Abstract
Designing secure sensor networks is difficult. We propose an approach that uses multicast communications and requires fewer encryptions than pairwise communications. The network is partitioned into multicast regions; each region is managed by a sensor node chosen to act as a keyserver. The keyservers solicit nodes in their neighborhood to join the local multicast tree. The keyserver generates a binary tree of keys to maintain communication within the multicast region using a shared key. Our approach supports a distributed key agreement protocol that identifies the compromised keys and supports membership changes with minimum system overhead. We evaluate the overhead of our approach by using the number of messages and encryptions to estimate power consumption. Using data from field tests of a military surveillance application, we show that our multicast approach needs fewer encryptions than pair-wise keying approaches. We also show that this scheme is capable of thwarting many common attacks.
Introduction
Wireless technology has seen remarkable growth in the past decade [1, 2]. Low cost, low powered sensors with reasonable processing power have become a reality. A sensor network is a dense mesh of low cost devices that collect and propagate information to a remote user community. Security is a major concern as adversaries can manipulate these sensors to disseminate incorrect information [3, 4]. Secure information exchange between two nodes requires a secure communications pipe between the nodes.
Point-to-point communication schemes use a separate encryption key for every pair of nodes. In
this type of environment, each node must either maintain a minimum of
(
Secure packet forwarding can be done in two ways. One way is to decrypt and re-encrypt the packet at every hop. If a message takes multiple hops to reach the recipient, which is typical for sensor networks, a large number of encryptions and decryptions will drain the node power reserves. Another way is using the scheme in [5], where a packet is encrypted once for every recipient and decrypted locally by each recipient. This assumes that the routing information is kept as plain text. In the seminal document on sensor network security [6], the NAI Labs studied many key management protocols for sensor networks. They found traditional secret key protocols inflexible for managing group membership and refreshing cryptographic keys. They also found RSA based public key protocols too power hungry for use in sensor networks. It has yet to be established whether or not elliptic curve public key cryptography also has excessive power needs.
Since public key approaches appear unsuited to use in sensor networks, authentication has been attempted by placing secret keys on the devices. To mitigate the security damage caused by secret keys being exposed when the nodes are physically compromised, Eschenauer et al. [7] proposed random key predistribution (RKP). In RKP a large pool of keys is generated and each node is provided with a small number of keys randomly chosen from the pool. Nodes with keys in common can communicate securely. In that paper, they explain how to revoke keys on compromised nodes; however, they do not discuss how to detect when these nodes are compromised.
Many extensions to RKP have been proposed. In [5], the nodes authenticated using RKP use multiple disjoint
communications paths to negotiate new point-to-point keys. This has a number of drawbacks: the number of communications required seems excessive and as with public key systems each node has a key for each partner, limiting the scalability of the
approach.
Another extension to RKP that establishes keys for point-to-point communications is given in [8]. They improve on the results in [5] but do not solve the scalability issue associated with pair-wise key management schemes.
Unfortunately, most sensor network applications are data-centric and map poorly to point-to-point communications schemes [9]. Applications are interested in data describing geographic regions, thus the specific node used to collect data is of absolutely no importance. The multicast key management approaches given in [10] and [11] map better to this application domain. These approaches were developed for use in mobile communications systems and use binary trees to efficiently distribute and refresh secret keys. Unfortunately, the approaches in the literature do not deal adequately with the problem of node authentication for sensor networks.
In this paper we show how to use RKP to authenticate nodes and initialize a multicast key management infrastructure in a sensor network. In our approach, a network of nodes deployed at random using the authentication approach in [7] self-organize into a set of multicast regions. Our distributed system is capable of identifying and counteracting several important classes of attacks. We use data from a military sensor network prototype [9] to quantify the power requirements of this approach and find that, for that specific application, it requires about 10% of the energy budget required by existing point-to-point security methods.
Figure 1 summarizes our approach. RKP bootstraps network security. Authenticated sensor nodes collaborate to create secure multicast regions. Geographic regions have local multicast keys. Local key sharing allows applications to support data-centric concepts and reduces communications overhead. Keys are refreshed periodically. We show how to identify and remove compromised nodes from the network.

Flowchart of sensor network security approach presented in this paper.
The paper is organized as follows. Section 2 gives an overview of our approach and explains how the network self-organizes to support multicast communications. Section 3 describes our key management policies and quantifies system overhead. Overhead is studied in terms of both the number of encryptions and the number of packet exchanges required. Section 4 explains how our key agreement protocol removes cloned nodes and keyservers from the network. In Section 5 we show the power consumption overhead for encryptions and wireless communications incurred. We analyze the security of this approach and show how it can be used to counter common attacks in Section 6. We conclude in Section 7 with a summary of our approach and its viability.
