Abstract
It may be surprising that one of the most popular compensation schemes in business is so open to being hacked – to having managers cheat to win. We explore tournament theory to detail its vulnerabilities to various forms of cheating unilateral and multilateral. We identify who is most likely to be involved and under what conditions. We describe the costs to the victims, to the firm, and to society. We outline the possible strategic effects – in terms of firm performance. And, we discuss possible ways to address these vulnerabilities to the schemes we rely on to motivate managers to put in the right efforts, to take the right risks, and to lead the right way.
A firm's choice of its compensation scheme is strategic because it affects performance through how well the interests of its manager-agents align with those of its owner-principals. The structure of that compensation determines whether managers put in the optimal level of effort and take on the proper amount of smart risks (e.g., Bloom and Michel, 2002; Hvide, 2002; Tekleab et al., 2005). Compensation schemes vary in form, and in associated benefits, costs and risks. For example, when worker monitoring is free, an effort input-based scheme is efficient; however, outside of that often unrealistic ideal, alternative schemes may provide better results. One such alternative is the tournament compensation scheme, as described by Lazear and Rosen (1979), where managers compete for rank-order prizes and monitoring is minimized (i.e., only the relative outputs of the competitors are necessary to measure). Our research question in this paper focuses on as-yet-hidden flaws in that popular compensation system; specifically, we inquire as to whether tournament schemes are susceptible to fraud. We expose the vulnerabilities of tournaments to cheating – through both unilateral and bilateral deception – and describe the related impacts and implications to affected and relevant parties.
The analysis of such ‘hacking’ of compensation systems is important to do, especially for the tournament scheme. Tournament-style compensation is popular, especially in western economies – as seen in its application to business, sports, entertainment and other activities where ‘winning is everything’ (e.g., Frank and Cook, 2013; MacDonald, 1988; Rosen, 1981). 1 It remains the standard compensation system for top management positions in Fortune 500 firms. It is an attractive system on paper for many reasons (e.g., Becker and Huselid, 1992; Kaleet al., 2009; Leeet al., 2008; Pissaris et al., 2010): First, it is as efficient, theoretically (e.g., in expected value terms for all participants), as a perfectly monitored piece-rate scheme. Second, it requires much less information to implement, which is important when monitoring efforts are costly; it needs only one measure – that of the relative output of the competitors – to implement. Third, for real participants, it induces sufficiently more risk-taking from managers to benefit most firms. Fourth, in real labor markets, it tends to provide a advantageous self-selection effect to filter for more confident, talented and risk-taking managers who enjoy competition. Fifth, it is fairer to managers than alternative systems when the firm is exposed to significant external uncertainties. That said, it is also a compensation scheme that entails different costs than alternatives like the piece-rate system; for example, it is does not provide a ‘fair’ realized (versus expected) outcome under a ‘tie’, it leads to and rewards an unequal distribution of wealth, and it encourages competition over cooperation (e.g., Bloom, 1999; Fredrickson et al., 2010; Pfeffer and Langton, 1993).
However, such a competitive approach has been associated with significant negative outcomes, such as the recent widening gaps between rich and poor (e.g., Piketty, 2014), and an unfriendly win-at-all-costs mentality in what were previously considered respectful arenas of fair-play (e.g., Kräkel, 2000; Main et al., 1993; Messersmith et al., 2011).
The ‘regular’ benefits, costs and risks of the tournament are well-understood; as are some of the
While no other paper has analyzed the hacking of the tournament model in the specific way we do here, there exists significant related research. (Note that we do
So, there has been a strong interest in the vulnerabilities and in the potential negative effects of the tournament model, and we complement and add to that literature with a comprehensive analysis of how the original model can be hacked – one that reveals new vulnerabilities. Specifically, we do so by analyzing the impacts of an added assumption about a manager's access to output information prior to the firm's access to it. This type of analysis – one that goes off the equilibrium path and examines the harms of the successful cheating of institutionalized systems – is even more important now, especially in light of the growing unease about corruptive practices and the costs to industries and nations when their organizations use systems that allow cheaters not only to prosper with monetary rewards but with power as well. Analyzing how people (and collections of people) cheat what are thought to be reliable and fair systems of competition is important because of its effects: on business – in terms of where managers decide to put in efforts (e.g., in cheating or in fair play, with the former most often more harmful and long-term inefficient to society given it builds distrust and backbiting), and in terms of the costs to stakeholders when cheating firms are exposed (e.g., Enron, Worldcom, Arthur Andersen, Madoff, Theranos, and so on); on politics – relating to who wins elections and is able to make, change and implement laws that could pardon past wrongdoing or further harm victims; and, on society – in terms of our trust in each other and our institutions, especially as influencing our willingness to cooperate with and invest in each other's businesses (which are actions that produce the main synergies powering our economies). The more we know about these systems and their hackability, the better can understand what can go wrong and how to preempt and fix them.
