespass bills to understand how these bills are implicating resistant publics deemed threatening to pipeline infrastructure, as well as how CI trespass bills are shaped by historical and new petro-security state power alliances. Through comparative content analysis, we find significant patterns in how CI and criminal activities are defined across bills, as well as how individuals, assisting organizations, and specific tactical practices of activists are positioned as threats. Many bills build on previous state laws to increase trespassing penalties from minor fines to felonies, as well as extend trespass liabilities to include persons or organizations seen as aiding from the margins.
CI trespass bills are also targeting activities important to community-watchdog efforts, such as civilian use of drones and photography to document permit violations and accidents. Using geospatial analysis, we furthermore find meaningful patterns in where CI trespass bills have emerged, such as from states with heavy investments in pipeline infrastructure, states primarily—but not exclusively—dominated by Republican Party governors and legislatures, and states with contested pipeline projects within their borders. Finally, our analysis reveals how CI trespass bills consistently implicate language provided by a 2017 model bill developed by the industry-entangled American Legislative Exchange Council (ALEC).
Although these bills have received significant attention in investigative media, 1 , 2 , 3 , 4 , 5 our study interrogates CI trespass bills to offer a unique contribution to the research on coordinated state legislative efforts to limit the activities and rights of environmental activist movements. In reflecting on our findings, we suggest that CI trespass bills implicating pipelines represent only a recent chapter within a longer history of actions by state powers to portray spaces of civil disobedience as sites of resistance to national security and economic stability, while mobilizing state security systems to make such sites acceptable sacrifice zones in the interest of promoting free market industrialism. 6 , 7 However, we argue that, although CI trespass bills have significant potential to erode the public's right to contest pipeline projects, they may also have unintended generative effects that strengthen resistance to the petro-security state.
CI and petro-security state power
Acts to physically disrupt the operation of pipelines are not unheard of in the United States. Several isolated attempts have caused physical damage with rudimentary explosive devices. 8 In other cases, direct action by protesters has stopped the flow of pipelines by turning off emergency shut-off valves—groups that have been independently organized around the name “valve turners.” 9 A 2021 ransomware attack against the Colonial Pipeline, and its resulting gas shortages throughout the Northeast United States, is only a recent instance demonstrating real cybersecurity vulnerabilities within the industry. 10 However, the overwhelming majority of pipeline-related safety incidents in the United States are caused by equipment failure, operator error, excavation accidents, and natural forces. 11
More than 5,500 such incidents have been reported by the Pipeline and Hazardous Materials Safety Administration since 2010, accounting for 596 injuries, 126 fatalities, and cumulative damages (to infrastructure, environment, and property) estimated at more than $4 billion. 12 Nevertheless, a series of congressional and industry reports have entangled the daily risks of commonplace pipeline safety incidents with the perceived malicious intents of environmental activists. 13 , 14 , 15
In the United States, regulations protecting large-scale infrastructure date back to the 1940s, but the genealogy of present-day security imaginaries attentive to “critical” infrastructure can be traced to at least three historical milestones, first, as a direct result of the Strategic Bombing Survey analyses performed by the American military during the Cold War. When identifying potential targets of Soviet aggression, factories and petrochemical refineries, in particular, were prioritized over other assets of public importance, such as health care systems. 16 The 1973 oil crisis, and the 1979 energy crisis, galvanized attention to petrochemical infrastructure threats, where large transmission pipelines were seen as likely targets for international terrorist groups. 17
Second, concerns generated by growing U.S. strategic reliance on computing and networked information systems resulted in the Clinton Administration's 1997
CI trespass bills are a direct expression of these evolving security imaginaries, entangled with additional state ambitions to frame environmental activists as eco-terrorists in the 1960s and 1970s. As Hasler