The approach we present uses two separate tree structures to organize communications among the nodes in the multicast region:
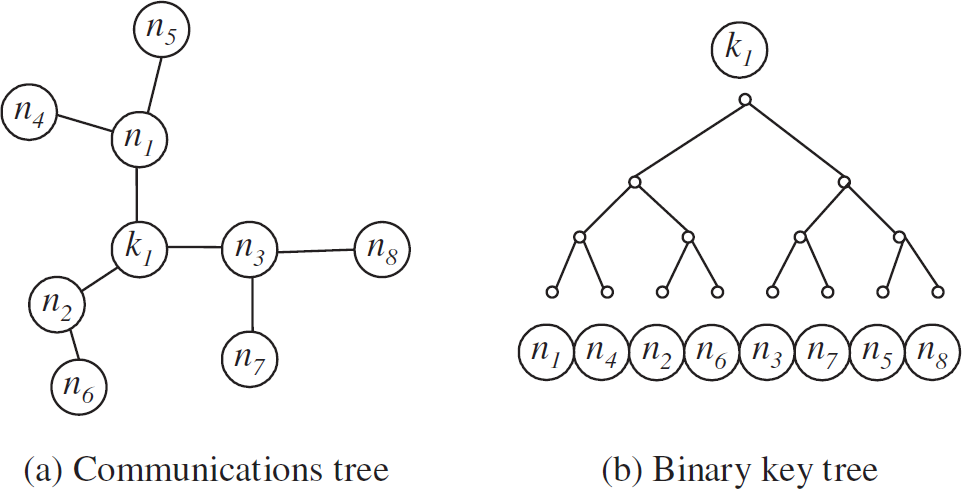
Tree structures (Communications tree and binary key tree).
To avoid confusion, we will use these terms throughout the article to distinguish between these two structures.
The work presented here builds on the results [12] that provide optimizations for group re-keying in
multicast environments. In this approach, the multicast keys are managed using a rooted multicast
key tree [10, 11]. Each sensor node is associated with a leaf node on the
key tree. All nodes attached to the key tree share a common symmetric key for encrypting/decrypting
data. The data encryption key and a set of key encryption keys are managed by a unique keyserver
node. Each of the
The keyserver solicits every node within
The first step in our approach is determining the membership of each multicast region by choosing
the keyserver. To determine the number of keyservers
Using our approach, there is the threat that network security could be compromised if malicious
nodes collude to be chosen as keyservers. They could then undermine the keyserver election scheme
and skew the process to favor the election of malicious nodes. We avert this possibility by using
the secure selection scheme in [16].
This selection scheme ensures that all nodes have an equal chance of becoming a keyserver. When
selecting the keyservers (cluster head in [16]), each node: Generates a random number Calculates a hash value from the number Broadcasts the hash value to the participating nodes. This commits the node to its number without
revealing its value. Waits an an agreed-upon time-out period for every participating node to broadcast its hash
value. Broadcasts a list of all nodes that have transmitted hash values. Matches the lists it receives to its local list and requests a hash value from any missing
node. Waits on an agreed-upon time-out period, and then broadcasts its random number. Verifies the random numbers against pre-committed hash values to ensure integrity.
The key server is then chosen using an agreed-upon criteria based on these random numbers. For
example, the node whose id satisfies (1) becomes the keyserver. 
where
The second step of the process is creating a binary key tree structure rooted at the keyserver.
We use this binary tree structure to manage a set of KEKs that are used when refreshing keys to
guarantee the security of the new keys. Let
We construct the key tree by using a two-pass protocol, where phase creates an initial tree and phase groups nodes to assign tree nodes to sets of physical sensor nodes.
Initialize Each node not in the tree Repeat step 2, (
Assign any leaf node of the tree Count the number of siblings of if (even) group parent with if (odd) do not group parent node group all siblings and
Remove nodes that were grouped in step 2 from consideration and repeat steps 1 and 2 until all
nodes are grouped. (The iterations group nodes 8 & 9, 10 & 3, 11 & 12, 2 & 4 as
shown in Fig. 3c.) Fuse grouped nodes into single nodes, reconstruct a balanced tree of the fused nodes and repeat
steps 1, 2 and 3. (Fig. 3d shows how nodes
5, 1, 6, 7 get grouped.) Repeat step 4 until only one node exists in the initial tree. Construct the key tree according to
the grouping of nodes at every iteration in step 4. (Further iterations group nodes 8, 9, 10, 3 into
one group and 11, 12, 2, 4 into another finally to form the binary tree as shown in Fig. 3e.)