Tournament theory primer
We begin the analysis of cheating in the tournament system by describing ‘tournament theory’ in its most basic form as laid out by Lazear and Rosen (1979); that basic form provides a solid foundation for the rest of the analysis. So, we start with an economics-based, mathematical, formal model and then shift to less-formal, descriptive logic to analyze the cheating possible in the modified basic model. We do so because the economic model's formality efficiently and clearly sets up the basic system and its main variables, including the ones we focus on (e.g., the level of uncertainty as measured by the variance in managerial outputs) that allow the analysis of cheating when the new, realistic assumptions are added to the base model. This exposition style is both fair to the original material (i.e., by summarizing it in its own language) and appropriate for the business audience (i.e., by explaining the main analysis in less formal, more descriptive and realistic terms once they have been introduced to the that original material 2 ).
We do not think that keeping the economics-based formality is appropriate for the entire paper. One reason is that standard economics analyses require calculating equilibria when
We start with the Lazear and Rosen (1979) paper because it provides a simple-but-generalizable model that focuses attention on the most important factors and issues. In this model, there are two managers vying for first and second prize in the tournament being held at the focal firm. There is one main period of action in which they make decisions –a period that is preceded by the firm choosing the two tournament prize levels, and followed by the firm choosing the winner and awarding the prizes. The actions of the two managers involve mainly the choice of their effort-investment that they each voluntarily make in the tournament, but may also include other items like posting a bond to enter the tournament (e.g., depending on the prize levels chosen). Each manager 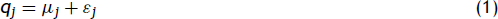
Each manager's effort investment is produced at an increasing cost
For comparison we can consider the piece-rate compensation scheme under free monitoring costs. In that case, the outcome is efficient. Firm output settles at the point where societal marginal benefits just equal manager marginal costs (and firm-owners make no profits in the competitive market), so that:

With the comparison outcome set, we can now return to the tournament outcome illustrated with our (generalizable) two-player competition over two prizes – 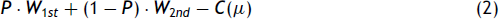
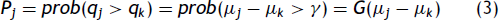
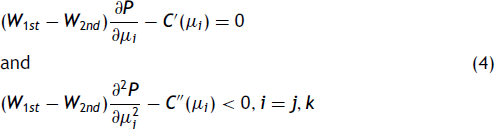
Each manager chooses effort to maximize expected utility, and with an interior solution assumed,
3
this gives:
Lazear and Rosen (1979) provide the explanation justifying the traditional interior solution assumption and describe the conditions when an interior solution does not occur.
We assume Nash–Cournot optimization where each manager optimizes against the optimum choice of his opponent, which leads to the reaction function for manager 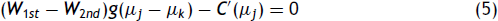
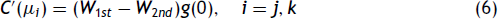
The assumed symmetry of opponent actions under a Nash solution gives μ
Substituting equal effort into Eq. (5) gives:
The firm's revenue is (
Now, substituting (7) into (2) and setting 
The firm sets the equilibrium prize levels to optimize (8), and that guarantees marginal benefits equal marginal costs:
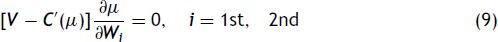
Some additional manipulation of the equilibrium conditions identifies the prize levels as:
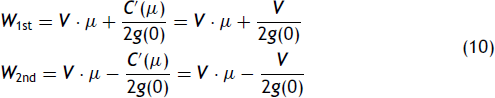
To illustrate further, assuming a Normal distribution of the random factor, equation (10) describes how the optimal prize spread settings vary directly with
For the remainder of this paper, we keep the model at this level of description, even though tournament theory has been developed and been further complicated to reveal other interesting effects, like that such schemes attract managers who are less risk-averse and better endowed, and that it is a preferred scheme when certain types of measurement errors exist in the economy. This present level is sufficient to make our points about this scheme being vulnerable to cheating in a simple and generalizable way. From here on we switch from formal economics language to a more descriptive argumentation because we will not be talking about standard economic equilibria analyses, but instead examining off-equilibrium paths where deception can occur, where the implications are meant more for a business rather than an economics audience.