Animal rights, anti-nuclear, and environmental protection activists utilizing disruptive tactics to oppose industrial development projects (such as Earth First! and the Earth Liberation Front) were increasingly pursued by the U.S. Justice Department, which later extended terrorist-related laws to protect private material property beginning in the 1980s. 22 , 23 , 24 , 25 In a parallel continuation of prosecutorial legacies aimed at social justice groups, such as the Black Panthers, the American Indian Movement, and other civil rights activists of the 1960s and 1970s, state security responses to Occupy Wallstreet and the Black Lives Matter movement have similarly extended political appetites to apply terrorist-related laws to progressive protest movements. 26 , 27
As has been observed in the United States and elsewhere, collaborations between the state and environmentally damaging industries create mutually beneficial security partnerships for the purpose of securing sacrifice zones for the ecological and social exploits of free market industrialism. 28 , 29 , 30 , 31 Petrochemical pipelines are poignant sites of these accepted externalities, where a growing body of research has scrutinized the distributional, procedural, and recognition-based justice issues that are systemic to pipeline infrastructure buildouts. 32 , 33 , 34 , 35 , 36
Pipelines have also established new acceptable sites for petro-security state powers to justify the use of surveillance and suppression tactics against dissenting publics. 37 These injustices are felt across the U.S. oil and gas landscape, but they are most acutely experienced by historically marginalized groups—and particularly demonstrated by the questionable practices of constructing pipelines on Indigenous lands. 38 , 39 , 40
However, pipeline fights have also demonstrated the power of resistance in tangibly altering the trajectories of pipeline projects, as well as in raising broader public awareness of petrochemical industry operators and their ambitions. 41 , 42 As the CEO of the pipeline company Enbridge, observed, “Fifteen years ago nobody cared that much about pipelines, today pipelines are under siege.” 43 We argue that CI trespass bills are a product of this realization, wrapped in the cloak of security imaginaries refined to see resistance as a malicious threat.
METHODS
The CI trespass bills examined in our study were identified by using multiple sources, including the International Center for Non-Profit Law's (ICNL) exemplary “US Protest Law Map,” 44 the nonprofit “LegiScan” website that tracks legislative actions, 45 and individual states' legislative session activity bulletins. The CI trespass bills that did not explicitly mention pipelines, or infer pipelines through broader language referencing petrochemical facilities, were excluded from our analysis.
One executive order, issued by North Dakota's governor in 2017 (EO2017-01), was discovered in our research. We recognized that this order was issued to force evacuation of Dakota Access Pipeline protest camps at Standing Rock under the pretense of protecting occupants from the risks of spring flooding. However, given that the order did not explicitly reference CI or pipelines/petrochemical facilities, it was also excluded from our analysis. The final scope of our data collection resulted in an analysis of 51 bills pertaining to senate and house legislative actions in 28 states between January 2016 and June 2021.
Our analysis includes four components. First, we assembled extensive dossiers tracking the progress and contents of the 51 bills. Bills were categorized as “enacted” (passed by both legislative branches and signed into law), “pending” (in process, but not yet enacted), or “failed” (defeated in process, or having died before the end of the legislative session). Second, the 51 bills were comparatively coded by using MAXQDA software to determine variations and similarities in language defining CI, criminal activities, and liabilities. A second round of coding was conducted to then determine similarities between the 51 bills and the 2017 ALEC “Critical Infrastructure Protection Act” model bill. 46
Third, using public data provided by the National Conference of State Legislatures, 47 we documented which political parties held majorities in state legislatures and governorships during the time that bills were introduced. Finally, using spatial data from the U.S. Energy Information Administration, 48 we calculated the total number of pipeline miles contained within all 50 states, in addition to the total miles of 63 pending and under-construction pipelines known to be “contested” by the authors from ongoing research (defined as having produced significant anti-pipeline protest activities during the lifespan of the project). 49
RESULTS
Figure 1 presents a timeline of CI trespass bills by state and bill numbers. Twenty-one bills have been passed into law, another 9 remained pending at the end of our analysis window, and 21 bills failed to pass. This timeline suggests some initial patterns. As has been suggested in several media investigations, 50 , 51 , 52 , 53 the Dakota Access Pipeline Standing Rock protest camps appear to be a major instigator for the introduction of new bills attempting to criminalize public dissent, including OK HB1123—introduced in 2017 and used as a template for the ALEC model bill. 54 A second wave of bills follow in the wake of the 2018 congressional elections and has continued throughout 2021.