From the ad hoc network (a), we create an initial tree (b). We group nodes (c and d). The result is a binary tree (e) that groups nodes by the keys they will have in common.
Figure 3 shows how to construct a binary
key tree from the ad hoc network cluster. This protocol creates an efficient tree for key management
within the multicast group. An
If 
The grouping of nodes 
For example, consider the two leftmost leaf nodes on the binary key tree
Our protocol is a heuristic that provides good results in most cases. Some simulations found multiple trees with equal numbers of message-hops to every node. For the cluster of 10 nodes in Fig. 4a, our protocol gives the binary tree as shown in Fig. 4b. Another possible configuration is shown in Fig. 4c. However, we see by counting that both Fig. 4b and Fig. 4c require 82 message-hops. This is calculated by:

Example solutions to the tree generation process.
Key management is performed by the keyserver, which coordinates the following activities: Initial keying. Every sensor node elects the keyserver in a distributed and secure manner by the scheme in [16]. The keyserver establishes a unique
private key with each member of the multicast group using Shamir's protocol [13] which sets up a shared key over an untrusted channel by
exchanging 3 messages. The keyserver then generates a key-encryption key (KEK) for pairs of nodes
each at level (log Member ostracism. If a single node is found to be insecure [18], a new multicast key is created and sent to the rest of the multicast tree. If node
Member join operation. A join operation is a request from a sensor node to join the cluster. It is not efficient to
re-key the entire tree to perform a single join. Instead, the new sensor node is attached to leaf
nodes without siblings when they are available. If
Group Agreement Protocol
Random key predistribution security schemes are well-suited for use in sensor networks due to their low overhead. However, the security of a network using pre-distributed keys can be compromised by cloning attacks. Chan and Perrig [4] explain how clones can falsify sensor data, extract data from the network, and/or stage denial of service attacks.
In this section, we expand the approach in [18] for detecting cloning attacks on sensor networks using random key predistribution. In that approach, clone detection is done by a central authority outside the network. We show here how this process can become an organic (in military usage) part of the network.
Each sensor node makes a counting Bloom filter of the keys used by its neighbors to authenticate themselves [18]. A Bloom filter is essentially a hashing function that supports membership queries. Counting Bloom filters provide information on the number of times an element exists in the set. For our purpose, Bloom filters simultaneously reduce the volume of data transmitted and avoid sending key values over the network. Each keyserver collects key usage statistics within its cluster. Equations that define threshold values for cloned key use in sensor networks can be found in [18]. If a key is used more than the threshold value, sensor nodes authenticated by using that key are assumed to be cloned. Since counting Bloom filters are transmitted within the cluster, any keyserver can only recognize the keys within its key ring. Hence, a second round of message exchanges between keyservers is necessary so that the key usage for every key is available to every keyserver.
The threshold for the number of times a key is used for authentication is based on the
probability that two nodes share a key and the probability that they share a connection. The
expected number of times a key is used for communications in the network is: 
with variance: 
where
We determine whether or not a key is cloned by comparing
If any keyserver turns out to be subverted, it gives rise to a problem similar to the Byzantine Generals Problem. Barborak [19] provides a survey of related research that contains algorithms for forcing agreement as long as well-known criteria (described in Section 4.1.4 of [19]) are satisfied. By applying these algorithms, our group key agreement protocol can ensure security as long as less than one-third of the keyservers are compromised.
Since compromised nodes may incorrectly report key usage statistics and adversaries may collude to cause legitimate nodes to be detected as cloned nodes and ostracized from the network, our group agreement protocol must be immune to internal subversion. The protocol in Section 4.1 reaches agreement on the set of cloned keys and can tolerate subversion of less than 1/3 of the keyservers. The limit of 1/3 is the theoretical bound on distributed consensus in the presence of malicious parties [19].