Hackability and its effects
Tournament-style compensation schemes involve
Hacking the ideal model
To begin our analysis of the opportunities to cheat, we consider the original base model, as described above,
However, what if there were other ways to boost output – options not considered in the base model? For example, the manager could seek to boost his own output by obtaining output from others (a practice not uncommon in business, for example, when managers take credit for the output of underlings). Consider the benchmark case when he pays the market price
Now consider that there may be other ways to boost a manager's output, some possibly having a marginal cost below the
Such possibilities have all occurred in the real world, even under the ‘reasonable’ levels of monitoring that occur in sports tournaments and tournament-like rivalries between firms. Within a firm, where monitoring is lower because it is costly and, hence, a good place to use a tournament scheme, such possible cheating is obviously possible as well, in addition to being harmful. If the cheating is successful – i.e., the cheating manager wins when he would have not otherwise – then there are victims. There is the cheated rival manager, and there are likely other victims as well, such as the firm and others who did not promote the best manager or who were put in unsafe conditions due to corners being cut, and so on. Given that harmful cheating is possible even in the base case, it is worth investigating in more realistic cases and across all of the main variations of cheating by the parties involved; and we do so, all in one place, as a contribution to the literature, below. We refer to the same base model, the same main methods of boosting output, the same manipulatable factors (e.g., effort) in doing so, but with one main addition in the assumption of who knows what when, an assumption we argue is realistic in most business contexts.
Hacking a more realistic tournament model
We now consider cheating in a more realistic version of the tournament, beginning with the simplest case, a case that does
The timing of the manager's checking on his output is important. If it does not increase over the span of the contest, the manager would rather wait as long as possible to check the output in order to remove as much of the randomness in the effort-to-output function as possible. That way, he has the most accurate reading of the final output level without cheating – a level he can then use to best decide if and how much he should cheat. If we assume that the randomness effect is uniformly distributed across time, as is the manager's main effort, then waiting until very close to the contest's end is optimal timing.
To be clear, we are assuming that the manager can only observe his own output and
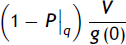
This new assumption – where the cheater observes his own output level prior to it being judged by the firm – is important because it alters the probability distribution driving the marginal benefits of cheating,
The prospect of higher marginal benefits opens up many possibilities for boosting output because the marginal costs of such can be at the level of
Fig. 1 illustrates the band of cheating activity expected for a symmetrical pdf. The limits of the band are defined by the original – higher-variance –
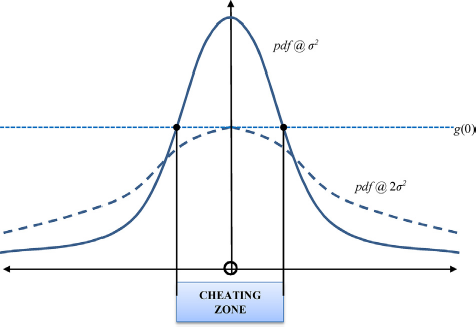
The bookends of the cheating regime.
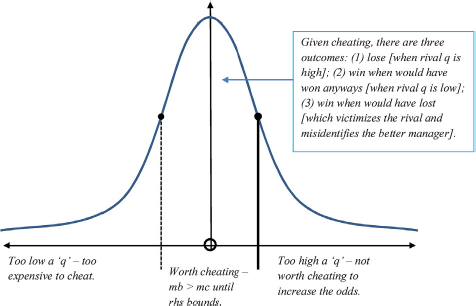
The outcomes of cheating.