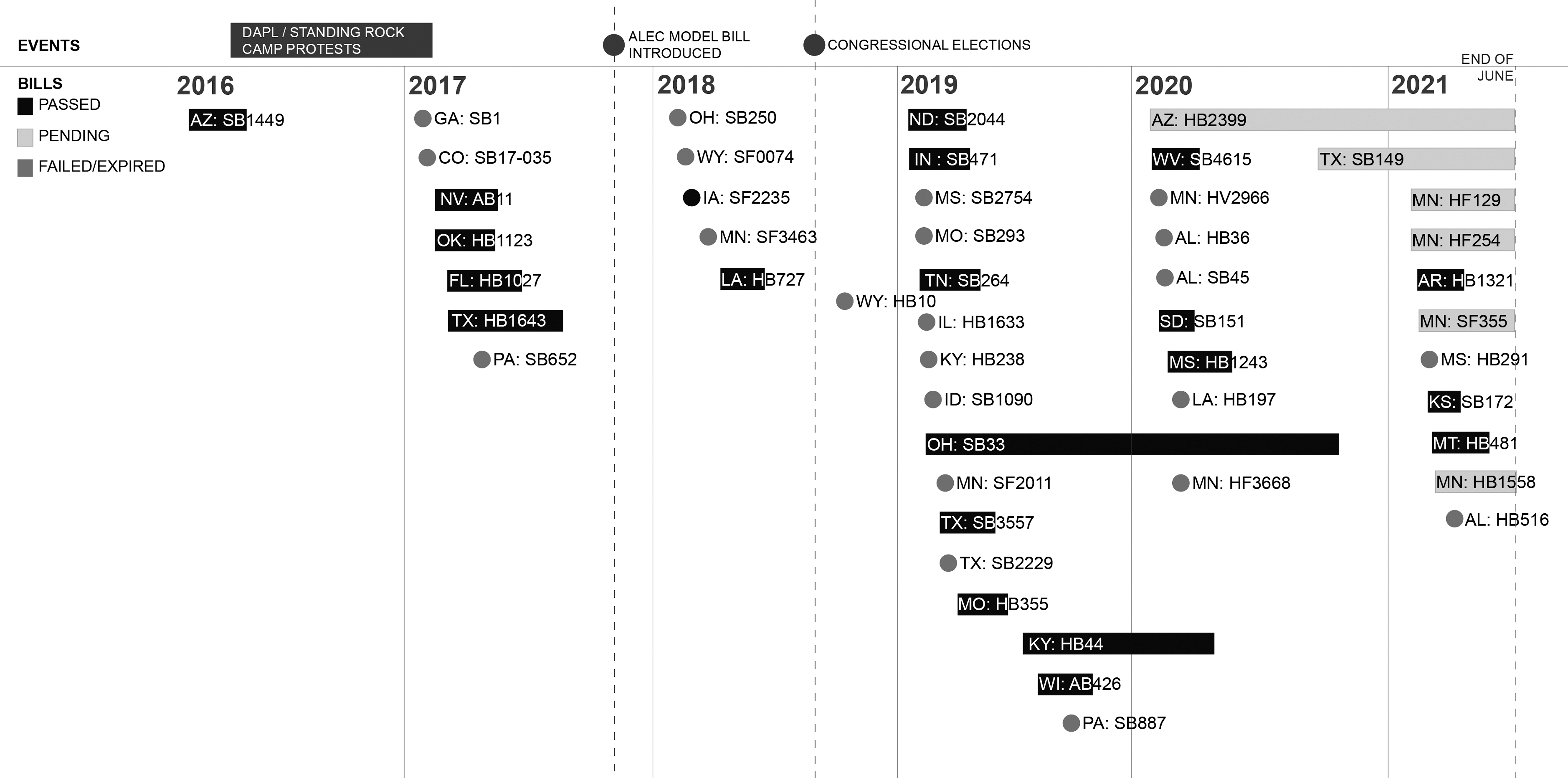
Timeline and status (as of June 2021) of 51 CI trespass bills. Dots represent bills that received immediate legislative action. Bars represent bills debated over longer timelines. CI, critical infrastructure.