To reach consensus on the set of cloned keys in the network: Each node transmits to its keyserver the counting Bloom filter for the keys used by the node. The keyserver transmits the counting Bloom filters from all the nodes within its multicast region
to every other keyserver using an authenticated channel. These channels are established using
Shamir's 3 pass protocol [13]. Every keyserver now has counting Bloom filters for every multicast region. Each keyserver
computes key usage statistics for keys in its key ring to identify cloned nodes. The keyservers use a Byzantine agreement protocol [19] to reach consensus on key usage statistics. The protocol
from [20] comes to a correct consensus
as long as less than one-third of the keyservers are faulty or compromised. It also degrades
gracefully as long as fewer than The keyserver computes a vector The vector v is sorted, and the lowest and the highest The key usage value is the mean of the vector This protocol is guaranteed to be correct when
Suppose that the system is designed to tolerate up to
A secure private key has to be established between every pair of keyservers to exchange the
compressed counting Bloom filters. Using Shamir's 3 pass protocol
Total number of messages for group agreement =
Message Overhead and Power Consumption
We now compute the number of encryptions, messages, and hops required by our approach. We denote
the key associated with the
The results tabulated in Table 1 for
system overhead for every membership operation are derived below. Initial keying.
At level (log
At level (log
Let Member ostracism.
(log
For the replacement of (log
Each message must reach a subset of nodes within the cluster which consist of all leaf nodes
associated with the new KEK. The session key at level 0 (K
Member join operation.
When a node joins a leaf node, it creates an extra parent node and a KEK associated for that
node.
As the case for encryption, we require 2 messages to transmit that KEK. Also, the new node should
establish its private key (3 messages) and receive existing ((log
Number of hops: Since the join occurs on any of the members less than

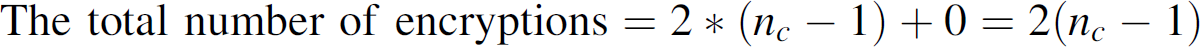







Overhead for group membership operations

The overhead calculations for the number of encryptions and messages are of the order of the
multicast region size (
The StrongARM 110 processor consumes 108 nJ for each 128-bit operation [6]. The StrongARM consumes 12 times the energy of the ARC-3 [6]. Hence the power consumption for a 128-bit operation on ARC-3 can be estimated as 9 nJ.
Power consumption for network initialization

RSA encryption roughly requires 7,056 128-bit operations and decryption requires 145,408 128-bit operations. Therefore, RSA requires 5.36 mJ to encrypt a message of 900 bits and decryption consumes 110.42 mJ on StrongARM 110 processor. RSA encryption on ARC-3 requires 0.45 mJ and decryption 9.20 mJ.
AES requires less energy than RSA. AES encryption and decryption overhead is nearly identical.
Encrypting 900 bits on a StrongARM processor would require 15.3
Our protocol requires 2(
Transmission costs are usually 1.5 times the energy required for reception. The energy consumed by idling and receiving data is nearly identical. Assuming that only transmission requires extra energy, we estimate the cost for transmitting 900-bit messages within a range of 50 meters. Radio communications using Bluetooth expend 10−7 joules per bit for transmission.
Private key establishment with each sensor node requires two message transmissions by the
keyserver and one by the sensor node. Each sensor node receives two messages and has to transmit
one. Also, for each KEK in the binary key tree other than leaf nodes, the keyserver transmits two
messages and every sensor node receives log
Table 2b tabulates the total power consumption for transmission and reception during key initialization.
Thus for a sample network of 100 nodes scattered in unit square with a communication radius of
0.2, the ideal cluster size [14] is a
2-hop radius containing 26 nodes on an average. Assuming AES encryption on ARC-3 processor, the
keyserver consumes 28
ColTraNe [21] is a surveillance application that tracks military targets using a sensor network. We use the data collected from our field test of this network to estimate the power overhead required by our approach. Our multicast approach requires fewer encryptions and less energy consumption than pair-wise keying approaches. One tracking method used in the field tests required 911 packets to be exchanged between 70 sensor nodes. A pair-wise keying approach would require one encryption per packet to securely transmit the data. AES encryption on a MC68328 Dragonball processor requires 205.68 mJ energy to encrypt the 911 packets that contain a total of 254,552 bytes of data.
Our multicast approach requires fewer encryptions. In the worst-case each packet would have to be encrypted for all 12 multicast regions. This would require only 95 encryptions. The total power consumption for encrypting data drops to 17.76 mJ. A more detailed analysis of these results is available in [14].
Applications need to guarantee that adversaries cannot subvert the sensor network, and our approach can be used to neutralize many important classes of attacks. In Byzantine attacks malicious nodes try to force disagreement among legitimate nodes. In Sybil attacks [22] compromised nodes try to maintain multiple identities. This can be used either to stage Byzantine attacks or drain power from legitimate network nodes. Cloning attacks create multiple copies of legitimate nodes. They can disrupt a network by inserting false detections, dropping packets, modifying data, and eavesdropping. In this section we describe these attacks and show how they fail against our multicast encryption infrastructure.