We have established that with a small change in assumptions the opportunity for cheating exists for a typical pdf – one with an increasing ‘value at the mean’ under lower variance – and that the cheating range will increase with pdfs that are more sensitive to changes in variance. That is a significant
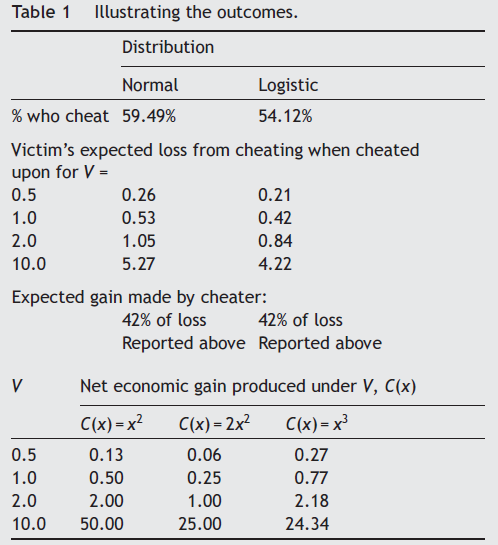
59.5% of managers will cheat, and, of those:
○ 20.3% will lose regardless;
○ 79.7% will win, made up of:
50% who would have won anyways; and,
29.7% who would have lost.
In other words, by cheating, the manager increases his chances of winning by about 30%. 6
These statistics were calculated by using the Normal distribution, comparing its pdf under a mean (μ) and variance (2σ
2
) with a pdf under the same mean (μ) but with half the variance (σ
2
); for example, the cheating range is located from the two intercepts of these pdfs, then the cdf between the two intercepts provides the percent of the total within that range. Similar calculations can be done for a distribution based on the range identified [e.g.,outside that range to the right is where the rival would win despite the cheating actions of a cheating rival].
The act of cheating generates several inefficiencies and unjust effects: The victimized manager loses an expected amount of ‘
The cheating manager increases his expected income by the amount of about ‘(0.221) ·
We have only considered the case of one of the two managers cheating thus far, as it was the simplest case. What happens when they both cheat? If neither knows that the other is cheating, then the one-manager case that we have outlined predicts when each will cheat but not who will win nor who gains and who loses. It terms of expected values, both managers will lose in costly output boosting investments that cancel each other out (on average) with the firm gaining from the added outputs. If both managers know that the other can cheat then neither will put in any initial effort, and then they will make the least cost investments in output boosting (i.e., cheating) up until marginal costs equal marginal benefits, and depending on their then-known random effect level under the new pdf. Assuming symmetry in expectation, neither manager will gain and both may lose by making investments (as these are likely to exceed base model effort levels, but with unspecified cost functions), but the firm is likely to gain because the tighter variance should increase outputs. Of course, if both managers know the other is cheating, then it is likely that the firm does as well. And, when all parties know that cheating is likely then a new contract will be generated based on that shared knowledge and the reduced variance. It is likely to produce an efficient outcome much like the original base model.
Illustrating the outcomes.
Hacking the alternative model bilaterally
We have described how a realistic (i.e., slightly altered in assumptions) tournament model can be cheated unilaterally. We now consider bilateral cheating opportunities, where two parties collude to cheat a third. There are two types of bilateral cheating, each with variants: (1) where the cheating manager and the firm conspire to cheat the other manager; and, (2) where the two managers conspire to cheat the firm.
Case 1a – Bilateral cheating agreed to ex ante
Here, the cheating manager and the firm conspire after the victim-to-be manager has signed up to compete in the tournament but before the cheating manager does any work. The scam here involves agreeing to split the expected difference between the victim-manager's output and his ‘fixed’ losing prize. In this case, the cheating manager sells off his output in the free market and does not take the winning prize (leaving it to the firm), while the firm tells the victimized manager that he lost the tournament. In this case, because each conspiring party is ‘guaranteed’ an expected benefit, 100% of managers and of firms have the motivation to cheat in this manner. (Nash-type bargaining, based on the numbers of alternative cheaters available, should determine the split of the expected rent-shifted gain from the victim of the amount ‘
Case 1b – Bilateral cheating agreed to ex post
Here, the cheating manager and the firm conspire only after the work has been done by both managers but prior to the awarding of the prizes. The cheating manager approaches the firm with his verifiable output with an offer to award him the winning prize in return for a side payment. We assume at that point neither party knows the other manager's output. For simplicity, we further assume that the cheating manager cannot adjust his output prior to presenting his offer to firm.