Table 1 outlines the frequency of commonly used sub-definitions for CI found across the 51 bills (0–51 occurrences), their pertinence to pipelines and/or petrochemical facilities, and whether or not the language was taken verbatim from the ALEC model bill. Although our research discovered 56 different sub-definitions of CI, including commercial maritime vessels, public stadiums, and even “anything with a fence and/or signage” (MS HB291), Table 1 is limited, in order of frequency of appearance, to duplicative language found in 10 or more bills, followed by 6 less common sub-definitions that we found were pertinent to pipelines (23, 27, 28, 29, 37, 39). What is immediately clear from Table 1 is the centrality of pipeline-related sub-definitions within the CI trespass bills, through either explicit mention or encompassed within broader references to petrochemical facilities.
Content and Frequency of Critical Infrastructure Sub-Definition Language Across State Bills, Their Relevance to Pipelines, and Their American Legislative Exchange Council Model Bill Origins
ALEC, American Legislative Exchange Council.
Table 2 offers additional details on the nature of the 51 CI trespass bills, including their thematic focus (on individual trespass offenders and/or the use of civilian drones), crime designations (misdemeanor and/or felony), potential financial liabilities (to the individual, and/or aiding organizations and individuals), and an ALEC model bill language commonality score (16/16 having all of ALEC sub-definitions listed in Table 1).
Critical Infrastructure Trespass Bills by State, Bill Focus, American Legislative Exchange Council Commonality, and Party Dominance When Introduced
ALEC, American Legislative Exchange Council.
We found that the overwhelming majority of bills in our study model legacy trespass laws, which focus on the actions of individual offenders. We also found evidence of how security imaginaries are changing to include more abstract interpretations of trespass, such as the use of technologies. Nearly 25% of bills directly reference the use of civilian drones, such as KY HB44 (enacted in 2019), which states, “A person commits the offense of trespass upon key infrastructure assets if he or she knowingly uses, or retains or authorizes a person to use, an unmanned aircraft system to fly above real property on which key infrastructure assets are located.”
The range of penalties associated with trespass—physical and virtual—was found to be quite broad, from misdemeanors and felonies, to even hard labor (KY HB238, LA HB727, LA HB197) and potential death penalties (GA SB1). Finally, our research suggests that security imaginaries are also expanding to define organized coalitions as threats from the margins. For instance, MN HF3668 defines “conspirators” as those who recruit, train, aid, advise, hire, or counsel those who commit trespass. Nearly half of the bills in our research outline similar liabilities, with fines reaching as high as $1 million.
In addition to examining the contents of 51 CI trespass bills, a primary goal of our study was to identify geospatial similarities across the 28 states that had introduced these bills. Our analysis began with an examination of the total number of pipeline miles for all 50 states. To calculate these miles, we first utilized PHMSA data 55 for 301,954 transmission and 17,304 gathering pipeline miles (omitting the 1.9 million miles of smaller distribution pipelines in the United States that deliver natural gas to commercial and residential customers).