Byzantine Attack
In a Byzantine attack, a compromised node forwards manipulated information to cripple the
decisions of legitimate nodes and, in certain cases, also to influence the result. Assume that a
cloned node
Consider a network of
Sybil Attack
The Sybil attack [13, 22] is an attack on a network where one compromised node acts as multiple nodes (i.e., has multiple identities.) For example, multiple Sybil identities can drain resources from legitimate nodes by sending spurious traffic. Alternatively, Sybil nodes can skew voting algorithms, like the Byzantine Agreement. Sybil attacks are known to affect routing, data aggregation, and detection of cloned nodes in sensor networks. Our approach counteracts these attacks, since they make it easier for the compromised nodes to be identified.
In the case of a Sybil attack, a compromised keyserver reports the existence of multiple keyservers. This leads to an increase in the density of reported keyservers. We have a prior threshold on the density of keyservers in the sensor network. Since the keyservers are selected at random, their density should remain within a predictable variance from the mean. A Sybil attack will increase the keyserver density when the multicast region is contained entirely in the field. Alternatively, compromised keyservers can report a region outside the regular field to create Sybil nodes without changing the node distribution. To counter this, it is advisable to restrict deployments to predefined regions.
The key usage statistics will also support the detection of the Sybil nodes. Since the Sybil nodes require its keys to be used multiple times, they quickly fall into the category of suspicious cloned nodes that will be ostracized by the network.
Consider a network of 1000 nodes spread over unit area with 100 keyservers picked at random.
Hence, the average density of the nodes is 1000 and that of the keyservers is 100. Assume a node
located at location (0.1, 0.1) is a Sybil node. It reports the false existence of 6 keyservers
around it, within a range of 0.1. Hence the density of the keyservers around the Sybil node
increases to 6/(
Cloning Attacks
In a cloning attack, the adversary fills the network with copies of compromised nodes. The cloned nodes then launch a variety of attacks ranging from forwarding erroneous data to manipulating the messages in the network. It also attempts to drain other legitimate nodes of its limited power. Our previous work [18] shows that by using statistical analysis of the key usage in the network such clones can be easily detected. They can be ostracized from the network by discarding the keys used by that node. A key that is used very often indicates unusual activity by the nodes using it.
Each node transmits a counting Bloom filter of the used keys. The keyservers come to a consensus on which keys are cloned on the basis of pre-defined thresholds. Any key that is used more than a given threshold times is a candidate to be a suspected cloned node. If the mean usage and variance of a key is above the specified threshold, the keyserver calculates a confidence on the suspected cloned key. The cloned nodes are removed from the network by terminating all connections that use the set of cloned keys.
Simulations on a 250-node network support the predicted equations. With a key pool size of 1000, each node randomly picking a key ring of 50 keys and with an assumption that 10% of the keys are already cloned, analysis predicts that any key used more than 100 times on average indicates a cloned node. Simulations showed that cloned nodes used the same keys an average of 100 times. In a network of 250 nodes, if there are at least 20 clones, the cloned nodes can be detected with a false positive rate of 70%.
A re-encryption of only log
Conclusions
In this paper we present a fully distributed approach to sensor network security. The proposed approach allows the network to organize itself into a set of security zones. We have shown how to organize and maintain the security regions. In doing so, we quantified both the energy savings attained and showed that the approach is able to tolerate many classes of attacks.
We start with an
We use a secure selection scheme to randomly select the keyservers. The keyserver nodes establish local multicast groups using the protocol described in Section 2. This approach has no single point of failure and is resilient to collusion among nodes.
The key agreement protocol presented in Section 3 secures the network from cloning attacks and internal corruption. Keyservers use a Byzantine agreement protocol to identify and ostracize compromised nodes. Group key management reduces the network overhead due to encryption and message exchanges, which results in significant energy savings. We use statistics from standard commercial hardware to quantify the energy savings provided by our approach.
Our approach uses key usage statistics to detect cloned nodes. This keeps the false positive rates within manageable bounds. If the number of clones is below this threshold, they will not be detected. This means that applications that use our approach need to be designed to tolerate inputs from a small number of malicious participants.
Further research is desirable in developing more efficient protocols for two portions of the
proposed framework. The first aspect is keyserver selection. The current approach requires
O(