8
The possible benefit to the cheating manager emerges from being guaranteed the winning prize, while the cost to do so is the size of the side payment made to the firm. Thus, the expected increase in gross benefit to the cheating manager is:
There are several sub-variants of bilateral cheating that can occur, for example, where parties have access to private information that can be used to manipulate the co-conspirator. Such cases require further assumptions and further complexities for the model. We present the simplest case here because our point in this research paper is to reveal that cheating is possible, both unilaterally and bilaterally; the purpose is not to depict the every possible variant of the main types of cheating for a tournament compensation scheme. We leave the latter exercise as future work.
Several observations from this condition and case can be noted: For any level of the cheating manager's output,
Cases 2a and 2b – Bilateral managerial cheating agreed to ex ante
In these cases, the two managers collude to cheat the firm. As before, we assume that neither manager can verify the other's output prior to it being verified by the firm (because it is private information that is costly to monitor and, therefore, to verify). We also assume that the offer to cheat is made prior to work being done by either manager. There are two cases to consider – (a) when managers cannot sell their excess output on the open market without being observed by the firm; and, (b) when they can.
In Case 2a, there exists an instability when such collusion is attempted
The content of the contracted side-payment could consist of each manager posting a bond of half the difference between the two rewards, where the deemed winner (assumed verifiable by a third party) then must transfer the bond to the deemed loser (with the deemed loser retaining their own bond). This would be enforceable because it is not illegal (as it does not violate the standard terms of the tournament contract or of criminal law), and the trigger is verifiable. (The contract does not need to include bonding, but it does ensure a smooth transaction of payment between colluding parties.) An example of such a side-payment scheme between two agent parties who are supposed to be competing for a prize from a principal but who instead collude to cheat that principal occurs in bids for road projects (and in other procurement auctions) in the US (e.g., Bajari and Summers, 2002; Bajari and Ye, 2001). The first firm pays the second to submit a non-competitive bid in exchange for a side payment; the first firm wins the bid at a sufficient profit margin to pay off the second firm and still enjoy high profits itself, while the government agency (and taxpayers) lose. Such side payments may be in the form of a contract or ‘bonded’ by reciprocation over time among the ‘competing’ firms. Such a scheme is akin to the one described in this paper where two competing managers collude through contracted side-payments to cheat the tournament holding firm (by reducing their efforts for the firm).
In Case 2b, where managers can sell their excess output on the open market undetected, they put in efficient efforts and then choose whether to sell their excess depending on seeing their own output level,
Discussion
We have proven and detailed that under limited and realistic additional assumptions to the base model – involving self-awareness and imperfections in monitoring – that unilateral and bilateral cheating is likely to occur in a tournament. Our results are important because they constitute a new revelation that exposes potentially significant costs arising from a common business compensation system. Such a revelation appears to feed the sense of injustice at many workplaces, and then in society more widely, regarding the questionable division of economic classes often based on small and possibly even fraudulent differences in actual talent and effort. If significant opportunities for cheating can occur in this relatively simple model, then what does that entail for real, complex, poorly overseen compensation and tournament systems used in businesses, governments and other institutions? What does it mean especially when so many of these rank-based systems entail no oversight other than verifying that the process ‘looks right’ in terms of having the expected process steps, when no actual checks are done on whether those processes are hackable – e.g., that garbage in is not producing garbage out. 10 It may mean that the wrong people and firms are winning, that the right people and firms are losing. It may also mean that competitive advantage may arise from either being a hacker or by being able to design unhackable systems, including those controlling compensation.
Of course, we need not look far to see how such systems have been violated in our business school rankings, our publication processes and our accreditations – COPE, AACSB, Princeton Review and other oversight agencies do not actually conduct any investigations into cheating, although they provide ‘cover’ for their members to the naïve public that everything is fine when it may not be.