We found that all of the top 10 states by total number of pipeline miles (TX, OK, LA, KS, IL, OH, WY, PA, MS, CA), with the exception of CA, have introduced CI trespass bills. Meanwhile, only two states (ID, AK) of those with the lowest number of total pipeline miles (HI, RI, VT, DE, NH, CT, MD, AK, ME, ID) have introduced bills. We similarly calculated the total miles for 63 pending and under-construction “contested” pipelines and found that, out of the top 10 states in this category (PA, TX, OH, LA, WI, MI, WV, IL, ND, VA), all but 2 (MI, VA) have introduced bills.
Our findings suggest strong correlations between states with heavy investments in large pipeline infrastructure projects and the introduction of CI trespass bills. Figure 2 visually illustrates these relationships, where “enacted” states have passed at least one bill, “pending” states have no enacted bills but are considering ones, and “failed” states have no enacted or pending bills but have debated bills in the past.
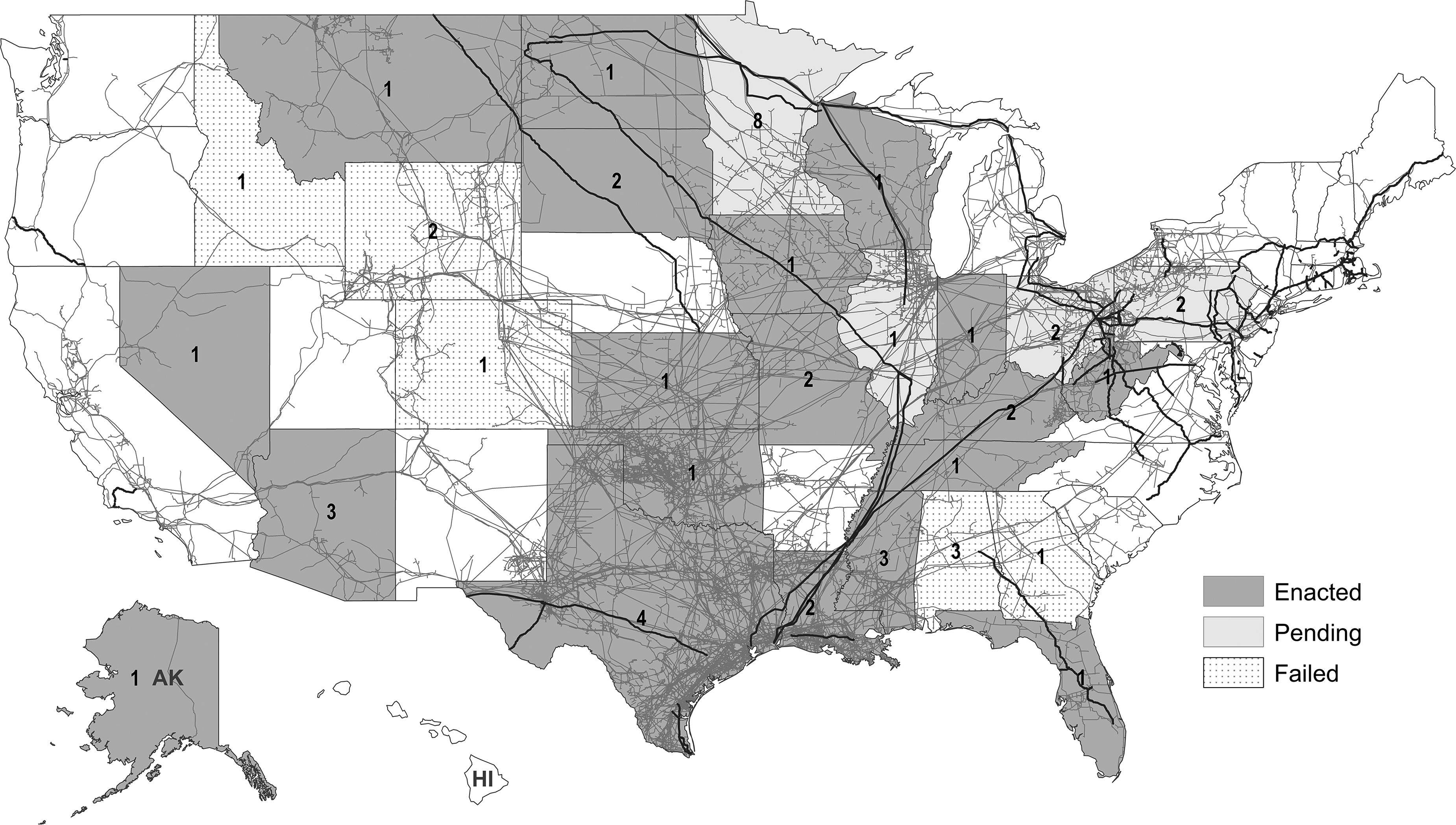
CI trespass bills relative to transmission pipeline infrastructure with “contested” pipelines shown in black (locations of gathering pipelines not shown).