Regardless, the hacking of trusted reward systems is an important phenomenon that deserves further investigation. We have witnessed cheating under various compensation schemes, including tournaments, from high-stakes sports (e.g., cycling, soccer, baseball, racing, and so on) to high-stakes business (e.g., VW, Enron, Xerox, Theranos, Wells Fargo, Bre-X, Siemens, HealthSouth). Readers have probably even suspected it when participating in their organization's own tournament compensation schemes (e.g., seeing corner-cutting, misreporting, overzealous projections, taking credit for underlings’ work, sabotage of rivals, and other activities that boost output in dangerous ways). These behaviors are harmful to organizations, to the economy and to society. So, it is important to understand the range of such behaviors (and their effects) that constitute cheating in any commonly applied system, as we have done so here for tournament-style compensation schemes. With that understanding, we can better decide on which reward system is better (accounting for its vulnerabilities) and make informed decisions on how to mitigate the deviant behaviors (e.g., by being able to more accurately trade off the costs and benefits of increased monitoring; by being able to more accurately target the likely times and people involved in cheating; and, so on).
Our analysis has contributed to the understanding of compensation systems by adding to concerns focused on the vulnerabilities of such systems to hacking. We illustrated this using tournament theory. Our analysis has identified the likely cheaters (i.e.,. mid-tier-quality managers), and the damages cheating can cause – which can be significant under specific levels of output value, effort-cost, and random effect variance (or ‘talent spread’). We have described the limits where the tournament is relatively ‘cheat-proof. We have identified the main types of cheating that are likely to occur – i.e., where there is the opportunity and motivation to do so. We have described the main statics of the relevant conditions – e.g., where cheating is expected to increase with output value and noise (i.e., the variance in luck). We have provided illustrations of the costs to the victims, to the firms, and to society when cheating occurs. We note two more related concerns now to round out the more realistic effects of such fraud: (1) that the wrong winner is identified and may then move forward in the next round of competition, adding a further inefficiency to the system; and, (2) that the wrong message is sent to the firm and society that in fact cheaters do prosper, feeding a possible vicious cycle in such destructive actions (e.g., think about the steroids era in sports).
The natural question that then arises is whether such fraud can be stopped, especially in situations where monitoring is normally too costly, or is practically or legally impossible. The answer is that maybe it can be mitigated with a penalty system of big fines based on spot-checks, whistle-blowing, and focusing on unusual patterns of managerial behavior, to increase the probability of getting caught. Our analysis has identified whom to target and the conditions for when to check, based on factor conditions like output value, luck (or ‘talent spread’), and so on. Also, recall that every cheating action leaves a paper trail – e.g., in the purchase of outside output, in the bonds entered into, and so on – a trail that theoretically could be used as evidence. So, in theory, there may be less of a need to monitor what ‘regular’ efforts are being made by a manager, and more of a need to investigate what ‘unusual’ actions he may be partaking in (and with whom) that would allow cheating to occur – i.e., actions that allow him to alter his output without putting in the effort by exploiting transactions with those who could use or produce such outputs. In other words, monitoring manager network use and the timing of that use may be a better choice than spot-checking day-today efforts and outputs; firms doing so should outperform their rivals.
There are many avenues for future work that could be pursued based on the analysis in our research. We advocate field work on identifying and testing cheating in tournaments – in cases and in lab experiments – to see how and when it is done and to what effect. Field work may also be helpful in determining the counter-measures being deployed by firms and to what extent these are effective under which conditions, and when they lead to better profits. Such findings should be publicized so that more hack-proof compensation schemes can be devised and deployed, and so that the dangers of hackable ones can be made more widely known. We also advocate further analysis into other common compensation schemes to identify whether and how these alternatives can be hacked and what that means for strategic decisions and outcomes.
Although such analyses may be distasteful to some who believe that most people adhere to ethics and laws, it remains worthwhile to discuss the ways in which our systems may be hacked and when they are likely to be hacked – i.e., where there is opportunity, motivation and rationalization to do so (e.g., Cressey, 1973; Howe and Malgwi, 2006). That type of analysis is, of course, pursued with ‘better labeling’ in the agency literature – where people are expected to act with guile in their own self-interests (Williamson, 1975). The point is similar here; we need to design systems that produce the results we want, rather the results we do not when they are hacked. Only by taking a hard look at our systems will we be able to protect our firms, economies and values, and that is certainly worth the attention of our own cunning.