Additional patterns were identified in states that have introduced CI trespass bills and state political party dominance, as represented in Table 2: (D)emocrat, (R)epublican, or (S)plit (in the case of some legislatures). The F/P/H abbreviations in the Table 1 legislative column further denote whether or not that state's legislature is (F)ull-time and well-resourced, (P)art-time with a few staff and resources, or (H)ybrid-time and meeting roughly two-third full-time. 56
We found that 71% of bills (36) were introduced in states with Republican governors and Republican legislatures. Of the 15 bills introduced in states with Democrat governors, 33% had Republican legislatures, 54% had Split legislatures, and 13% had Democratic legislatures.
These findings come into sharper focus when examined alongside the potential influence of the ALEC model bill developed for legislatures in 2017. As detailed in Table 1, 16 of the 19 most commonly used sub-definitions found across 10 or more bills were take verbatim from the ALEC model bill. Of these, nine apply directly or indirectly to pipeline infrastructure. The ALEC commonality scores (Table 2) were calculated for each of the bills and 43 were found to have some verbatim language taken from the ALEC model bill.
Very high commonality scores of 15 out of 16 were associated with 11 bills, most of which emerged from the earlier mentioned states with heavy investments in pipeline infrastructure (8 of the 11 bills) and those with contested pipelines within their borders (6 of the 11 bills). As was the case with the stronger correlations between states introducing bills and the presence of Republic Party dominance, similar patterns were found with increased ALEC commonality scores within bills passed by Republic Party dominated states, by a margin of more than 2:1.
Finally, although 86% of bills were introduced by states with Part-time (14) or Hybrid-time legislatures (30), we did not find significant correlation in whether or not those bills were more likely to use verbatim ALEC language, suggesting that the relative availability of legislative resources is not as strong a factor as others examined in our analysis.
DISCUSSION
In conducting a comparative analysis of recent legislative actions to enact CI trespass bills, we have offered novel empirical insights into state efforts to use security framings to limit the rights of publics who resist pipeline projects. Although none of the CI trespass bills that we analyzed contained specific language mentioning anti-pipeline protesters, overwhelming evidence supports this correlation—including the timelines of CI bill introduction dates relative to major pipeline resistance events, and numerous instances of pipeline executives, legislative officials, and ALEC representatives publicly stating that the purpose of CI trespass bills was to deter pipeline “vandals,” who are framed as the “poster child” for why legislation action was needed. 57 , 58 , 59
Several themes emerge from our findings that highlight how CI trespass bills pose new dangers to opponents of the petrochemical industry. Many bills explicitly mention pipelines. However, significantly more contain vague references to activities and facilities simply “maintained” by the petrochemical industry. Given the near-ubiquitous presence of petrochemical infrastructure in the United States, abstract definitions may be used to suppress dissent in a variety of settings tangentially related to pipelines, or where pipelines have yet to even be built (such as in proposed rights-of-way). Ambiguous language also includes lack of distinctions between private and public property. This is significant given that numerous cases exist where landowners have been persecuted for protesting eminent domains on their own property. 60 , 61
The singling out of particularly effective tactical practices in resistance movements, such as the use of civilian drones, is a second problematic feature of CI trespass bills. Drones are an increasingly popular tool for collecting data about the petrochemical industry, from environmental sensing to producing high-resolution documentation of accidents, violations, and policing tactics used against protesters. 62 , 63 , 64 , 65
These forms of public monitoring are effective for rearranging power dynamics and have resulted in regulatory fines, revoked permits, and news-ready footage. As has been observed by legal scholars, state drone laws are vastly more restrictive than laws dictating the use of hand-held cameras and monitoring devices, 66 which leads us to conclude that language addressing drones in CI trespass bills are an acknowledgment of the power of counter-surveillance in spaces that would otherwise be unobservable and inaccessible to the public.
Going beyond individual trespass offenders to also target association liability represents a third area of concern in CI trespass bills. Extending liabilities to “conspiring” organizations provides traction for aggressively pursuing advocacy groups and technical resource providers that build capacity in historically marginalized communities opposing petrochemical infrastructure projects. Although legal reviews question the constitutionality of extended liabilities in CI trespass bills, 67 their inclusion may have a chilling effect within environmental coalitions as groups examine their vulnerability when providing even the most innocuous of support.
However, CI trespass bills may also have unintended generative effects. As Pellow has observed of past activist movements, criminalization of protesters did not necessarily destroy these movements, but instead aligned social justice, welfare, and civil rights organizations persecuted by the state. 68 Early evidence from a survey conducted by the authors in 2021 of nearly 100 organizations opposing pipelines suggests similar patterns. Some 30% of respondents reported that CI trespass bills had impacted their work, but they also noted that they were now a part of organized efforts to defeat these bills. 69
Finally, our study reveals close working relationship between petrochemical companies and state legislatures brokered through ALEC, perhaps the most direct indication that recent CI trespass bills are deeply tied to the strengthening and alignment of petro-security state powers. However, the language dissemination patterns we recognized within CI trespass bills are not unique. Scholars have found similar patterns in how ALEC model bills were foundational to neoliberal legislative reforms in public educational, Stand Your Ground laws, and anti-sanctuary city policies. 70 , 71 , 72
The ALEC's involvement is notable in our case, not only for its role as a super-node within a network of ideologically aligned policymakers, but also for its deep funding entanglements with the petrochemical industry. Although it would be tempting to presume that forwarding CI trespass bills to protect petrochemical industry interests in partnership with ALEC are solely the work of conservative politicians in the United States, our findings show that these bills emerge from within Democratic Party dominated legislatures as well—particularly in states experiencing contested pipelines—accentuating how CI trespass bills are deeply embedded in national security imaginaries, popular across the political spectrum, that value free market industrialization over the rights of dissenting publics.
CONCLUSION
Protecting CI is undoubtedly important to U.S. economic and national security interests. However, although recent state legislative CI trespass bills are proposed to ensure public protection, these bills are the product of security imaginaries that frame infrastructure as sites of political and military contestation, where environmental activists are existentially framed as ideological eco-terrorists. By broadly designating those who resist pipeline infrastructure as threats to national health and well-being, CI trespass bills serve to strengthen petro-state security powers that embody these imaginaries.
In doing so, these bills amplify the centralization of material assets as legislatively protected sites of acceptable risk for absorbing the externalities of petrochemical development at a time when climate change and energy transition concerns are at the forefront of national debates. However, CI trespass bills may also reinforce resistance not only to pipelines, but also to the unjust racist, capitalist, and colonialist state practices that have historically supported these projects.
Footnotes
AUTHOR DISCLOSURE STATEMENT
No competing financial interests exist.
FUNDING INFORMATION
This work was funded by the JPB Environmental Health Fellowship, a program of the Harvard T.H. Chan School of Public Health and the JPB Foundation.
